“Encrypted DNS Implementation Guidance,” a detailed document from the Cybersecurity and Infrastructure Security Agency (CISA), tells government agencies how to improve their cybersecurity by using encrypted Domain Name System (DNS) protocols.
This advice is in line with Memorandum M-22-09 from the Office of Management and Budget (OMB), which lays out a “zero trust” cybersecurity plan for departments in the Federal Civilian Executive Branch (FCEB).
Executive Summary
The document, which was released in April 2024, explains in great detail how federal agencies must meet federal requirements for encrypting DNS data.
ANYRUN malware sandbox’s 8th Birthday Special Offer: Grab 6 Months of Free Service
As required by M-22-09 and 6 U.S.C. § 663 Note, Agency Responsibilities, it stresses using CISA’s Protective DNS feature for all outgoing DNS resolve.
The guidelines help agency network professionals use the most up-to-date technology tools to protect DNS infrastructure.
OMB posted Memorandum M-22-09, the Federal Zero Trust Strategy, on January 26, 2022, to back up Executive Order 14028, “Improving the Nation’s Cybersecurity.”
This plan requires all DNS traffic within FCEB agencies to be encrypted by FY24. The document’s goal is to help agencies use encrypted DNS protocols that align with these zero-trust concepts.
Checklist for Agency Implementation
The advice lists the most important rules and recommended methods for encrypting DNS data and using CISA’s Protective DNS for upstream DNS resolution.
Setting up the agency’s DNS infrastructure to handle encrypted DNS protocols is one of the most critical points.
- Configuring agency DNS infrastructure to support encrypted DNS protocols.
- Using Protective DNS as the upstream provider.
- Disabling DNS Root Hints and other mechanisms that might bypass Protective DNS.
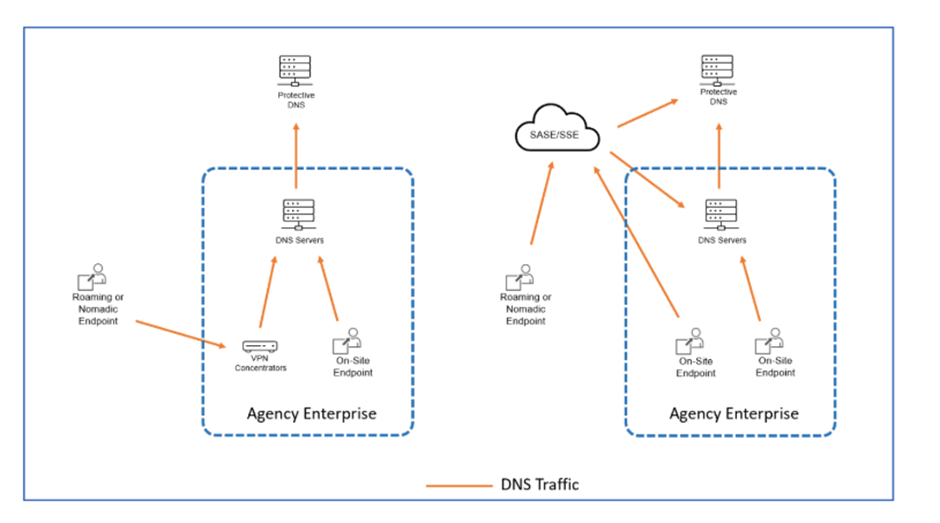
- Configuring SASE/SSE solutions to send all device DNS queries through encrypted protocols.
- Ensuring on-premises and roaming endpoints use authorized DNS configurations.
Phased Implementation
Given the complexity of transitioning to encrypted DNS, the guidance recommends a phased approach:
- Use Protective DNS: Configure internal DNS infrastructure to use Protective DNS.
- Block Unauthorized DNS Traffic: Configure networks to block unauthorized DNS traffic.
- Encrypt DNS Traffic with Protective DNS: Use encrypted DNS when communicating with Protective DNS.
- Encrypt DNS for Roaming and Nomadic Endpoints: Configure endpoints to use SASE/SSE solutions for DNS requests.
- Encrypt DNS Traffic in Cloud Deployments: Configure cloud deployments to use encrypted DNS.
- Encrypt DNS Traffic for On-Premises Endpoints: Support encrypted DNS protocols for on-premises endpoints.
The document gives thorough technical instructions on how to use CISA’s Protective DNS service and encrypt DNS. It
talks about ways to encrypt DNS data, like DNS-over-HTTPS, DNS-over-TLS, and DNS-over-QUIC.
It also talks about how Protective DNS can be used to stop endpoints from resolving malicious names.
Implementation Advice Based on Vendor
Implementation advice for web browsers, operating systems, and DNS servers that are unique to each vendor is included in Appendix A.
It tells you exactly how to set up Firefox, Chrome, Safari, Microsoft Windows, macOS, iOS/iPadOS, BIND DNS Server, Microsoft DNS Server, Azure Private DNS Server, and Infoblox DNS Appliance so that they can handle encrypted DNS protocols.
The “Encrypted DNS Implementation Guidance” from CISA is very important for government agencies that want to improve their security by using encrypted DNS protocols.
Even though it’s mostly for FCEB agencies, other groups may find it useful for zero-trust attempts. The guidance paper is marked so that anyone can see it and share it without any problems.
Free Webinar on Live API Attack Simulation: Book Your Seat | Start protecting your APIs from hackers