CISA is warning that a critical Citrix ShareFile secure file transfer vulnerability tracked as CVE-2023-24489 is being targeted by unknown actors and has added the flaw to its catalog of known security flaws exploited in the wild.
Citrix ShareFile (also known as Citrix Content Collaboration) is a managed file transfer SaaS cloud storage solution that allows customers and employees to upload and download files securely.
The service also offers a ‘Storage zones controller’ solution that allows enterprise customers to configure their private data storage to host files, whether on-premise or at supported cloud platforms, such as Amazon S3 and Windows Azure.
On June 13th, 2023, Citrix released a security advisory on a new ShareFile storage zones vulnerability tracked as CVE-2023-24489 with a critical severity score of 9.8/10, which could allow unauthenticated attackers to compromise customer-managed storage zones.
“A vulnerability has been discovered in the customer-managed ShareFile storage zones controller which, if exploited, could allow an unauthenticated attacker to remotely compromise the customer-managed ShareFile storage zones controller,” Citrix explains.
Cybersecurity firm AssetNote disclosed the vulnerability to Citrix, warning in a technical writeup that the flaw is caused by a few small errors in ShareFile’s implementation of AES encryption.
“Through our research we were able to achieve unauthenticated arbitrary file upload and full remote code execution by exploiting a seemingly innocuous cryptographic bug,” AssetNote researchers explain.
Using this flaw, a threat actor could upload a web shell to a device to gain full access to the storage and all its files.
CISA warns that threat actors commonly exploit these types of flaws and pose a significant risk to federal enterprises.
While CISA shares this same warning on many advisories, flaws impacting managed file transfer (MFT) solutions are of particular concern, as threat actors have heavily exploited them to steal data from companies in extortion attacks.
One ransomware operation, known as Clop, has taken a particular interest in targeting these types of flaws, using them in widescale data theft attacks since 2021, when they exploited a zero-day flaw in the Accellion FTA solution.
Since then, Clop has conducted numerous data-theft campaigns using zero-day flaws in SolarWinds Serv-U, GoAnywhere MFT, and, most recently, the massive attacks on MOVEit Transfer servers.
Active exploitation
As part of AssetNote’s technical writeup, the researchers shared enough information for threat actors to develop exploits for the Citrix ShareFile CVE-2023-24489 flaw. Soon after, other researchers released their own exploits on GitHub.
On July 26th, GreyNoise began monitoring for attempts to exploit the vulnerability. After CISA warned about the flaw today, GreyNoise updated its report to say there had been a significant uptick in attempts by different IP addresses.
“GreyNoise observed a significant spike in attacker activity the day CISA added CVE-2023-24489 to their Known Exploited Vulnerabilities Catalog,” warns GreyNoise.
At this time, GreyNoise has seen attempts to exploit or check if a ShareFile server is vulnerable from 72 IP addresses, with the majority from South Korea and others in Finland, the United Kingdom, and the United States.
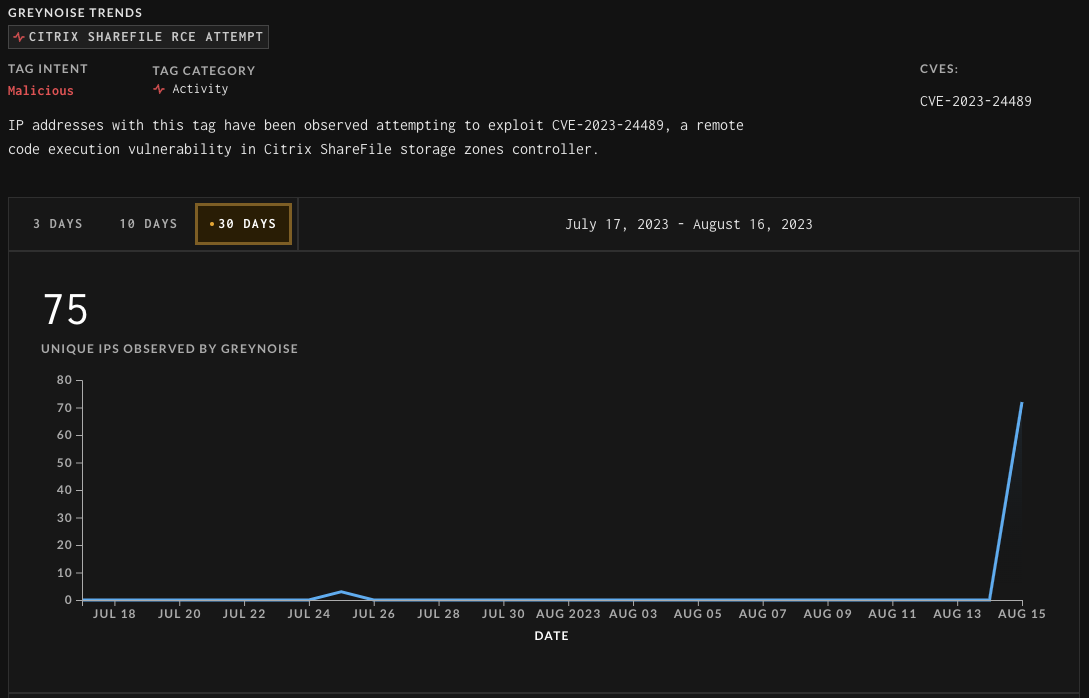
Source: GreyNoise
While no publicly known exploitation or data theft has been linked to this flaw, CISA now requires Federal Civilian Executive Branch (FCEB) agencies to apply patches for this bug by September 6th, 2023.
However, due to the highly targeted nature of these bugs, it would be strongly advised that all organizations apply the updates as soon as possible.







