ClickFix is not a malware, but a very successful social engineering technique. It primarily relies on MFA verification fatigue and fake CAPTCHA pages to silently install malware.
Researchers have discovered and analyzed a ClickFix attack that uses a fake Cloudflare ‘humanness’ check. The Cloudflare check is called Turnstile and has replaced the earlier Cloudflare CAPTCHA process in keeping with an industry-wide migration toward frictionless security.
Cloudflare is a well-known and widely used service designed to improve the security and performance of websites. Most internet users will have come across a Cloudflare Turnstile challenge en route to a website and will not be surprised to see one. Turnstile operates by running non-intrusive JavaScript challenges to verify human activity.
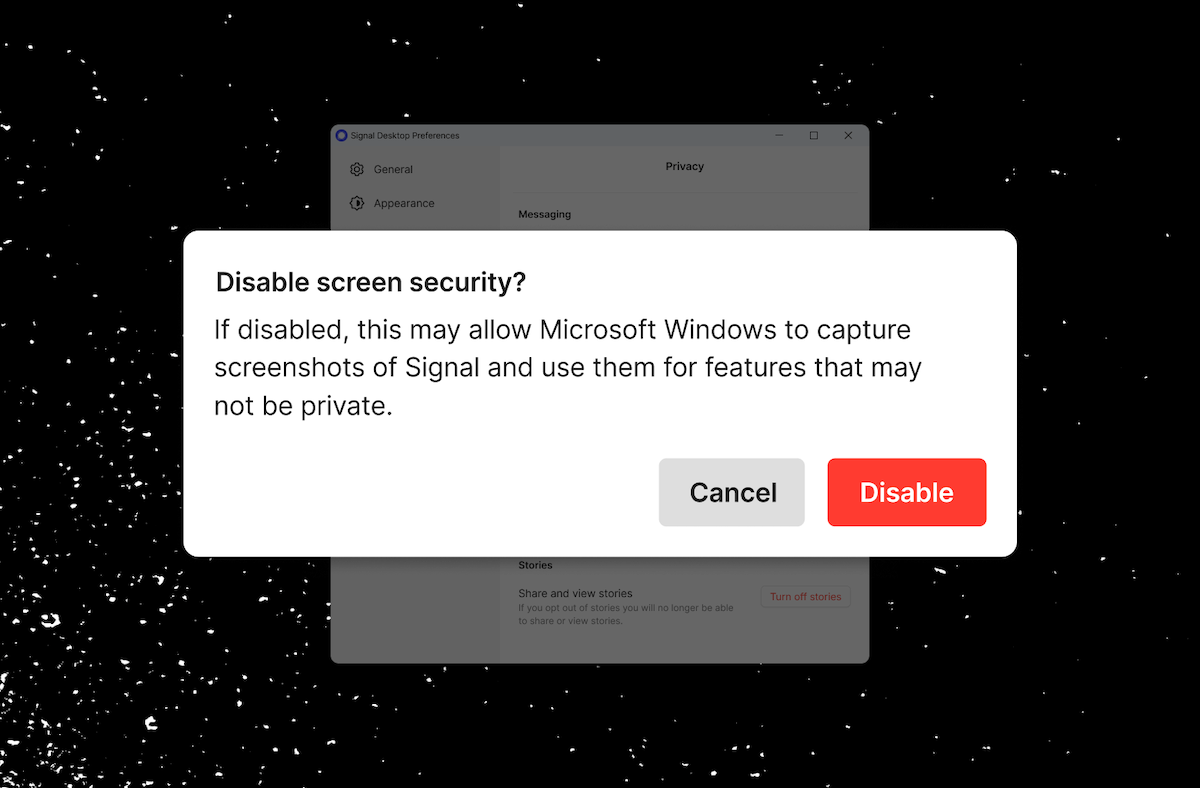
In this example, the fake Turnstile page is an accurate clone of the genuine Cloudflare page, a pixel-perfect copy, including the Cloudflare logo and the Ray ID footer (reminding the user that nothing is amiss since this is a legitimate security check).
But it is not legitimate. By accessing the fake page, a malicious but hidden background process is launched. A PowerShell command is loaded into the user’s clipboard. Then, when the user checks the “Verify you are human” box, a pop-up requests additional user steps. Nothing is overtly malicious, and the additional steps are easily accepted as part of the verification process.
The user is instructed to type Win+R followed by CTRL+V followed by Enter. The first opens the Windows ‘Run’ dialog box, the second copies the clipboard content (preloaded with a PowerShell command), and the third runs the command.
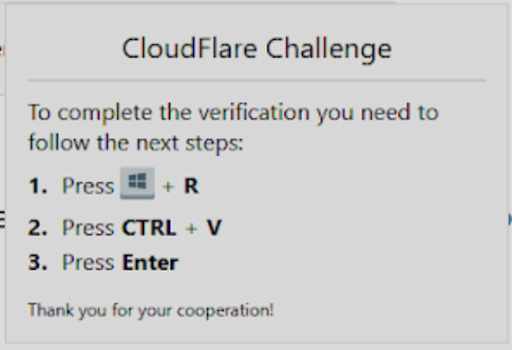
The PowerShell command fetches malware from a remote server and typically executes it in memory. Unless additional controls are in place, antivirus and endpoint protection products would probably not detect anything dubious in a Windows command. “Because of their limited visibility into browser behavior, AV products and other endpoint protection solutions tend to miss these attacks,” explains Lionel Litty, chief security architect at Menlo Security.
The attack comprises “a combination of social engineering and Living off the Land Binaries (LoLBins) which makes it difficult to defend against – the user simply launches PowerShell commands rather than a malicious binary that might be detected by an EDR solution,” adds James Maude, field CTO at BeyondTrust.
In this sample, the only clue that it might possibly be a scam can be seen in the pop-up box and the wording of “CloudFlare Challenge”. Cloudflare does not use an uppercase ‘F’ in its branding, but few users would notice this in their haste to get through the verification process. Verification fatigue is real and applies in many areas of life. If humans get too many warnings without seeing any justification for the warnings, they start to ignore them.
“Campaigns using ClickFix have delivered a variety of payloads in this manner – from info-stealing malware like Lumma and Stealc to full remote access trojans (RATs), which let attackers take control of a victim’s system like NetSupport Manager,” say the researchers.
The fake Turnstile page can be delivered, and targeted, by a variety of methods. Malvertising or social media lures can be designed to attract specific groups – such as healthcare workers – to visit a phishing site; while compromised but legitimate or completely fake websites can simply wait for visitors using a traditional drive-by technique.
“Cloudflare is one of the most impersonated services in phishing attacks. That’s largely because it offers a free tier that attackers exploit to obscure threats,” explains J Stephen Kowski, field CTO at SlashNext Email Security. “These screens are often familiar to users – like Google CAPTCHA or Cloudflare’s human verification – so they lower suspicion while the real malicious content loads in the background or is sideloaded locally.”
Just as Turnstile delivers frictionless security, so ClickFix delivers frictionless crime.
Related: Russia-Linked APT Star Blizzard Uses ClickFix to Deploy New LostKeys Malware, Google Warns
Related: Lazarus Uses ClickFix Tactics in Fake Cryptocurrency Job Attacks
Related: ClickFix Widely Adopted by Cybercriminals, APT Groups
Related: Microsoft Warns of Hospitality Sector Attacks Involving ClickFix