Crypto mining campaign targets Docker environments with new evasion technique

New malware campaign targets Docker environments using unknown methods to secretly mine cryptocurrency, researchers warn.
Researchers from Darktrace and Cado Security have spotted a malware campaign that targets Docker environments with a novel technique to mine cryptocurrency.
The malware campaign targets Docker environments to deploy a malicious node connected to Teneo, a decentralized infrastructure network. Teneo allows users to earn rewards (Teneo Points) by running Community Nodes that scrape public data from social platforms like Facebook, X, Reddit, and TikTok. These points can be converted to $TENEO tokens. The malware covertly monetizes social media bandwidth via this mechanism.
The attack chain begins with a request to launch a container from Docker Hub, specifically the kazutod/tene:ten image.
To analyze the malicious Docker image kazutod/tene:ten, researchers used Docker tools to pull and save it as a tar file for easier inspection.

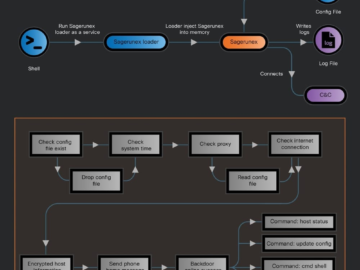
Upon extracting the tar, the experts found the image uses the OCI format, where contents are organized in layers. Each layer is stored as a tar file with accompanying JSON metadata, rather than a traditional file system.
“The Docker image uses the OCI format, which is a little different to a regular file system. Instead of having a static folder of files, the image consists of layers. Indeed, when running the file command over the sha256 directory, each layer is shown as a tar file, along with a JSON metadata file.” reads the report published by DarkTrace. “As the detailed layers are not necessary for analysis, a single command can be used to extract all of them into a single directory, recreating what the container file system would look like:”
The researchers analyzed the ten.py script included in the malicious Docker image and discovered that it is heavily obfuscated using multiple layers of base64 encoding, zlib compression, and string reversal. The script decodes and executes a payload repeatedly, each time generating another encoded string to decode, requiring 63 iterations before the actual malicious code is revealed. The researchers pointed out that despite the complex obfuscation process, the decoding process was easily automated, suggesting the effort was likely meant to deter casual analysis rather than seriously hinder experts.
The malicious script connects to teneo[.]pro, however, instead of scraping, the malware sends fake keep-alive pings to earn “Teneo Points” based on activity levels. This tactic allows evading common detection techniques for XMRig-based cryptojacking attacks. The attacker’s DockerHub profile suggests similar abuse of decentralized compute networks. However, due to the closed nature of private tokens like Teneo, it’s unclear how profitable this method is.
The attacker’s DockerHub profile shows a pattern of abuse, with their latest container running a Nexus network client to earn crypto via distributed zero-knowledge compute tasks.
“Typically, traditional cryptojacking attacks rely on using XMRig to directly mine cryptocurrency, however as XMRig is highly detected, attackers are shifting to alternative methods of generating crypto. Whether this is more profitable remains to be seen. There is not currently an easy way to determine the earnings of the attackers due to the more “closed” nature of the private tokens.” concludes the report “Translating a user ID to a wallet address does not appear to be possible, and there is limited public information about the tokens themselves. “
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, Docker)