D-Link confirms data breach, but downplayed the impact

Taiwanese manufacturer D-Link confirmed a data breach after a threat actor offered for sale on BreachForums stolen data.
The global networking equipment and technology company D-Link confirmed a data breach after a threat actor earlier this month offered for sale on the BreachForums platform the stolen data.
The company became aware of the a claim of data breach on October 2, 2023 and immediately launched an investigation into the alleged incident with the help of the security firm Trend Micro.
D-Link pointed out that the incident did not impact its operations.
The threat actor claimed to have stolen 3 million lines of individual information and the source code for D-Link’s D-View network management software. The threat actor is offering an archive of 1.2 GB. The stolen data includes information for many Taiwanese government officials, as well as the CEOs and employees of the company.
The stolen data includes names, emails, addresses, companies, phone numbers, registration dates, and the last sign-in dates of the users.
“I have breached the internal network of D-Link in Taiwan, I have 3 million lines of customer information, as well as source code to D-View extracted from system,” reads the announcement on BreachForums.
The investigation revealed that the data was stolen from an old D-View 6 system, which reached its end of life as early as 2015.
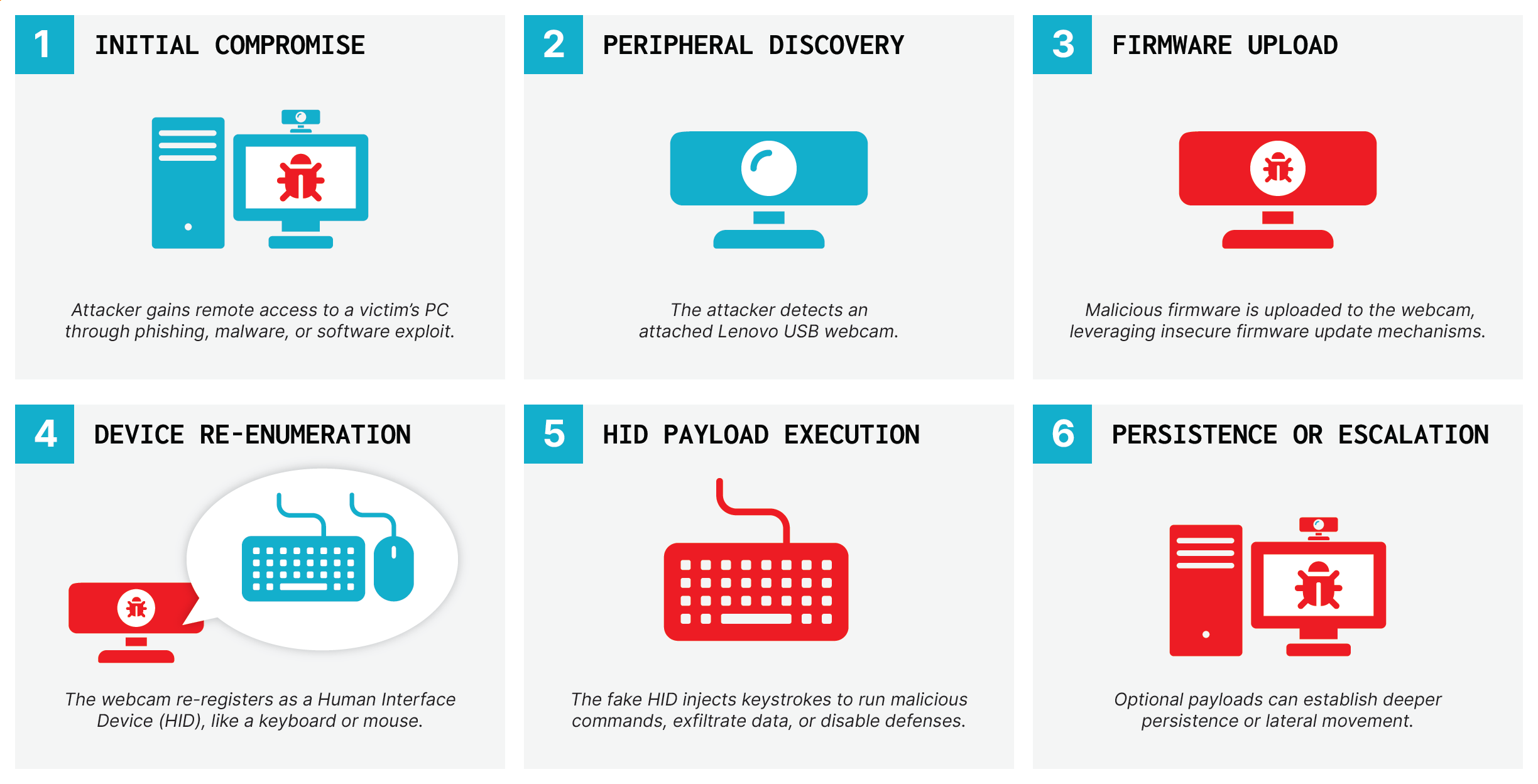
“The data was used for registration purposes back then. So far, no evidence suggests the archaic data contained any user IDs or financial information. However, some low-sensitivity and semi-public information, such as contact names or office email addresses, were indicated.” states the company. “The incident is believed to have been triggered by an employee unintentionally falling victim to a phishing attack, resulting in unauthorized access to long-unused and outdated data.”
D-Link discovered that the security breach was the result of a phishing attack against an employee.
In response to the intrusion, the company immediately shut down presumably relevant servers.
D-Link explained that the attackers only stole approximately 700 records.
“The post claimed to have millions of user data. Based on the investigations, however, it only contained approximately 700 outdated and fragmented records that had been inactive for at least seven years. These records originated from a product registration system that reached its end of life in 2015. Furthermore, the majority of the data consisted of low-sensitivity and semi-public information.” concludes the company. “Judging by the facts, we have good reasons to believe that most of D-Link’s current customers are unlikely to be affected by this incident.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, D-Link)