DarkGate, a Malware-as-a-Service (MaaS) platform, experienced a surge in activity since September 2023, employing various distribution methods, including email attachments, malicious ads, and compromised Samba shares.
Initially a human-operated command-and-control infrastructure, DarkGate has evolved into a versatile tool offering remote access, crypto mining, and other malicious functionalities.
The malware has been actively distributed across North America, Europe, and Asia, leveraging AutoIt or AutoHotkey scripts for initial infection.
Their actors launched a campaign in March 2024, using Excel files disguised as legitimate documents to deliver malicious payloads, primarily targeting North America but expanding to Europe and Asia.
Are you from SOC/DFIR Teams? - Sign up for a free ANY.RUN account! to Analyse Advanced Malware Files
The attack chain involves luring users to open Excel files with embedded links to publicly accessible Samba shares hosting VBS or JS scripts, which download and execute a PowerShell script, which in turn fetches and runs the final AutoHotKey-based DarkGate payload.
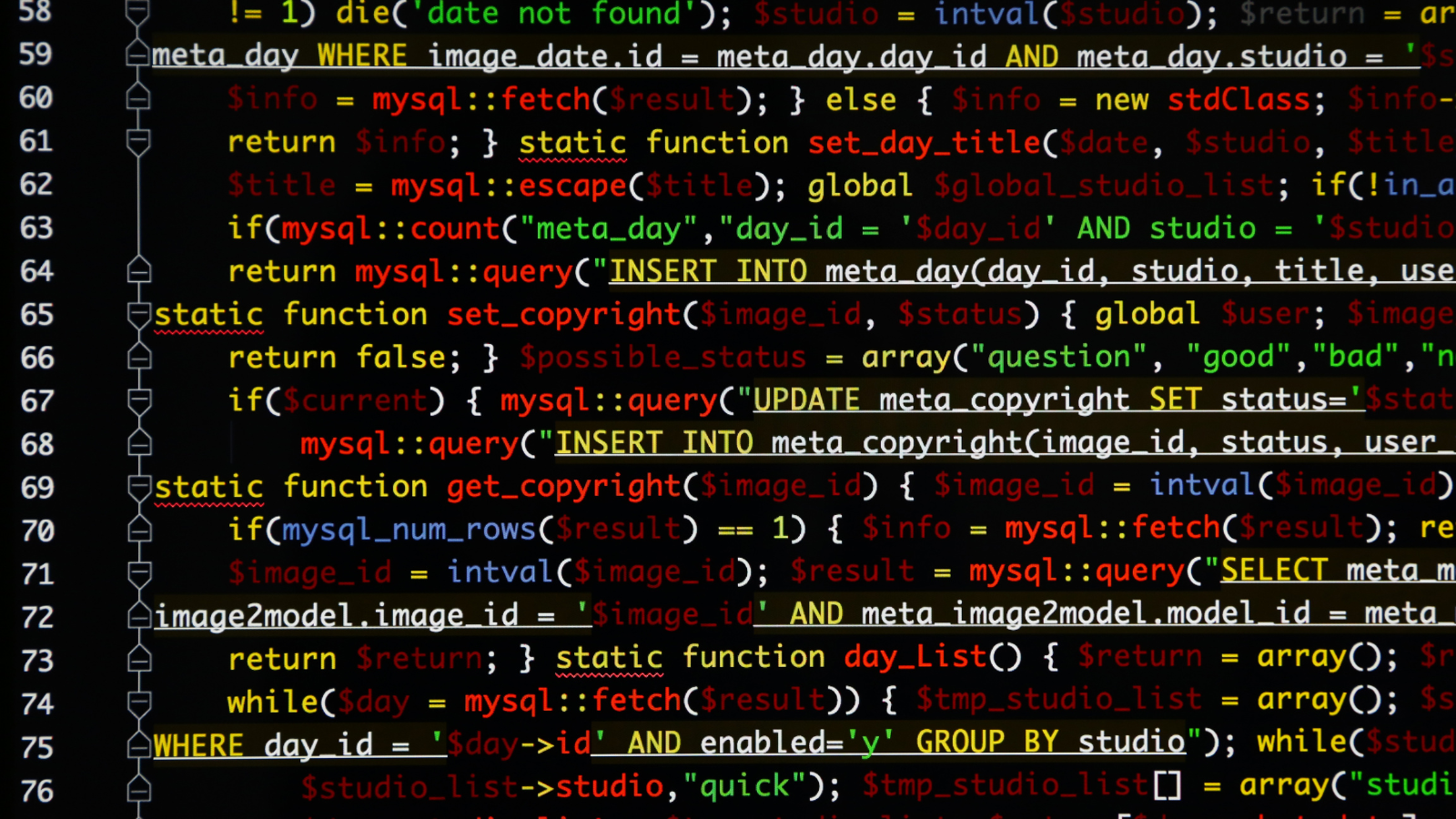
The threat actors employed various evasion techniques, including obfuscation, legitimate software usage, and anti-malware detection checks, to hinder analysis and increase the malware’s persistence.
.webp)
The malware employs anti-analysis techniques to evade detection by checking the system’s CPU to differentiate between virtual environments and physical hosts, potentially halting execution in controlled analysis settings.
It scans for multiple anti-malware programs using specific directory paths and filenames, aiming to avoid triggering their detection mechanisms or even disabling them.
The malware’s ongoing evolution includes adding new anti-malware checks, demonstrating its adaptability to counter evolving security measures.
.webp)
Analysis Of DarkGate Samples Reveals XOR Key Variations
Two sets of DarkGate samples were examined where the first set shared the same campaign ID but had different XOR keys, while the second set shared both the campaign ID and the C2 server but also had distinct XOR keys.
It indicates that DarkGate employs multiple XOR keys for the same campaign or C2 infrastructure, potentially hindering reverse engineering efforts and increasing malware resilience.
DarkGate malware scans a host for specific processes and tools commonly used in malware analysis or virtual environments by employing a complex configuration decryption process involving XOR keys to conceal its behavior.
While some configuration fields remain obscure, analysts have identified correlations between certain values and campaign identifiers.
Multiple samples within the same campaign can utilize distinct XOR keys, suggesting an intentional obfuscation tactic to hinder analysis and understanding of DarkGate’s inner workings.
.webp)
DarkGate C2 traffic, while appearing as unencrypted Base64-encoded HTTP POST requests, conceals obfuscated data, which can be decoded; further obfuscation exists.
Unit 42 looked into an infection that happened on March 14, 2024, and found that five HTTP POST requests with nearly 218 KB of Base64-encoded data sent to nextroundstr.com could have leaked data.
Although DarkGate’s primary function is unclear, its association with follow-on malware like Danabot and reported links to ransomware raise significant security concerns.
“Is Your System Under Attack? Try Cynet XDR: Automated Detection & Response for Endpoints, Networks, & Users!”- Free Demo