In a strategic move to outwit cybercriminals, a dedicated team of cybersecurity researchers devised an operation centered around the creation and strategic storage of fabricated personal data within the domain of the digital cloud.
The bait was set, the trap laid, and the clock began ticking as experts waited for hackers to take the bait, unknowingly stepping into a web of deception.
vpnMentor, which offers VPN and cybersecurity tools and services, created a honeypot for hackers to assess hacker behavior in terms of which data source they were most likely to hack first.
Deceptive Honeypot for Hackers Laid by Cybersecurity Researchers
The cybersecurity researchers created fake personal data, stored it in the cloud, and waited for hackers to access it. The planned data release included 14 Amazon AWS S3 buckets and 1 Google Cloud Storage server, among others.

The hacker honeypot remained openly exposed for an extensive period, spanning 450 days from April 29, 2021, to July 14, 2022.
The Experiment’s Focus: Exploring Common Hacker Behaviors and Actions:
- How soon can hackers detect exposed databases?
- How do different settings of stored data impact a data hack?
- Which data types attracted more cybercriminals?
- Which geographical regions attract the attention of hackers?
Details of the honeypot for hackers to find the answers to the above questions: –
- A website was created in the name of a new fraud prevention company.
- The website had every detail the hackers might want to verify the authenticity of the information. This included the company’s owner details and newly created emails.
- 1 Azure Blob Storage server.
- 12 buckets that had the company’s name with 10 having prefixes and suffixes from other S3 bucket finder software.
- Fake data amounting to 7GB was left open to hackers with source codes, database files, invoices, and CSV files of 21,089 fictitious individuals including their names, email addresses, and telephone numbers.
The data was segregated according to countries with those of the U.S. having the most users adding up to 6,480.
Results of the Honeypot for Hackers

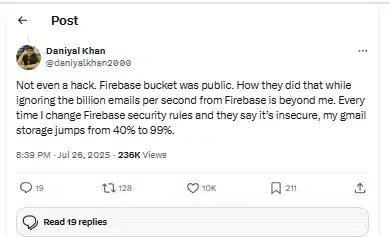
On June 3, 2020, the fake fraud detection services website was published. On June 24, the honeypot was visited for the first time without the CloudFront proxy, indicating that a malicious actor intentionally sought improperly set-up or unsecured S3 buckets, the vpnMentor report read.
A visitor from Croatia accessed the buckets using an automated tool coded in the Go programming language.
It was found that over 99% of the requests made per day amounting to nearly 1,720 were malicious. Researchers found that naming the buckets different from the company name did not provide any additional security.
Instead, one AWS S3 bucket with a generic name was still found by cybercriminals. The monitoring of unauthorized access to the exposed buckets showed that cybercriminals looked for alternate bucket names with the same company name.
Researchers Confirm Three Open-Source S3 Discovery Tools Among Ten Tested:
- PyLazyS3 for files-attachments-[website]
- insp3ctor for [website]-internal-dist
- amass for webdisk.billing-[website]
Insights into Cybercriminal Behavior Based on Honeypot Data Access
- Hackers scan for storage names to identify a match regardless of having a lead.
- Hackers scan websites for links to storage servers and follow the links as a breadcrumb trail to access the servers.
- Hackers look for different bucket names from those they have identified. This could help them reach the control servers.
- The malicious intent of the cybercriminals accessing files from specific locations indicated that the attempts were mostly due to geopolitical factors.
- CSV files were downloaded the most suggesting that user information in them lured them the most.
CSV files in the folders marked under China were accessed the least and US was downloaded the most.
Addressing the threat posed by Chinese-origin hackers, the report wrote, “China-based hackers have repeatedly breached corporate and government resources in the US and other Western countries.”
In the test that lasted over a year, it was concluded that the Google Cloud Storage and Azure Blob Storage servers remained undetected by cyber criminals.
This was attributed to them not being hotlinked and having the company name which prevented them from being detected using brute force.
Data security and storage are a pressing concern for organizations and governments across the globe. Similar experiments making cloud storage accessible to anyone could bring information about hackers and how they find all data storage. Azure Blob Storage was found to be complicated to access suggesting that it poses a challenge to hackers.
The findings could be used by IT teams to maintain data more effectively while keeping unwarranted access at bay.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.