A new backdoor dubbed Dohdoor is actively targeting schools and health care organizations in the United States through a stealthy multi-stage attack chain.
UAT-10027 focuses on education and health care entities in the U.S., sectors that handle highly sensitive personal and medical data but often have limited security budgets and legacy systems.
Cisco Talos assesses with low confidence that UAT-10027 may have a North Korea nexus due to overlaps in tooling and techniques with the Lazarus Group.
The attackers’ end goal is to establish persistent backdoor access with Dohdoor and then deliver follow-on payloads, likely including Cobalt Strike beacons for deeper network compromise and lateral movement.
The campaign, tracked as UAT-10027 by Cisco Talos, has been ongoing since at least December 2025 and abuses DNS-over-HTTPS (DoH) and reputable cloud infrastructure to hide its command-and-control traffic.
However, the victim profile does not fully match Lazarus’ usual cryptocurrency and defense focus. These overlaps include custom decryption logic, DLL sideloading, process hollowing, DoH-based C2, and EDR bypass routines seen in earlier Lazarus-linked tooling such as Lazarloader.
Dohdoor Malware
Initial access is believed to rely on social engineering, with phishing emails delivering or triggering a PowerShell script that acts as a downloader.
Telemetry and OSINT show the actor using PowerShell to invoke curl.exe with an encoded URL to fetch a malicious batch script with “.bat” or “.cmd” extensions from a remote staging server.
The second stage is a Windows batch script that prepares a hidden working directory under C:ProgramData or C:UsersPublic, then downloads a malicious DLL from the C2 via a specific URL path, renaming it to mimic legitimate Windows DLLs such as propsys.dll or batmeter.dll.
The script then copies trusted Windows binaries like Fondue.exe, mblctr.exe, or ScreenClippingHost.exe into that folder and sideloads the malicious DLL through these executables, before cleaning up evidence by wiping the Run history, clearing the clipboard, and deleting itself.

Once Dohdoor is loaded, it establishes backdoored access and pulls the next-stage payload directly into memory, likely a Cobalt Strike Beacon payload that runs reflectively inside legitimate Windows processes to evade traditional detection.
The malware later uses process hollowing against hardcoded Windows binaries such as OpenWith.exe, wksprt.exe, ImagingDevices.exe, and wab.exe to execute the decrypted payload under the guise of trusted processes.
Dohdoor’s standout feature is its use of DNS-over-HTTPS to resolve C2 infrastructure while blending into normal web traffic.
Instead of sending plaintext DNS queries, the malware crafts encrypted HTTPS requests to Cloudflare’s DoH service on port 443, using headers like User-Agent: insomnia/11.3.0 and Accept: application/dns-json, and parses the JSON response by locating “Answer” and “data” fields to extract IP addresses.
After resolving the C2 IP, Dohdoor sets up HTTPS tunnels using GET requests that mimic curl traffic (for example, User-Agent: curl/7.88 or curl/7.83.1) and specific URL paths to fetch encrypted payloads.
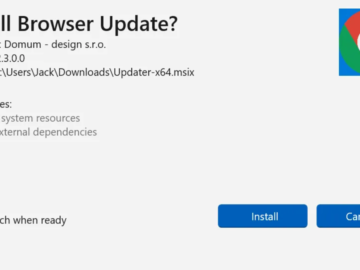
UAT-10027 further masks its infrastructure behind Cloudflare edge network and uses deceptive subdomains such as “MswInSofTUpDloAd” and “DEEPinSPeCTioNsyStEM” on mixed-case TLDs like “.OnLiNe”, “.DeSigN”, and “.SoFTWARe” to resemble update or security systems and frustrate simple string-based blocking.

This decryption style, including the use of a constant 0x26, closely mirrors techniques documented in Lazarloader, reinforcing the suspected link to North Korean operators.
EDR bypass and defensive coverage
Dohdoor dynamically resolves Windows API functions by hash instead of static imports and implements syscall unhooking against ntdll.dll to evade user-mode hooks on sensitive functions such as NtProtectVirtualMemory.
The payload delivered by Dohdoor is protected with a custom XOR-SUB decryption scheme that uses a 4:1 encrypted-to-decrypted size ratio and position-dependent logic, implemented via SIMD instructions for bulk processing and a secondary loop for remaining bytes.

It reads the first bytes of targeted functions, compares them with expected syscall stub patterns, and if hooks are detected, patches in a direct syscall stub to bypass monitoring code.
Although Talos did not capture a full final payload, TLS fingerprints from one C2 host including a JA3S hash 466556e923186364e82cbdb4cad8df2c and a specific certificate serial are consistent with default Cobalt Strike server profiles, suggesting Dohdoor is used as a loader for Cobalt Strike.
Cisco’s security stack now includes ClamAV signatures such as Win.Loader.Dohdoor-10059347-0 and Ps1.Loader.Dohdoor-10059533-0, along with Snort rules for Snort 2 and Snort 3, to detect both the loader components and related network activity in enterprise environments.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.