Over the weekend, security researchers released a proof-of-concept (PoC) exploit for a maximum severity vulnerability in Progress Software’s WS_FTP Server file sharing solution.
Assetnote researchers who discovered and reported the maximum severity flaw (CVE-2023-40044) published a blog post with a PoC exploit and additional technical details on Saturday.
CVE-2023-40044 is caused by a .NET deserialization vulnerability in the Ad Hoc Transfer Module, allowing unauthenticated attackers to remotely execute commands on the underlying operating system via a simple HTTP request.
“This vulnerability turned out to be relatively straight forward and represented a typical .NET deserialization issue that led to RCE. It’s surprising that this bug has stayed alive for so long, with the vendor stating that most versions of WS_FTP are vulnerable,” Assetnote said.
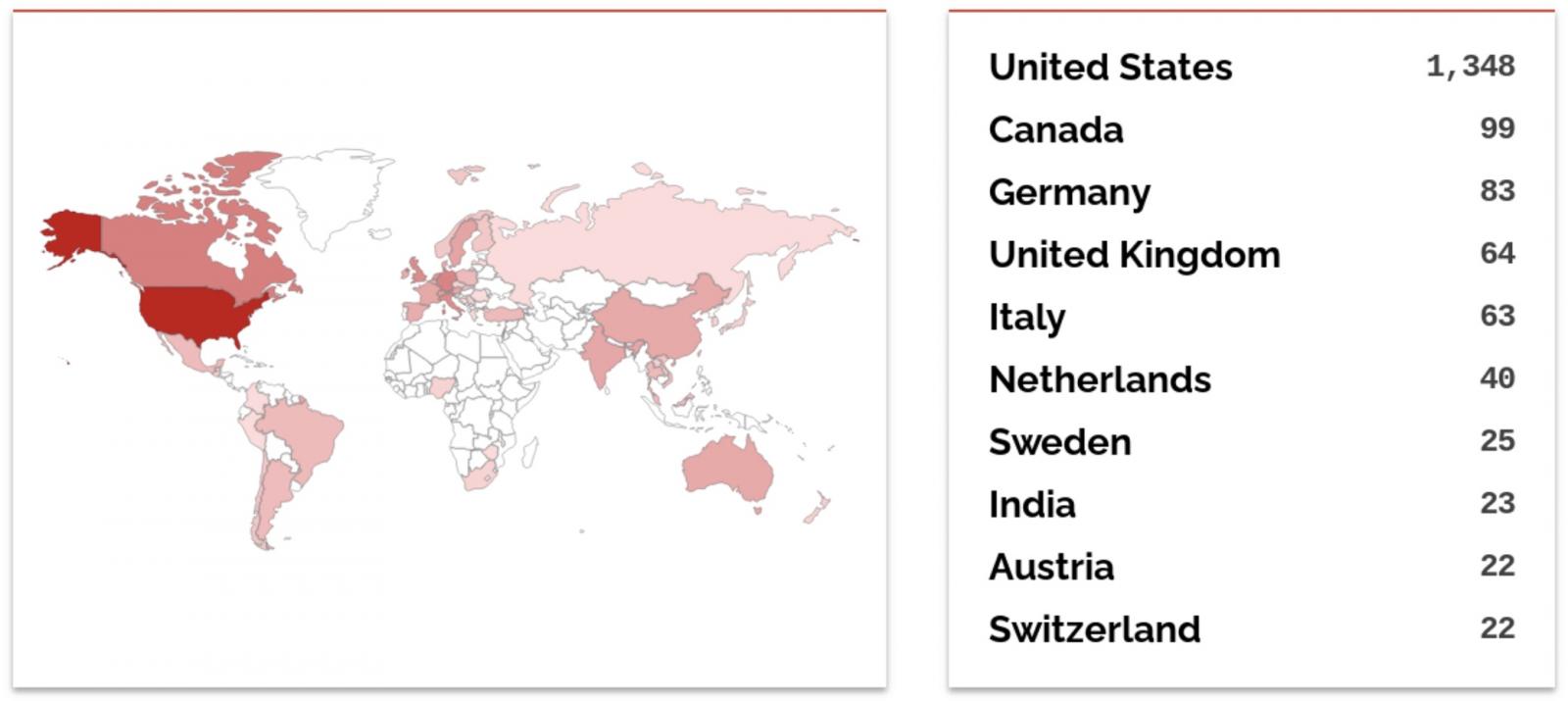
“From our analysis of WS_FTP, we found that there are about 2.9k hosts on the internet that are running WS_FTP (and also have their webserver exposed, which is necessary for exploitation). Most of these online assets belong to large enterprises, governments and educational institutions.”
A Shodan search confirms Assetnote’s estimates, showing that more than 2,000 devices running WS_FTP Server are currently reachable over the Internet.
Exploited in the wild
The day the PoC exploit was released, cybersecurity company Rapid7 also revealed that attackers began exploiting CVE-2023-40044 on Saturday evening, September 30.
“As of September 30, Rapid7 has observed multiple instances of WS_FTP exploitation in the wild,” said Caitlin Condon, Head of Vulnerability Research at Rapid7.
“The process execution chain looks the same across all observed instances, indicating possible mass exploitation of vulnerable WS_FTP servers.
“Additionaly, our MDR team has observed the same Burpsuite domain used across all incidents, which may point to a single threat actor behind the activity we’ve seen.”
Progress Software released security updates to address the critical CVE-2023-40044 vulnerability on Wednesday, September 27.
“We have addressed the vulnerabilities above and the Progress WS_FTP team strongly recommends performing an upgrade,” Progress warned at the time.
“We do recommend upgrading to the most highest version which is 8.8.2. Upgrading to a patched release, using the full installer, is the only way to remediate this issue.
Organizations that cannot immediately patch their servers can still thwart incoming attacks by disabling the vulnerable WS_FTP Server Ad Hoc Transfer Module.
On Friday, the Health Sector Cybersecurity Coordination Center (HC3), the U.S. Health Department’s security team, also warned all Healthcare and Public Health sector organizations to patch their servers as soon as possible.