SeroXen RAT, a Remote Access Trojan (RAT) that debuted in late 2022, is now gaining traction. Security researchers and threat analysts have spotted attempts to market it as a legitimate tool for covert access to computers.
SeroXen RAT is affordable, with a monthly license priced at $30 and a lifetime bundle available for $60, making it accessible to a wide range of users. With its fileless nature, the RAT excels at evading both static and dynamic analysis.
AT&T Alien Labs researchers Alejandro Prada and Ofer Caspi explained the modus operandi of the SeroXen RAT.
“SeroXen combines multiple open-source tools into one powerful malware. This includes Quasar RAT for remote access capabilities, and a rootkit named r77-rootkit to hide its presence in the system, this includes processes, files, network connections, and more”, the security researchers told The Cyber Express.
The malware is delivered as an obfuscated batch file which hardens its detection. SeroXen is fileless, its process is injected into other processes making it more difficult to detect, they added.
SeroXen RAT combines various open-source projects to enhance its capabilities, including Quasar RAT, r77-rootkit, and the command line utility NirCmd.
Marketing and distribution of SeroXen RAT

Quasar RAT, an open-source remote administration tool, has a long-standing history of malicious activities perpetrated by threat actors, APT groups, and government-sponsored attacks.
Its first release, under the name “xRAT,” occurred in July 2014, and it was later renamed “Quasar” in August 2015. The tool has seen updates up to version 1.4.1 in March 2023, demonstrating its enduring popularity among threat actors and its integration with other payloads.

Image Credit: AT&T Alien Labs
A recent analysis of SeroXen RAT by AT&T Alien Labs revealed that it is a modified branch of the open-source Quasar RAT.
This new variant introduces additional features, and it is being marketed and sold by an individual who claims to be a reseller of the tool.
The initial appearance of SeroXen RAT was on a Twitter account associated with an English-speaking teenager, who also posted a review of the RAT on YouTube, emphasizing its value for attackers and encouraging others to purchase it.
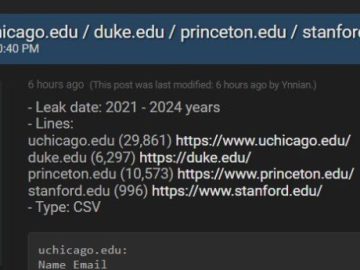
In December 2022, a dedicated domain, SeroXen[.]com, was registered to market and sell the RAT. Around this time, SeroXen RAT started to be observed in the wild, with zero detections on VirusTotal.
The malware quickly gained popularity and was advertised on social media platforms, including TikTok, Twitter, and YouTube, and cracking forums like hack forums. Users in gaming forums reported infections after downloading video games, which were later identified as SeroXen RAT.
Fileless nature of SeroXen RAT: Targeting the gaming community
To evade detection, the threat actor behind SeroXen RAT continually updates the domain name associated with the RAT. After decommissioning SeroXen.com, they switched to SeroXen [.]net in March 2023.
The new domain was registered using GoDaddy and Cloudflare for hosting, but it is solely used for marketing and sales, not for Command and Control (C&C) communications.
Examining the samples uploaded to VirusTotal, it becomes apparent that SeroXen RAT primarily targets video game users.
Lure injector cheat files with names referencing popular games like Fortnite, Valorant, Roblox, and
Warzone 2 have been observed. The threat actor also used Discord to distribute some samples, exploiting the gaming community’s active presence on the platform.
SeroXen RAT’s most prominent selling point is its complete undetectability during static analysis. The RAT is packed into an obfuscated PowerShell batch file, typically 12-14 megabytes.
This large size may deter certain antivirus programs from analyzing it, potentially allowing SeroXen RAT to bypass detection. While the current sample analyzed has zero detections on VirusTotal, some crowdsourced Sigma Rules flag its activity as suspicious.
SeroXen RAT: Evading dynamic analysis and Sandbox detection
In addition to its fileless nature, SeroXen RAT poses challenges for dynamic analysis. Sandbox environments may fail to detect the RAT due to its sophisticated techniques that evade virtualization and sandbox detection mechanisms and its use of string encryption for subsequent payloads.
To better understand the working mechanics of the RAT, TCE reached out to AT&T Alien Labs to learn about its evading techniques.
SeroXen evades its detection by packing the final malicious payload through multiple compression and encryption layers when at the end it is delivered as a polymorphic batch file, AT&T Alien Labs researchers said.
In addition, the malware uses a rootkit to inject itself into other processes. As the malware is fileless, for persistence it creates scheduled tasks that will invoke an obfuscated PowerShell script stored in the registry, they added.
The RAT also employs anti-debugging techniques utilizing Windows Management Instrumentation (WMI) to identify virtualization environments like VMware, thereby delaying and complicating analysis. It also checks for the presence of debuggers and employs pings to make threads sleep, further evading detection.
During execution, SeroXen RAT exhibits low detection rates for its child processes and dropped files. When the malicious payload is delivered to the victim, often through phishing emails or Discord channels, the victim receives a ZIP file containing an innocuous file.
In contrast, the heavily obfuscated batch file remains hidden and is automatically executed upon launch.


The rootkit enables fileless persistence, child process hooking, and in-memory process injection, among other features. It also has the ability to embed additional malware, such as NirCmd or Quasar, which are decrypted and injected into other processes.
The rootkit aims to ensure the stealthy execution of SeroXen RAT within the system. It employs process injections, executes commands received from other processes, and employs various techniques to avoid detection, such as AMSI bypass and DLL unhooking.
The communication between the RAT and the command and control (C&C) server utilizes TLS encryption with a certificate bearing the same Common Name as the Quasar RAT.
The C&C server’s functionalities closely resemble those found in the Quasar GitHub repository, including support for TCP network streams, network serialization, compression using QuickLZ, and secure communication through TLS encryption.
SeroXen RAT and future threat landscape
To sum up, the developer behind SeroXen RAT has cleverly combined free resources to create a RAT that evades detection in static and dynamic analysis.
By leveraging the capabilities of Quasar RAT, complemented by NirCmd and r77-rootkit, the tool has become highly elusive and difficult to detect.
Although its current focus is primarily on gaming communities, it is only a matter of time before SeroXen RAT is employed in targeted attacks against companies.
As the threat landscape continues to evolve with tools and services like SeroXen RAT, security researchers at AT&T Alien Labs have shared their quick response plan to that organizations can adopt to protect themselves against SeroXen RAT attacks:
- Install and keep security products such as antivirus with its latest detection signatures
- Keep software up to date: Regularly update operating systems, applications, and firmware to patch security vulnerabilities
- Do not open suspicious files or emails.
- Security awareness: Educate staff members regarding evolving threats and best practices for staying safe