The first known cryptojacking operation mining the Dero coin has been found targeting vulnerable Kubernetes container orchestrator infrastructure with exposed APIs.
Dero is a privacy coin promoted as an alternative to Monero with even more robust anonymity protection.
Compared to Monero or other cryptocurrencies, Dero promises faster and higher monetary mining rewards, which is probably why it has caught the attention of threat actors.
In a new report by CrowdStrike, researchers explain how the ongoing campaign was discovered in February 2023 after finding unusual behavior when monitoring customers’ Kubernetes clusters.
Scanning Kubernetes
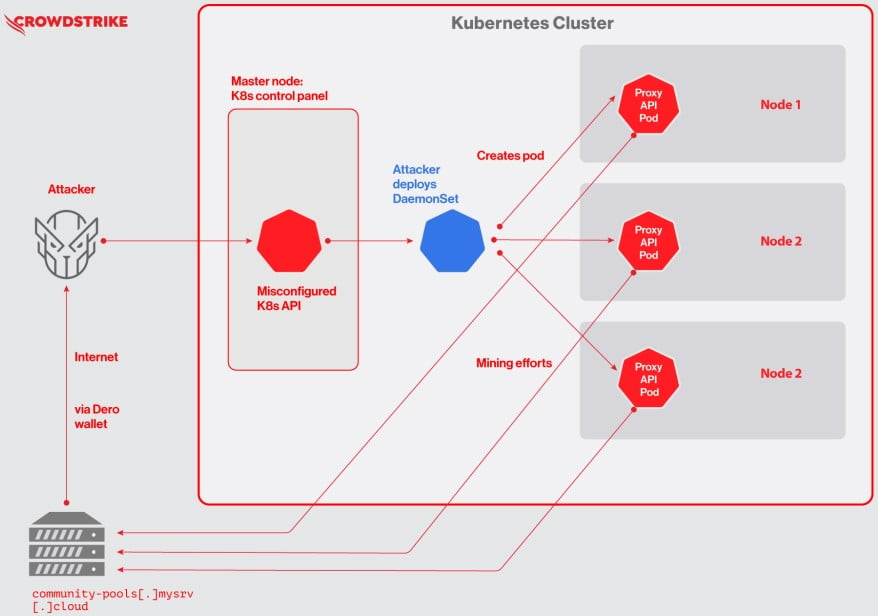
The researchers say the attacks start with the threat actors scanning exposed, vulnerable Kubernetes clusters with authentication set to –anonymous-auth=true, allowing anyone anonymous access to the Kubernetes API.
After gaining access to the API, the threat actors will deploy a DaemonSet named “proxy-api” that allows the attackers to engage the resources of all nodes in the cluster simultaneously and mine Dero using the available resources.
The installed miners will be joined to a Dero mining pool, where everyone contributes hashing power and receives shares of any rewards.
Crowdstrike says the Docker image used in the observed Dero cryptojacking campaign was hosted on Docker Hub and is a slightly modified CentOS 7 image containing additional files named “entrypoint.sh” and “pause.”
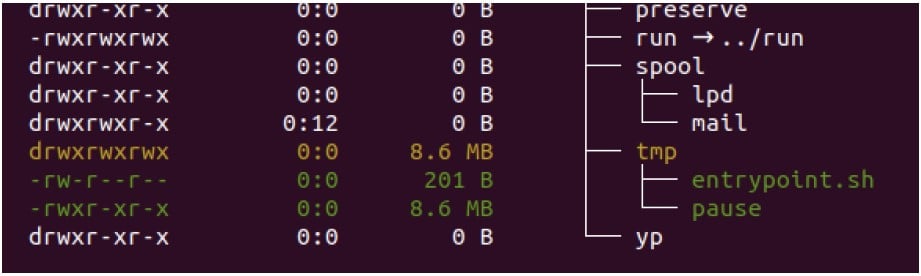
The first file initializes the Dero miner with a hardcoded wallet address and mining pool, while the “pause” binary is the actual coin miner.
Crowdstrike’s analysts have noticed no intention from the threat actors to move laterally, disrupt the cluster operation, steal data, or cause further damage, so the campaign appears to be 100% financially motivated.
A turf war
Shortly after Crowdstrike discovered the Dero campaign, its analysts detected a Monero cryptojacking operator attempting to hijack the same resources, eventually kicking out the Dero miner.
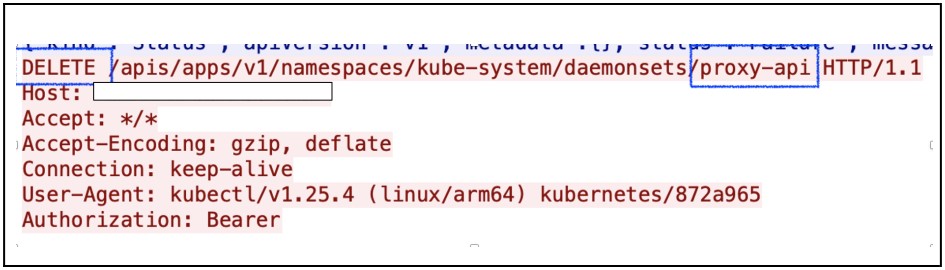
The second threat actor deleted the “proxy-api” DaemonSet used by the Dero campaign and then performed a much more aggressive takeover of the cluster, employing a privileged pod and mounting a “host” directory, attempting to escape the container.
Next, the threat actor used a custom XMRig miner downloaded from the attacker’s command and control server to mine Monero by escalating to the host and installing a custom service.
The Monero campaign opted to mine on the host instead of the pods, as Dero did, to access more computational resources and make a more significant profit.
Also, running mining processes on the host makes them harder to detect if properly masked as system services.
Finally, the operator installed a cronjob to trigger the payload, thus ensuring persistence between Kubernetes cluster restarts.
While cryptojacking campaigns are almost a dime-a-dozen, mining Dero over other privacy coins, such as Monero, makes this a novel campaign.







