A design flaw in the logging mechanism of Fortinet’s VPN servers has been uncovered, allowing attackers to conduct brute-force attacks without detection.
This vulnerability, disclosed by cybersecurity researchers at Pentera, highlights a critical gap in Fortinet’s ability to log successful authentication attempts during brute-force attacks, leaving enterprises vulnerable to potential breaches.
The issue lies in how Fortinet VPN servers handle authentication and authorization processes. When a user attempts to log in, the server responds with one of three outcomes: valid credentials, failed authentication, or an error due to excessive failed attempts.

However, successful authentication attempts are only logged after the authorization phase, which establishes the VPN session.
If an attacker stops at the authentication phase—where credentials are verified but no session is created—the successful attempt goes unlogged.
Download the Forrester TEI Study now and sign up for guidance to maximize cybersecurity ROI.
Blind Spot in Logging
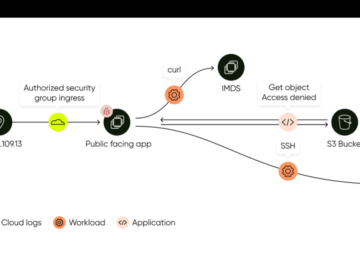
This creates a significant blind spot for incident response (IR) teams. Failed login attempts are recorded, but successful brute-force attempts remain invisible.
Consequently, attackers can validate leaked credentials without alerting security teams or triggering alarms, Pentera said.
The inability to log successful authentication attempts poses severe risks:
- Credential Validation Without Detection: Attackers can test leaked credentials against Fortinet VPN servers to identify valid accounts without leaving a trace.
- Delayed Response: IR teams monitoring logs may assume all brute-force attempts failed, missing opportunities to reset compromised passwords or investigate further.
- Credential Exploitation: Validated credentials could be used later for unauthorized access or sold on dark web marketplaces.
Expert Recommendations
While Fortinet does not classify this issue as a vulnerability, researchers argue that it undermines security and recommend immediate action:
- Enhanced Logging: Fortinet should update its logging mechanisms to record all authentication attempts—successful or failed—at the earliest stage. This would provide better visibility into suspicious activities.
- Multi-Factor Authentication (MFA): Organizations using Fortinet VPNs should enforce MFA to add an additional layer of security against brute-force attacks.
- Regular Audits and Updates: Enterprises should frequently audit their VPN configurations and apply updates to address any known vulnerabilities.
- Web Application Firewalls (WAFs): Deploying WAFs in front of VPN servers can help detect and block brute-force attempts.
Until Fortinet addresses this issue, organizations can take proactive measures:
- Monitor logs for anomalies such as “SSL tunnel shutdown” entries without prior “SSL tunnel established” logs, which could indicate credential validation without session creation.
- Limit login attempts and configure block durations to deter brute-force attacks.
- Use custom SSL ports and strong encryption protocols to reduce exposure.
This flaw underscores the importance of robust logging and monitoring practices in securing enterprise networks. While the vulnerability does not currently have a fix from Fortinet, organizations must act swiftly to implement compensating controls and reduce their attack surface.
Are you from SOC/DFIR Teams? – Analyse Malware & Phishing with ANY.RUN -> Try for Free