A recently discovered worm that researchers call LittleDrifter has been spreading over USB drives infecting systems in multiple countries as part of a campaign from the Gamaredon state-sponsored espionage group.
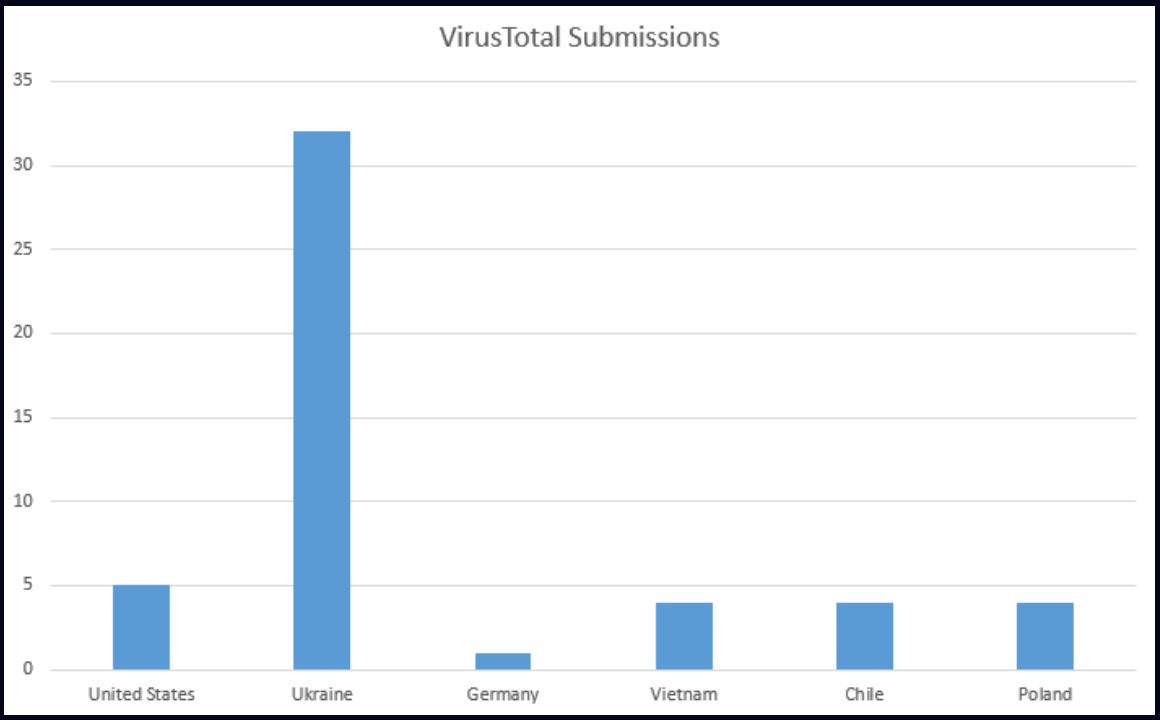
Malware researchers saw indications of compromise in the United States, Ukraine, Germany, Vietnam, Poland, Chile, and Hong Kong, which suggests that the threat group lost control of LittleDrifter, which reached unintended targets.
According to research from Check Point, the malware is written in VBS and was designed to propagate through USB drives, as an evolution of Gamaredon’s USB PowerShell worm.
Gamaredon, also known as Shuckworm, Iron Tilden, and Primitive Bear is a cyber espionage threat group associated with Russian that for at least a decade has targeted organizations in Ukraine from multiple sectors, including government, defense, and critical infrastructure.
LitterDrifter details
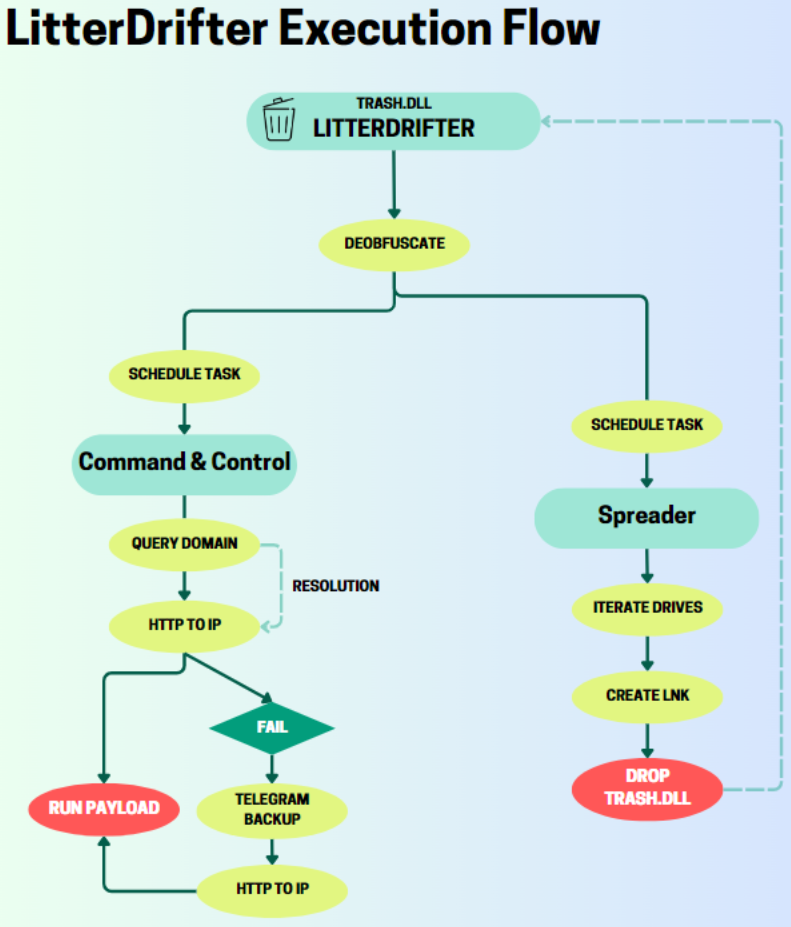
LitterDrifter’s purpose is to establish communications with the threat group’s command and control (C2) server and to spread over USB drives.
To achieve its goal, the malware uses two separate modules, which are executed by the heavily obfuscated VBS component trash.dll.
LitterDrifter and all its components nest in the user’s “Favorites” directory and establish persistence by adding scheduled tasks and registry keys.
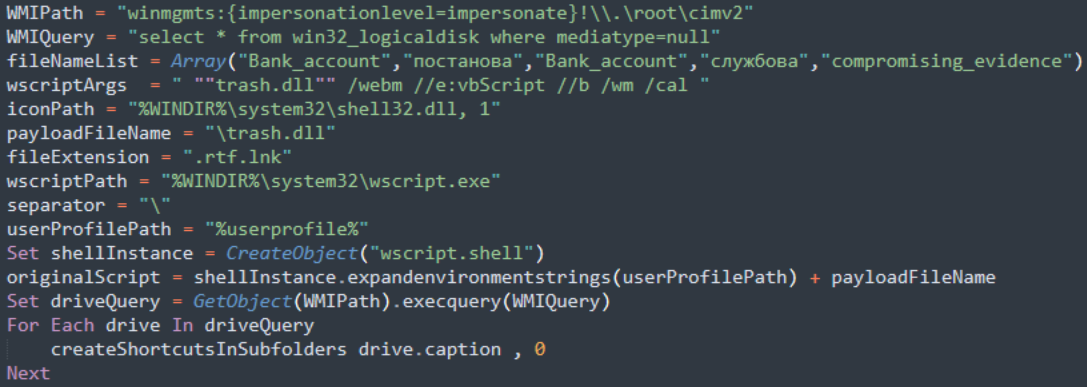
The module responsible for propagation to other systems monitors for newly inserted USB drives and creates deceptive LNK shortcuts along with a hidden copy of the “trash.dll.”
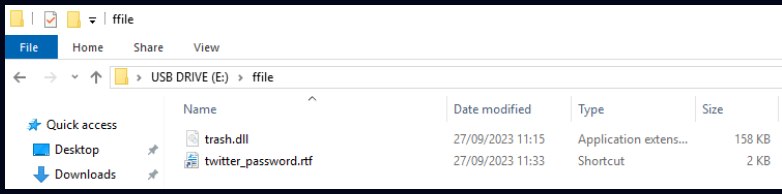
The malware uses the Windows Management Instrumentation (WMI) management framework to identify target drives and creates shortcuts with random names to execute malicious scripts.
The researchers explain that Gamaredon uses domains as placeholder for the IP addresses where the C2 servers are. From this perspective, the threat group has a “rather unique” approach.
Before trying to contact the C2 server, the malware looks in the temporary folder for a configuration file. If such a file does not exist, LittleDrifter pings one of Gamaredon’s domains using a WMI query.
The reply to the query contains the domain’s IP address, which is saved to a new configuration file.
Check Point notes that all domains used by the malware are registered under ‘REGRU-RU’ and use the ‘.ru’ top-level domain, which is consistent with past reports on Gamaredon activity.
The typical lifespan of each IP address that acts as a C2 in LitterDrifter operations is about 28 hours, but the addresses may change multiple times per day to evade detection and blocking.
The C2 may send additional payloads that LitterDrifter attempts to decode and execute on the compromised system. CheckPoint clarifies that no additional payloads were downloaded in most cases, which may indicate that the attacks are highly targeted.
As a backup option, the malware can also retrieve the C2 IP address from a Telegram channel.
LitterDrifter is likely part of the first stage of an attack, trying to establish persistence on the compromised system and waiting for the C2 to deliver new payloads that would further the attack.
The malware is characterized by simplicity and does not rely on novel techniques but it appears to be effective.
Check Point’s report provides hashes for almost two dozen LittleDrifter samples as well as domains associated with Gamaredon’s infrastructure.






