23andMe has confirmed to BleepingComputer that it is aware of user data from its platform circulating on hacker forums and attributes the leak to a credential-stuffing attack.
23andMe is a U.S. biotechnology and genomics firm offering genetic testing services to customers who send a saliva sample to its labs and get back an ancestry and genetic predispositions report.
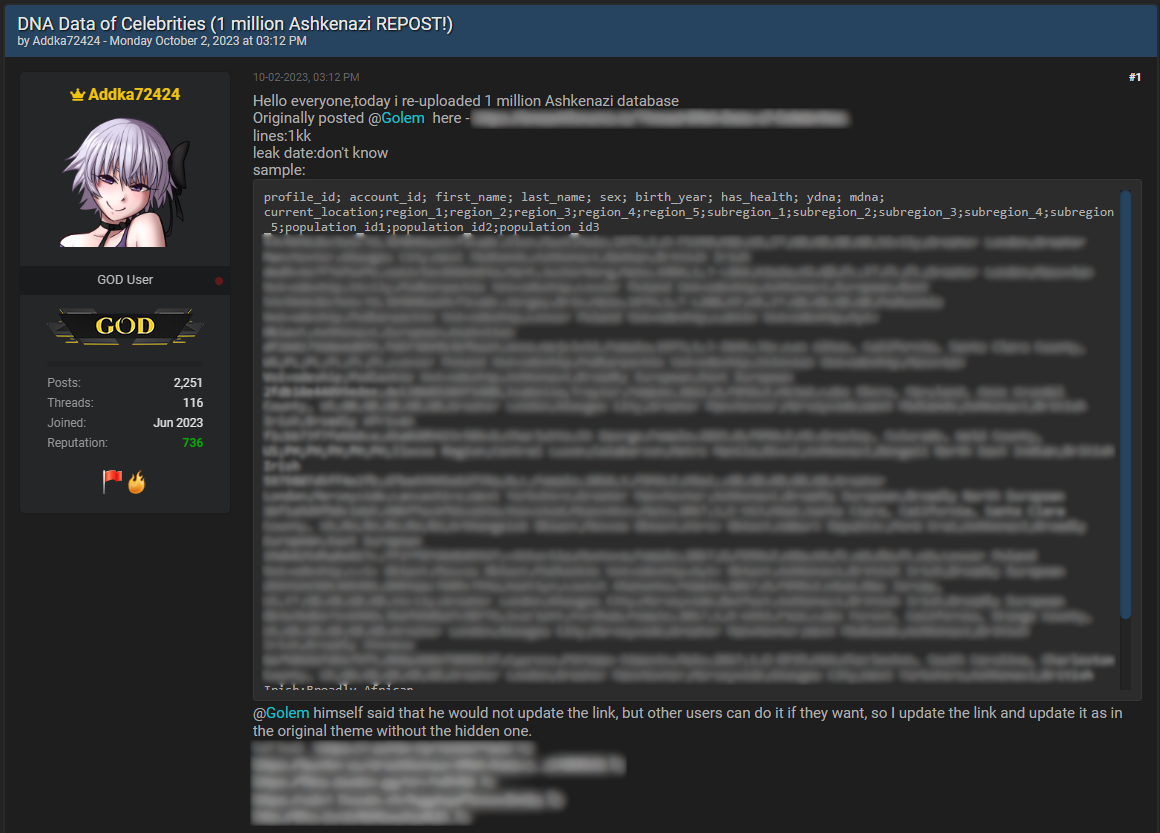
Recently, a threat actor leaked samples of data that was allegedly stolen from a genetics firm and, a few days later, offered to sell data packs belonging to 23andMe customers.
Source: BleepingComputer
The initial data leak was limited, with the threat actor releasing 1 million lines of data for Ashkenazi people. However, on October 4, the threat actor offered to sell data profiles in bulk for $1-$10 per 23andMe account, depending on how many were purchased.
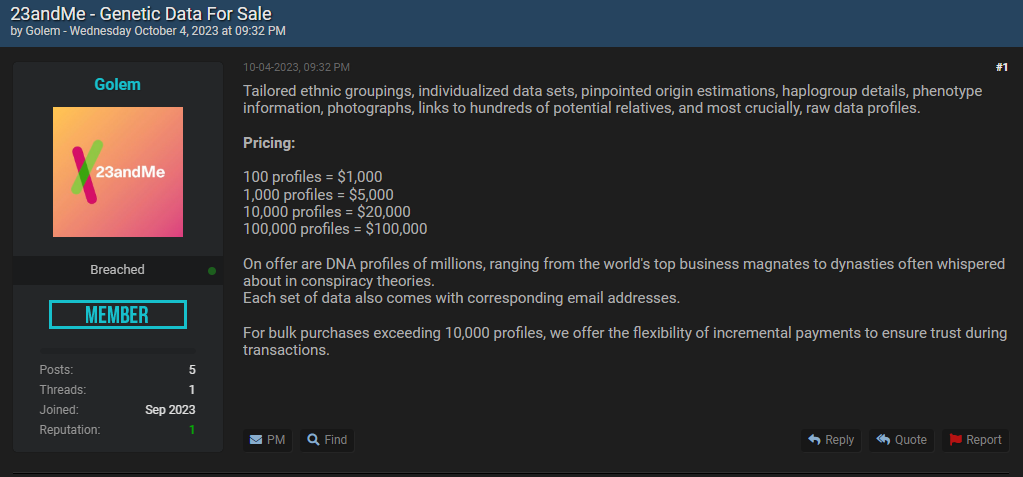
Source: BleepingComputer
A 23andMe spokesperson confirmed the data is legitimate and told BleepingComputer that the threat actors used exposed credentials from other breaches to access 23andMe accounts and steal the sensitive data.
“We were made aware that certain 23andMe customer profile information was compiled through access to individual 23andMe.com accounts,” stated 23andMe’s spokesperson
“We do not have any indication at this time that there has been a data security incident within our systems.”
“Rather, the preliminary results of this investigation suggest that the login credentials used in these access attempts may have been gathered by a threat actor from data leaked during incidents involving other online platforms where users have recycled login credentials.”
The information that has been exposed from this incident includes full names, usernames, profile photos, sex, date of birth, genetic ancestry results, and geographical location.
BleepingComputer has also learned that the number of accounts sold by the cybercriminal does not reflect the number of 23andMe accounts breached using exposed credentials.
The compromised accounts had opted into the platform’s ‘DNA Relatives’ feature, which allows users to find genetic relatives and connect with them.
The threat actor accessed a small number of 23andMe accounts and then scraped the data of their DNA Relative matches, which shows how opting into a feature can have unexpected privacy consequences.
23andMe told BleepingComputer that the platform offers two-factor authentication as an additional account protection measure and encourages all users to enable it.
Users should refrain from reusing passwords and consistently employ strong, distinct credentials for every online account they have.






