GitCaught campaign relies on Github and Filezilla to deliver multiple malware

Researchers discovered a sophisticated cybercriminal campaign by Russian-speaking threat actors that used GitHub to distribute malware.
Recorded Future’s Insikt Group discovered a sophisticated cybercriminal campaign by Russian-speaking threat actors from the Commonwealth of Independent States (CIS). The attackers, tracked as GitCaught, used a GitHub profile to impersonate legitimate software applications, including 1Password, Bartender 5, and Pixelmator Pro, to distribute malware such as Atomic macOS Stealer (AMOS), Lumma, Octo, and Vidar. The campaign shows how attackers exploit trusted internet services to carry out cyberattacks that steal personal information.
The malware employed in the multi-faceted campaign shared the same C2 infrastructure, suggesting attackers coordinated efforts to maximize the impact of the attacks. The threat actors are suspected to be a highly organized group with substantial resources and sophisticated capabilities.
The threat actors behind this campaign use a free and web-based infrastructure, like FileZilla servers, to deliver malware. This tactic allows them to avoid detection. The researchers noticed the presence of Russian-language artifacts within the analyzed HTML code, a circumstance that provides evidence about the threat actors’s origin.
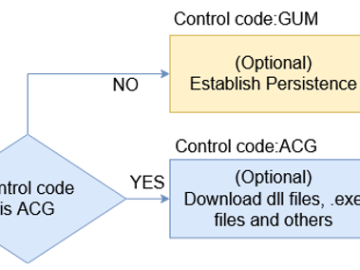
During the investigation, the researchers identified twelve websites that falsely advertised downloads of legitimate macOS applications, but instead directed victims to a GitHub profile to distribute the Atomic macOS Stealer (AMOS). Insikt Group monitored the profile for several weeks and discovered additional malicious payloads, including the Octo banking trojan and various Windows-based infostealers. Further analysis showed communications with a FileZilla server used as a dropper for infostealer variants like Lumma and Vidar, delivered through Python scripts and encrypted files with variable payloads. Insights from the FileZilla server and Recorded Future’s Network Intelligence led to the identification of four additional IP addresses linked to the threat actor’s network.
“Over the course of Insikt Group’s analysis of AMOS, twelve domains were discovered impersonating legitimate macOS applications such as CleanShot X, 1Password, and Bartender. All twelve identified domains redirected users to a GitHub profile belonging to a user named “papinyurii33” to download macOS installation media, resulting in an AMOS infostealer infection. As Insikt Group reported previously, the current AMOS version is capable of infecting both Intel-based and ARM-based Macs. According to GitHub, this profile was created on January 16, 2024.” reads the report published by the Recorded Future’s Insikt Group. “The last observed contribution by papinyurii33, as of this writing, occurred on March 7, 2024, and contained only two repositories, or “repos,” named “2132” and “22.””

The Insikt Group also spotted a website distributing AMOS malware along with Rhadamanthys by posing as legitimate software. Instead of hosting the malware directly, the fake application site redirects users to file-sharing services like Dropbox and Bitbucket. One of these malicious sites masqueraded as Rainway, a now-defunct remote desktop video game streaming service. While Rainway’s legitimate domain is rainway[.]com, the malicious domain is rainway[.]cloud. The researchers noticed that Google search for “Rainway” currently lists rainway[.]cloud as a top result above the legitimate rainway[.]com.
The report includes IndicatorsofCompromise and mitigations for this campaign.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, GitCaught)