GitHub has enabled push protection by default for all public repositories to prevent accidental exposure of secrets such as access tokens and API keys when pushing new code.
Today’s announcement comes after the company introduced push protection in beta almost two years ago, in April 2022, as an easy way to prevent sensitive information leaks automatically. The feature became generally available for all public repos in May 2023.
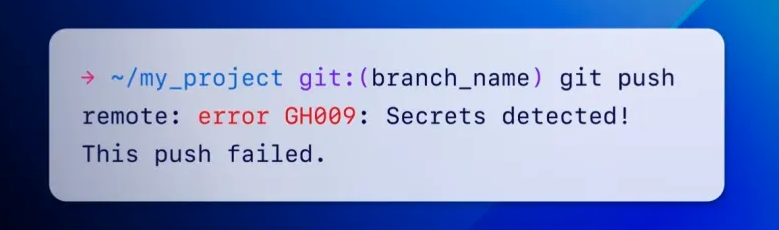
Push protection proactively prevents leaks by scanning for secrets before ‘git push’ operations are accepted and blocking the commits when a secret is detected.
GitHub says that the secret scanning feature automatically prevents secrets from leaking by spotting over 200 token types and patterns from over 180 service providers (API keys, private keys, secret keys, authentication tokens, access tokens, management certificates, credentials, and more).
“This week, we began the rollout of push protection for all users. This means that when a supported secret is detected in any push to a public repository, you will have the option to remove the secret from your commits or, if you deem the secret safe, bypass the block,” GitHub’s Eric Tooley and Courtney Claessens said.
“It might take a week or two for this change to apply to your account; you can verify status and opt-in early in code security and analysis settings.”
Even with push protection toggled on by default for all public repos, GitHub users can circumvent the automated commit block. While not recommended, they can completely deactivate push protection in their security settings.
Organizations subscribed to the GitHub Enterprise plan can use GitHub Advanced Security, which safeguards sensitive information within private repositories. This also adds a suite of other secret scanning features, as well as code scanning, AI-driven code suggestions, and other static application security (SAST) capabilities.
“Accidental leaks of API keys, tokens, and other secrets risk security breaches, reputation damage, and legal liability at a mind-boggling scale,” Tooley and Claessens said.
“In just the first eight weeks of 2024, GitHub has detected over 1 million leaked secrets on public repositories. That’s more than a dozen accidental leaks every minute.”
More details on using push protection from the command line or allowing some secrets to be pushed are available on this GitHub documentation page.
As BleepingComputer has reported in recent years, exposed credentials and secrets have led to multiple high-impact breaches [1, 2, 3].







