GoFetch side-channel attack against Apple systems allows secret keys extraction

Researchers demonstrated a new side-channel attack, named GoFetch, against Apple CPUs that could allow an attacker to obtain secret keys.
A team of researchers from several US universities demonstrated a new microarchitectural side-channel attack named GoFetch that could allow attackers to extract secret keys from systems using Apple CPUs.
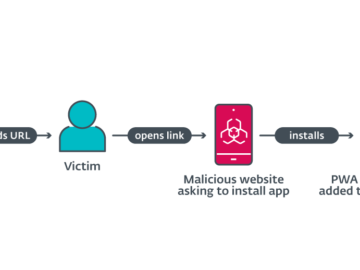
GoFetch side-channel attack can extract secret keys from constant-time cryptographic implementations via data memory-dependent prefetchers (DMPs).
Data memory-dependent prefetchers (DMPs) are a type of hardware optimization technique used in modern processors to improve performance.
Researchers explained that DMPs are present in many Apple CPUs, the researchers demonstrated how to extract keys from OpenSSL Diffie-Hellman, Go RSA, as well as CRYSTALS Kyber and Dilithium.
The researchers performed a reverse-engineering of DMPs on Apple m-series CPUs and discovered that the DMP activates and attempts to dereference data loaded from memory that resembles a pointer.
“This explicitly violates a requirement of the constant-time programming paradigm, which forbids mixing data and memory access patterns.” reads the report published by the researchers. “To exploit the DMP, we craft chosen inputs to cryptographic operations, in a way where pointer-like values only appear if we have correctly guessed some bits of the secret key. We verify these guesses by monitoring whether the DMP performs a dereference through cache-timing analysis. Once we make a correct guess, we proceed to guess the next batch of key bits. Using this approach, we show end-to-end key extraction attacks on popular constant-time implementations of classical (OpenSSL Diffie-Hellman Key Exchange, Go RSA decryption) and post-quantum cryptography (CRYSTALS-Kyber and CRYSTALS-Dilithium).”
The researchers demonstrated the GoFetch attacks on Apple systems using m1 processors, however, they believe that systems based on m2 and m3 CPUs are also vulnerable.
The first attack method targeting Apple m-series DMP was discovered by Augury in 2022. GoFetch is based on Augury, but is significantly more aggressive.
“Specifically, we find that any value loaded from memory is a candidate for being dereferenced (literally!). This allows us to sidestep many of Augury’s limitations and demonstrate end-to-end attacks on real constant-time code.” continues the experts.
The researchers explained that DMP can be disabled only on some processors. On m3 CPUs, it is possible to disable DMP setting the DIT bit on.
The researchers plan to release a proof-of-concept (PoC) exploit soon, they also confirmed to have disclosed their findings to Apple on December 5, 2023
“For users, we recommend using the latest versions of software, as well as performing updates regularly. Developers of cryptographic libraries can either set the DOIT bit and DIT bit bits, which disable the DMP on some CPUs.” said the researchers. “Additionally, input blinding can help some cryptographic schemes avoid having attacker-controlled intermediate values, avoiding key-dependent DMP activation. Finally, preventing attackers from measuring DMP activation in the first place, for example by avoiding hardware sharing, can further enhance the security of cryptographic protocols.”
The experts published a paper that includes details about their study, they also published a video PoC for the attack.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, Apple)