An ongoing Google ads malvertising campaign is spreading malware installers that leverage KoiVM virtualization technology to evade detection when installing the Formbook data stealer.
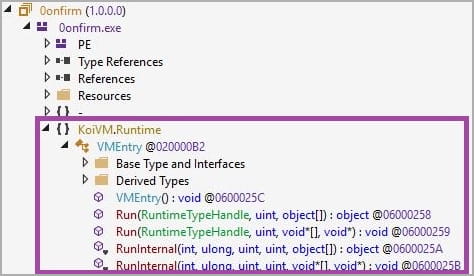
KoiVM is a plugin for the ConfuserEx .NET protector that obfuscates a program’s opcodes so that the virtual machine only understands them. Then, when launched, the virtual machine translates the opcodes back to their original form so that the application can be executed.
“Virtualization frameworks such as KoiVM obfuscate executables by replacing the original code, such as NET Common Intermediate Language (CIL) instructions, with virtualized code that only the virtualization framework understands,” explains a new report by SentinelLabs.
“A virtual machine engine executes the virtualized code by translating it into the original code at runtime.”
“When put to malicious use, virtualization makes malware analysis challenging and also represents an attempt to evade static analysis mechanisms.”
In a Google advertising campaign spotted by Sentinel Labs, threat actors push the Formbook information-stealing malware as virtualized .NET loaders dubbed ‘MalVirt,’ that help distribute the final payload without triggering antivirus alerts.
Sentinel Labs comments that while KoiVM virtualization is popular for hacking tools and cracks, it is seldom used in malware distribution.
Instead, the security firm believes the new trend in its use might be one of the multiple side effects of Microsoft’s disabling of macros in Office.
Abusing Google search ads
Over the past month, researchers have seen increased abuse of Google search ads to distribute various malware, including RedLine Stealer, Gozi/Ursnif, Vidar, Rhadamanthys stealer, IcedID, Raccoon Stealer, and many more.
In the ongoing campaign seen by SentinelLabs, threat actors push the MalVirt loaders in ads pretending to be for the Blender 3D software.
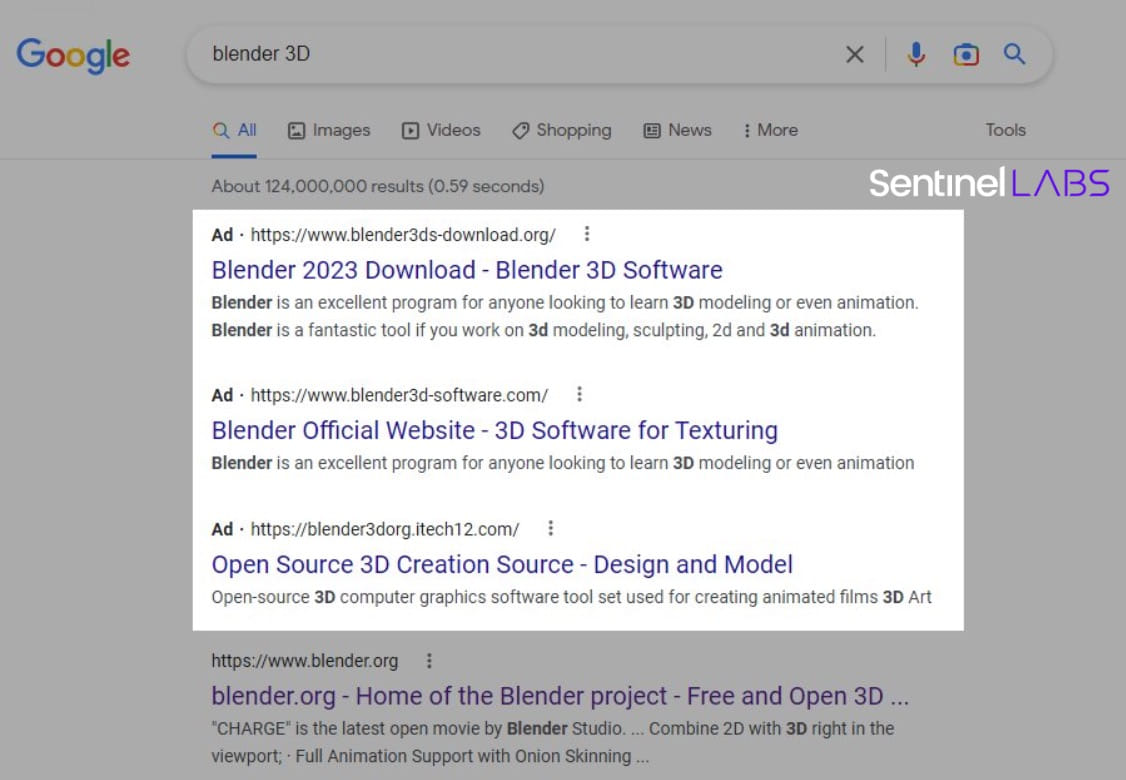
The downloads offered by these fake sites utilize invalid digital signatures impersonating Microsoft, Acer, DigiCert, Sectigo, and AVG Technologies USA.
While these invalid signatures will not trick Windows into showing them as signed, the MalVirt loaders still pack features to avoid detection.
“For example, some samples patch the AmsiScanBuffer function implemented in amsi.dll to bypass the Anti Malware Scan Interface (AMSI) that detects malicious PowerShell commands,” explains researcher A. Milenkoski.
“Further, in an attempt to evade static detection mechanisms, some strings (such as amsi.dll and AmsiScanBuffer) are Base-64 encoded and AES-encrypted.”
The loaders can also detect if they run in a virtualized environment by querying specific registry keys, and if they do, the execution stops to evade analysis.
MalVirt also uses a signed Microsoft Process Explorer driver loaded at system start-up as “TaskKill,” enabling it to modify running processes to dodge detection.
To also evade the decompilation of the virtualized code, the loaders also use a modified version of KoiVM that features additional obfuscation layers, making its decyphering even more challenging.
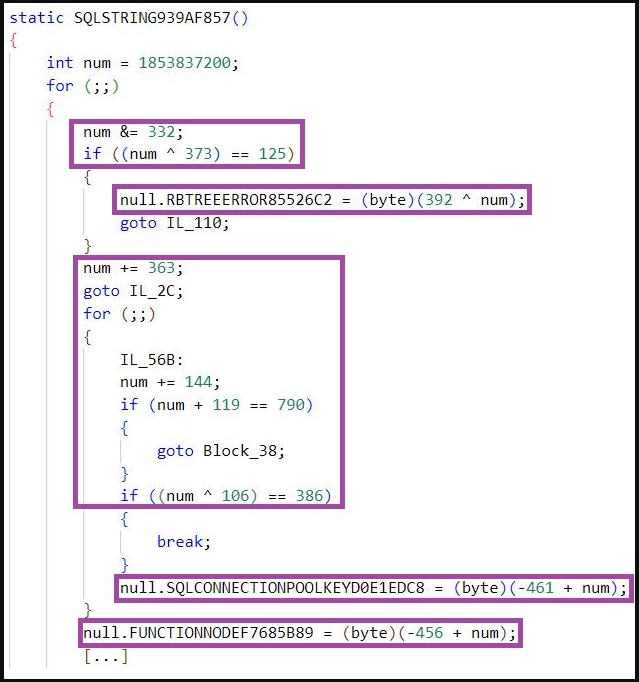
SentinelLabs says this custom KoiVM implementation confuses standard devirtualization frameworks like the ‘OldRod’ by obfuscating its routine through arithmetic operations instead of using straightforward assignments.
Milenkoski says it’s possible to defeat the obfuscation in these MalVirt loaders and restore the original order of KoiVM’s 119 constant variables.
However, the additional obfuscation makes it difficult, requiring hefty manual labor since existing automated tools cannot help.
Hiding the infrastructure
In addition to all detection avoidance systems used in the malware loader, a new trick is employed by Formbook itself that helps disguise its real C2 (command and control) traffic and IP addresses.
The info-stealing malware mixes its real traffic with various “smokescreen” HTTP requests whose content is encrypted and encoded so they don’t stand out.
The malware communicates with those IPs randomly, picking them out of a hardcoded list with domains hosted by various companies.
SentinelLabs says that in the samples it analyzed, it saw Formbook communicating with 17 domains, only one of which was the actual C2 server, and the rest serving as mere decoys to confuse network traffic monitoring tools.
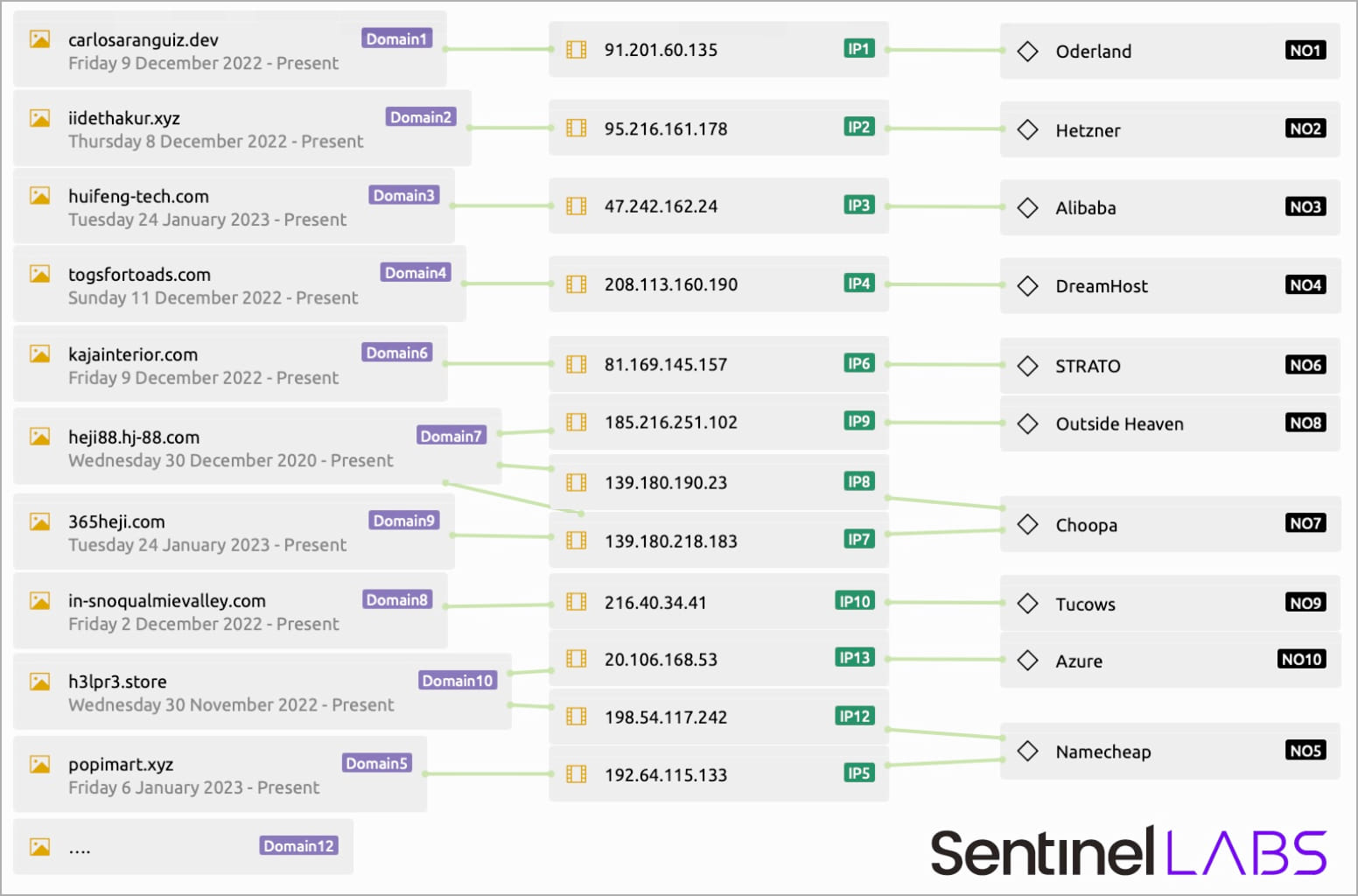
This is a novel system on a pretty old malware strain, indicating that its operators are interested in empowering it with new features that will make it better at staying hidden from security tools and analysts.
Whether or not threat actors have completely switched malspam distribution of Formbook to Google search advertisements remains to be seen, but it’s another example that users need to be very careful of the links they click in search results.






