Cybercriminals are increasingly weaponizing legitimate software installer frameworks like Inno Setup to distribute malware, turning user-friendly tools into covert vehicles for malicious payloads.
Originally designed to simplify software deployment on Windows, Inno Setup has become a favored tool among threat actors due to its trusted appearance and powerful Pascal scripting capabilities.
This sophisticated abuse allows attackers to disguise malware within seemingly benign installation packages, often bypassing user suspicion and even evading some antivirus solutions.
Exploiting Trust in Software Distribution Tools
As highlighted by the Splunk Threat Research Team (STRT), a recent campaign demonstrates how these malicious installers deliver information-stealing malware like RedLine Stealer through a multi-stage infection chain involving shellcode execution and the use of HijackLoader for stealthy payload delivery.
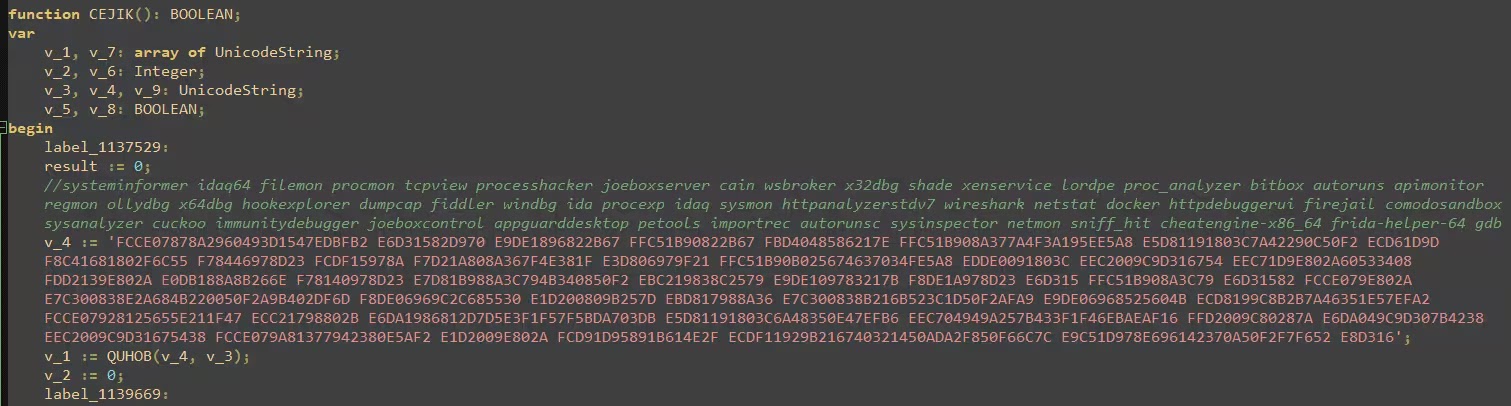
The attack begins with a malicious Inno Setup installer that leverages Pascal scripting to execute a series of evasion techniques, including debugger and sandbox detection.
The script employs XOR encryption to obfuscate critical strings and uses Windows Management Instrumentation (WMI) queries to check for malware analysis tools and virtual machine environments, terminating the process if such conditions are detected.
If the environment passes these checks, the installer uses a TinyURL link to download a compressed payload from a command-and-control (C2) server, often hidden behind access-restricted pages on platforms like rentry[.]org.

A Multi-Stage Malware Delivery Chain
Once downloaded, the payload a ZIP archive is extracted using a renamed 7-Zip utility, and a scheduled task ensures persistence by launching a hidden executable upon system reboot.
This payload then initiates a complex sequence involving DLL sideloading, where a trojanized QtGuid4.dll decrypts shellcode from an encrypted file, ultimately loading HijackLoader.
Known for its modular design and evasion tactics like Heaven’s Gate and Process Hollowing, HijackLoader decrypts and injects the final payload, RedLine Stealer, into a legitimate MSBuild.exe process to steal sensitive data such as browser credentials and cryptocurrency wallet information.
RedLine Stealer further employs “constant unfolding” obfuscation, dynamically constructing parameters at runtime to complicate static analysis, while using browser flags like –no-sandbox in Chrome to disable security features and launching Internet Explorer with extensions disabled to facilitate malicious actions undetected.
This campaign exemplifies the sophisticated abuse of trusted tools, as attackers exploit Inno Setup’s legitimacy to distribute malware through phishing, cracked software, or poisoned updates.
The STRT has developed multiple detections to identify such threats, focusing on indicators like unsigned DLL sideloading, hidden scheduled tasks, and suspicious browser behaviors.
As cybercriminals continue to refine these tactics, leveraging legitimate frameworks for malicious ends, both users and organizations must remain vigilant, employing robust endpoint security and monitoring to detect and mitigate these stealthy threats before they compromise critical data.
Indicators of Compromise (IOC)
| Description | Hash |
|---|---|
| Malicious Inno Setup Loader Hash 1 | 0d5311014c66423261d1069fda108dab33673bd68d697e22adb096db05d851b7 |
| Malicious Inno Setup Loader Hash 2 | 0ee63776197a80de42e164314cea55453aa24d8eabca0b481f778eba7215c160 |
| Malicious Inno Setup Loader Hash 3 | 12876f134bde914fe87b7abb8e6b0727b2ffe9e9334797b7dcbaa1c1ac612ed6 |
| Malicious Inno Setup Loader Hash 4 | 8f55ad8c8dec23576097595d2789c9d53c92a6575e5e53bfbc51699d52d0d30a |
Exclusive Webinar Alert: Harnessing Intel® Processor Innovations for Advanced API Security – Register for Free