Cybersecurity agencies worldwide have issued a joint advisory warning against the growing threat posed by “fast flux,” a sophisticated technique used by malicious actors to evade detection and obscure the locations of their command-and-control (C2) servers.
The advisory, released by organizations such as the National Security Agency (NSA), Cybersecurity and Infrastructure Security Agency (CISA), and their counterparts in Australia, Canada, and New Zealand, highlights fast flux as a critical gap in network defenses that demands immediate attention.
Fast flux is characterized by the rapid rotation of Domain Name System (DNS) records, including IP addresses, associated with a single domain.
This dynamic resolution technique enables cybercriminals to maintain resilient infrastructure for malicious operations, such as ransomware attacks, phishing campaigns, and botnet management.
By leveraging fast flux, attackers can effectively circumvent IP blocking mechanisms, complicating efforts to trace their activities or disrupt their networks.
Single and Double Flux Variants
The fast flux technique manifests in two primary variants:
- Single Flux: In this approach, a single domain name is linked to multiple IP addresses that are frequently rotated in DNS responses. This ensures uninterrupted access to the domain even if individual IP addresses are blocked or taken down.

- Double Flux: Building on single flux, this variant also involves frequent changes to DNS name servers responsible for resolving the domain. This additional layer of redundancy further anonymizes malicious domains, making them harder to track.


Both techniques rely heavily on botnets comprising compromised devices across the internet.
According to the Report, these botnets act as proxies or relay points, making it challenging for defenders to identify malicious traffic or execute takedowns of the infrastructure.
Key Advantages for Malicious Actors
Fast flux offers several strategic advantages to cybercriminals:
- Resilience: The rapid rotation of botnet devices ensures continuity of operations despite law enforcement or abuse notifications.
- Anonymity: Investigators face significant challenges in tracing malicious content back to its origin due to constantly changing IP addresses.
- Ineffectiveness of IP Blocking: The dynamic nature of fast flux renders traditional IP blocking techniques obsolete.
This technique has been observed in ransomware campaigns like Hive and Nefilim, as well as operations by advanced persistent threat groups such as Gamaredon.
Beyond maintaining C2 communications, fast flux plays a pivotal role in phishing campaigns and cybercriminal marketplaces.
Phishing websites leveraging fast flux remain operational despite takedown efforts, enabling attackers to steal sensitive information or distribute malware efficiently.
Some bulletproof hosting (BPH) providers even advertise fast flux services on dark web forums as a means to evade Spamhaus blocklists and enhance the reliability of malicious activities.
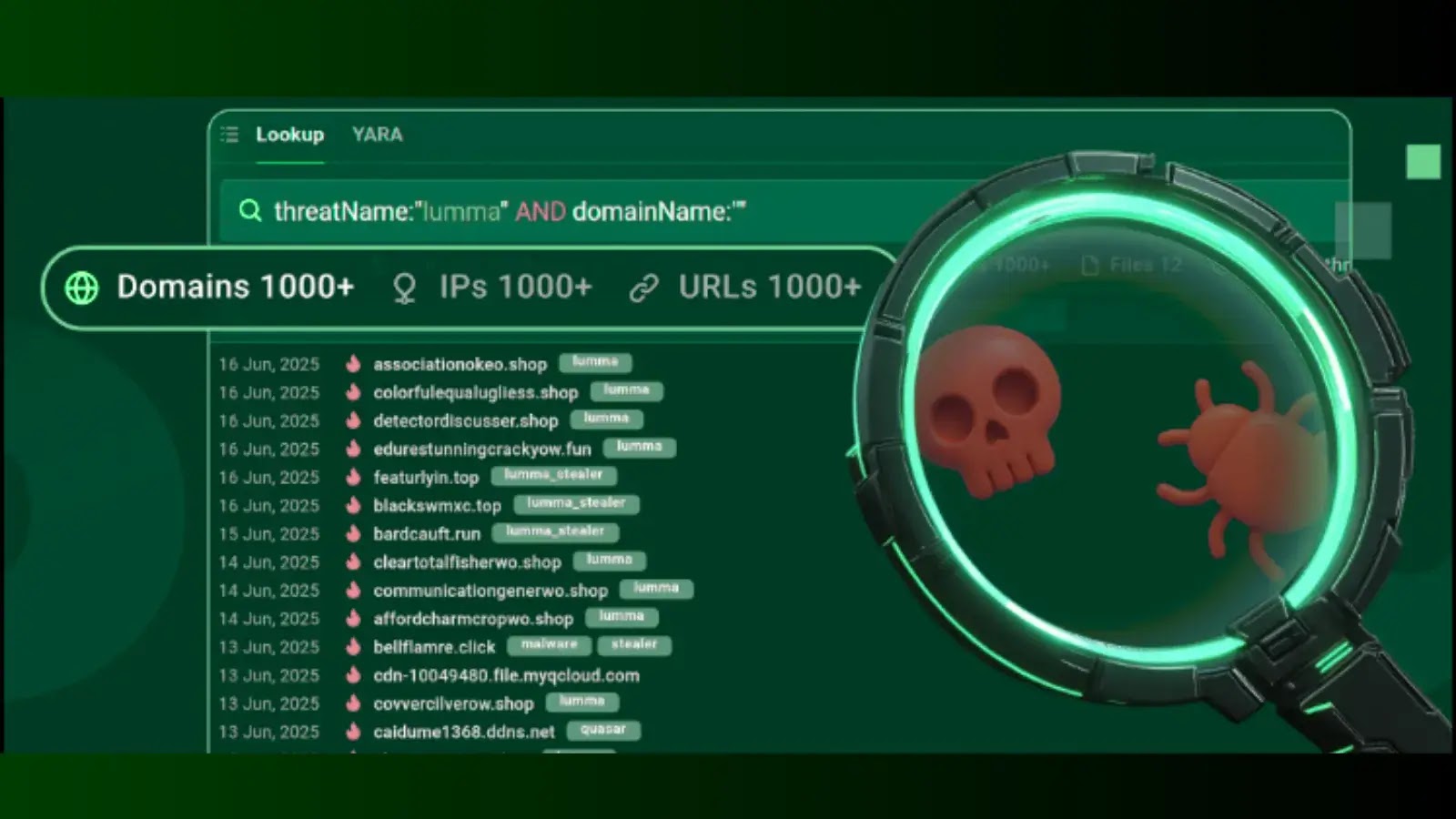
Detecting fast flux activity remains an ongoing challenge due to its resemblance to legitimate dynamic hosting practices like content delivery networks (CDNs).
However, cybersecurity agencies recommend several measures:
- DNS Analysis: Monitor DNS query logs for domains exhibiting high entropy or frequent IP address rotations.
- Time-to-Live (TTL) Analysis: Identify domains with unusually low TTL values indicative of fast flux behavior.
- Geolocation Inconsistencies: Analyze DNS resolution for inconsistent geolocation data linked to suspicious domains.
- Threat Intelligence Integration: Leverage feeds and reputation services to identify known fast flux domains.
Mitigation strategies include DNS and IP blocking, sinkholing malicious domains, reputational filtering, enhanced monitoring, and collaborative defense through information sharing initiatives.
Protective DNS services are also recommended for detecting and blocking fast flux-enabled threats.
Fast flux represents a persistent challenge for network security, enabling attackers to evade detection while maintaining robust infrastructure for malicious operations.
Cybersecurity agencies urge organizations to adopt multi-layered defense strategies combining DNS analysis, network monitoring, and threat intelligence.
By proactively addressing this threat, stakeholders can significantly bolster their defenses against fast flux-enabled attacks.
Find this News Interesting! Follow us on Google News, LinkedIn, & X to Get Instant Updates!