Cybersecurity researchers at Cofense Intelligence have uncovered an ongoing campaign where threat actors abuse Windows File Explorer to distribute malware.
By exploiting the legacy WebDAV protocol, attackers are tricking victims into downloading Remote Access Trojans (RATs) while bypassing traditional web browser security controls and some Endpoint Detection and Response (EDR) systems.
WebDAV Exploit
WebDAV (Web-based Distributed Authoring and Versioning) is an HTTP-based file management protocol.
Although Microsoft deprecated it in November 2023, it remains natively supported within Windows File Explorer.
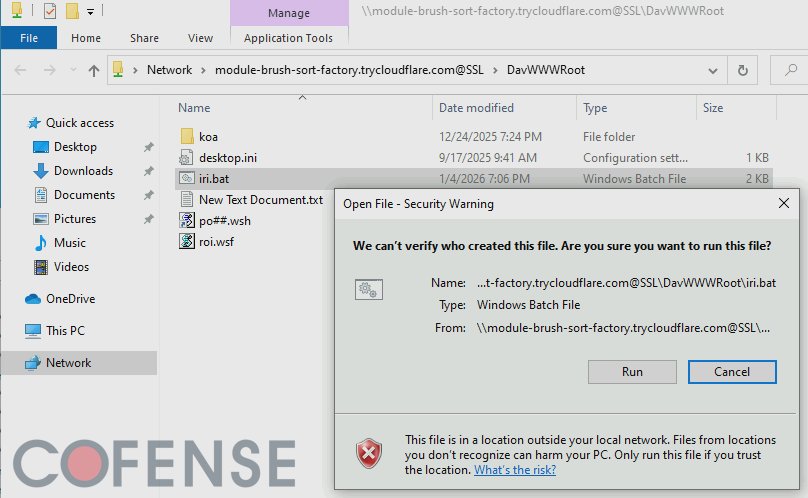
Attackers exploit this by sending malicious links that open remote WebDAV servers directly within File Explorer.
Because the interface looks like a standard local folder, victims are less suspicious of the files they are viewing.
Threat actors primarily use three methods to execute this attack: Direct Linking (using file:// URIs), URL shortcut files (.url), and LNK shortcut files (.lnk).
These files directly open remote paths or run malicious scripts from the attacker’s server. Interestingly, if a .url file contains a Windows UNC path, simply opening the local folder containing the shortcut triggers an automatic DNS lookup.
This inadvertently alerts the attacker that the payload is active on a victim’s machine.
To hide their malicious activities, attackers are heavily relying on free demo instances of Cloudflare Tunnels (trycloudflare[.]com) to host their WebDAV servers.
When a victim connects to the malicious WebDAV server, their network traffic is routed through legitimate Cloudflare infrastructure.
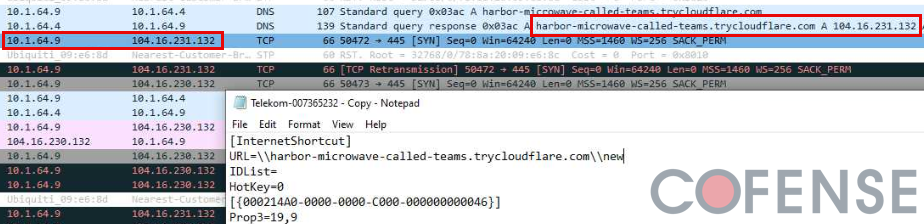
This makes detection difficult for security analysts who might dismiss the traffic as safe. Furthermore, these servers are short-lived, which prevents security researchers from analyzing the payloads after the campaign concludes.
Malware Payloads and Targeted Victims
According to Cofense, this tactic has been observed since February 2024, but campaign volume surged significantly in September 2024.
The primary payload for 87% of these attacks is multiple remote access trojans (RATs) delivered simultaneously.
The most popular malware families deployed in these attacks include XWorm RAT, Async RAT, and DcRAT.
The campaigns largely target European corporate networks through phishing emails.
Currently, 50% of the active threat reports associated with this tactic use German language emails featuring fake financial invoices, while another 30% utilize English language lures.
Indicators of Compromise (IOCs)
The following Cloudflare Tunnel domains have been observed hosting malicious WebDAV servers in recent campaigns. Security teams should monitor for unusual outbound traffic to these addresses.
| Cloudflare Tunnel Domain | Associated Threat Type |
|---|---|
tiny-fixtures-glossary-advantage[.]trycloudflare[.]com | Malicious WebDAV Server |
nasdaq-aged-sf-cheers[.]trycloudflare[.]com | Malicious WebDAV Server |
lose-croatia-acdbentity-lt[.]trycloudflare[.]com | Malicious WebDAV Server |
discounted-pressed-lc-vcr[.]trycloudflare[.]com | Malicious WebDAV Server |
skills-statute-alberta-demand[.]trycloudflare[.]com | Malicious WebDAV Server |
whats-menu-familiar-zshops[.]trycloudflare[.]com | Malicious WebDAV Server |
publicity-jenny-paintball-gilbert[.]trycloudflare[.]com | Malicious WebDAV Server |
Organizations should consider disabling WebDAV client services if they are not actively required for business operations.
Additionally, IT teams must monitor for unusual outbound SMB or WebDAV traffic, particularly connections attempting to access unauthorized internet resources via File Explorer.
Similar networking protocols like FTP and CIFS can also be abused using these same methods, so holistic network monitoring is essential.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.