Head Mare, a hacktivist group targeting Russia and Belarus, leverages phishing campaigns distributing WinRAR archives to exploit CVE-2023-38831 for initial access.
By deploying LockBit and Babuk ransomware, they encrypt victim systems and publicly disclose stolen data.
The group shares similarities with other anti-Russian hacktivists in tactics but employs more advanced access methods, as their operations, linked to PhantomDL malware activity, underscore the evolving threat landscape for Russian organizations.
A hacktivist group targeting Russian organizations primarily leverages publicly available tools like LockBit, Babuk, and Mimikatz for their attacks.
Free Webinar on Detecting & Blocking Supply Chain Attack -> Book your Spot
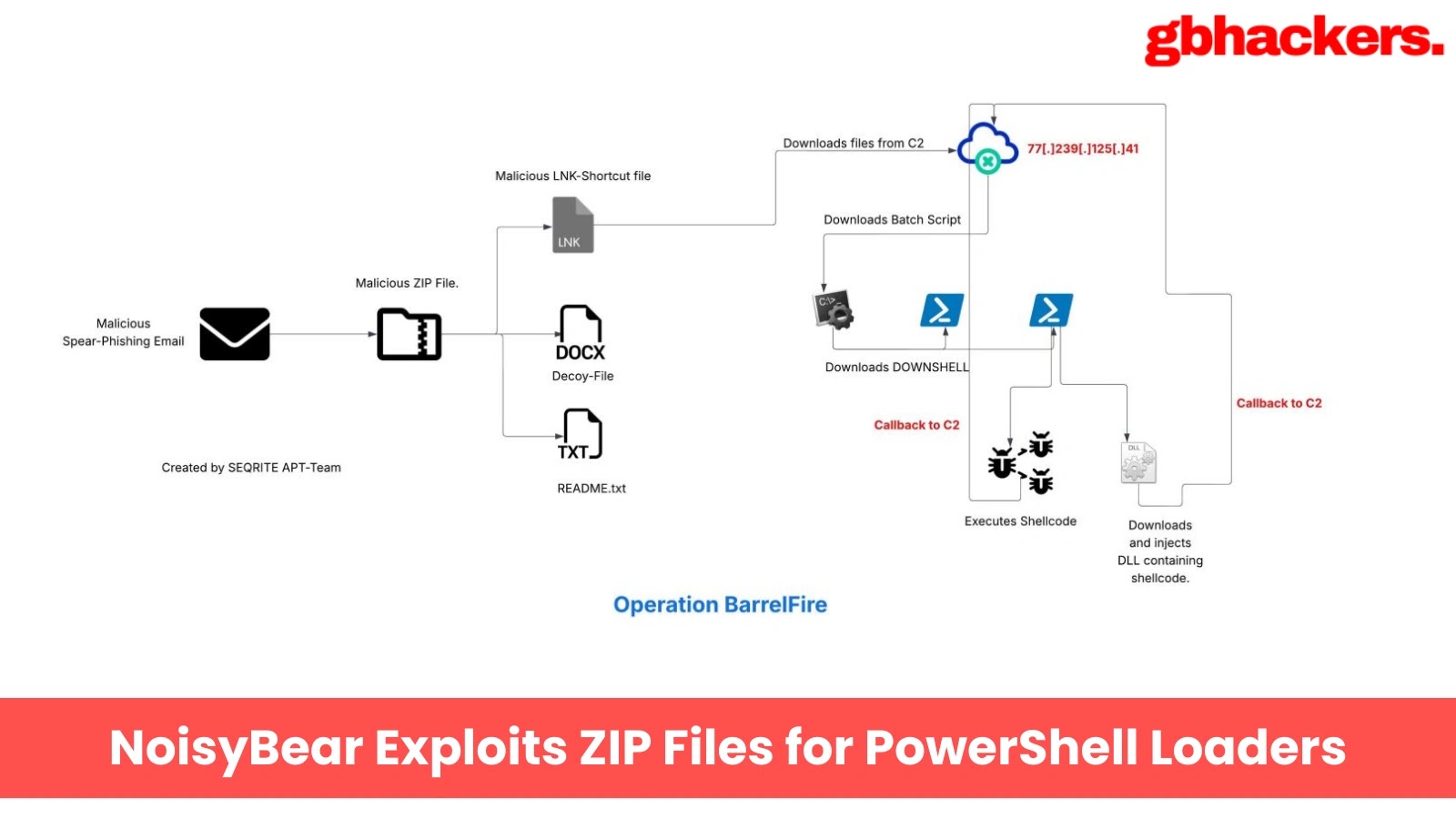
Their primary infection vector involves phishing campaigns distributing malicious archives containing custom malware, PhantomDL and PhantomCore, which exploit the WinRAR vulnerability CVE-2023-38831.
Once executed, these malware variants establish command-and-control channels, gather system information, and implement persistence mechanisms through registry modifications and scheduled tasks to maintain unauthorized access.
.webp)
Head Mare employs sophisticated evasion tactics, disguising malicious payloads as legitimate software like OneDrive and VLC and using common file names and locations to blend into system environments.
They leverage Sliver as a primary C2 framework, coupled with Garble obfuscation, to maintain covert command and control over compromised systems.
Their infrastructure includes VPS servers hosting various tools like PowerShell scripts for privilege escalation, Meterpreter for remote interaction, and PHP shells for command execution, demonstrating a versatile and adaptable attack toolkit.
.webp)
Attackers leverage rsockstun and ngrok to establish covert tunnels, enabling lateral movement within compromised networks.
They exploit vulnerabilities and gain initial access, employing tools like cmd, arp, and PowerShell to gather system information and credentials.
Mimikatz and XenAllPasswordPro are used for credential harvesting.
Ultimately, ransomware like LockBit and a custom Babuk variant are deployed to encrypt sensitive data and disrupt operations, with the latter specifically targeting ESXi environments and employing advanced encryption techniques.
.webp)
The Head Mare attacks leveraged publicly available LockBit ransomware builders, distributing the malware under various disguises.
Attackers employed a two-phase encryption process, initially using LockbitLite with limited file and free space wiping capabilities, followed by a more destructive LockbitHard variant.
Both versions were configured to encrypt file names and wipe free space, but LockbitHard had broader file deletion permissions.
The ransomware was typically installed on a user desktop or in ProgramData directories, and distinct ransom notes were generated.
Kaspersky Threat Intelligence identified Head Mare malware exclusively in Russia and Belarus.
Similarity analysis revealed connections between Head Mare samples and those from other groups targeting the same region, suggesting shared tactics.
Head Mare uniquely employs custom malware, PhantomDL and PhantomCore, along with the CVE-2023-38831 exploit, differentiating it from other regional threat actors, which underscores the need for heightened vigilance among Russian and Belarusian organizations.
Are you from SOC and DFIR Teams? Analyse Malware Incidents & get live Access with ANY.RUN -> Get 14 Days Free Access