The growing sophistication of software supply chain attacks is driven by widespread flaws in open-source and third-party commercial software, along with malicious campaigns that specifically target AI and cryptocurrency development pipelines, according to a ReversingLabs report.
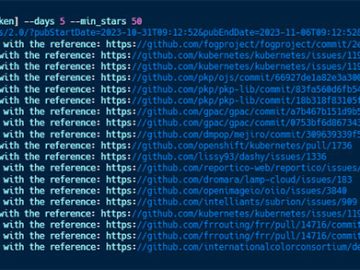
According to ReversingLabs data, open-source software remained a key element of supply chain risk in 2024. For example, incidents of exposed development secrets via publicly accessible, open-source packages rose 12% compared to 2023. And critical and exploitable software flaws continued to lurk in even the most widely used open source packages. A scan of 30 open source packages that account for more than 650 million total downloads across three leading open source package managers found an average of 6 critical-severity and 33 high-severity flaws per package.
But open-source software is just one source of software supply chain risk. A scan by ReversingLabs of more than two dozen widely used commercial-software binaries, including commercial and open-source operating systems, password managers, web browsers, and virtual private network (VPN) software, found evidence of software risks lurking in third-party commercial binaries.
Many of the packages scanned, received a failing security grade due to the discovery of exposed secrets, actively exploited software vulnerabilities, evidence of possible code tampering, and inadequate application hardening.
“The 2025 report highlights the challenges faced by software vendors and their enterprise buyers,” said Mario Vuksan, CEO of ReversingLabs. “First is the increasing sophistication of the attackers, and their willingness to invest years to plan and carry out their attacks. Second is the move beyond open source to target commercial software. This reinforces the need to establish better controls over the software we build and deploy. This is especially true with the rise of AI across the software supply chain.”
Gartner underscored this need for focus, saying that the “security of the software supply chain is now as critical as the security of the software itself.”
Third-party commercial software under attack
While much of the conversation about software supply chain security focuses on open-source software packages, the most prominent risks lie in closed-source, commercial software. To underscore this problem, ReversingLabs scanned 20 distinct versions of VPN clients from six prominent vendors and found worrying trends including:
- Seven of the 20 VPN packages contained one or more patch-mandated and/or exploited software vulnerabilities.
- Four of the 20 VPN packages scanned contained exposed developer secrets
While prominent risks lay in third-party commercial software, open-source software modules and code repositories still accounted for the vast majority of supply chain risks in 2024. ReversingLabs identified serious, exploitable software flaws, configuration errors, and other problems lurking in widely used open-source modules, which present a significant risk.
Additional examples of open-source risks include:
- Rampant “code rot:” Analysis of popular npm, PyPI, and RubyGems packages found that many widely used open-source modules contain old and outdated open-source and third-party software modules.
- ReversingLabs’s scan of an npm package with close to 3,000 weekly downloads and 16 dependent applications, identified:
- No code updates in more than 7 years
- 164 distinct code vulnerabilities with 43 rated “critical” severity and 81 rated “high” severity.
- Seven software vulnerabilities that are known to have been actively exploited by malware
Software producers warned by rising attacks on crypto apps
2024 saw a parade of sophisticated software supply chain attacks targeting cryptocurrency exchanges, wallets, and end-user applications. The crypto-focused attackers employed sophisticated and high-touch techniques to gain access to sensitive cryptocurrency applications and infrastructure. The report outlines research on detected malicious code in an established Python package, aiocpa.
The report also documents a series of malicious software supply chain campaigns targeting development infrastructure and code used by developers of AI and large language model machine learning applications.
Researchers discovered a malicious technique dubbed “nullifAI” in which malicious code was placed in Pickle serialization files, while evading protections built into the Hugging Face open source platform – a main resource for AI and ML developers.