Threat actors are using Domain Name System (DNS) tunneling to track when their targets open phishing emails and click on malicious links, and to scan networks for potential vulnerabilities.
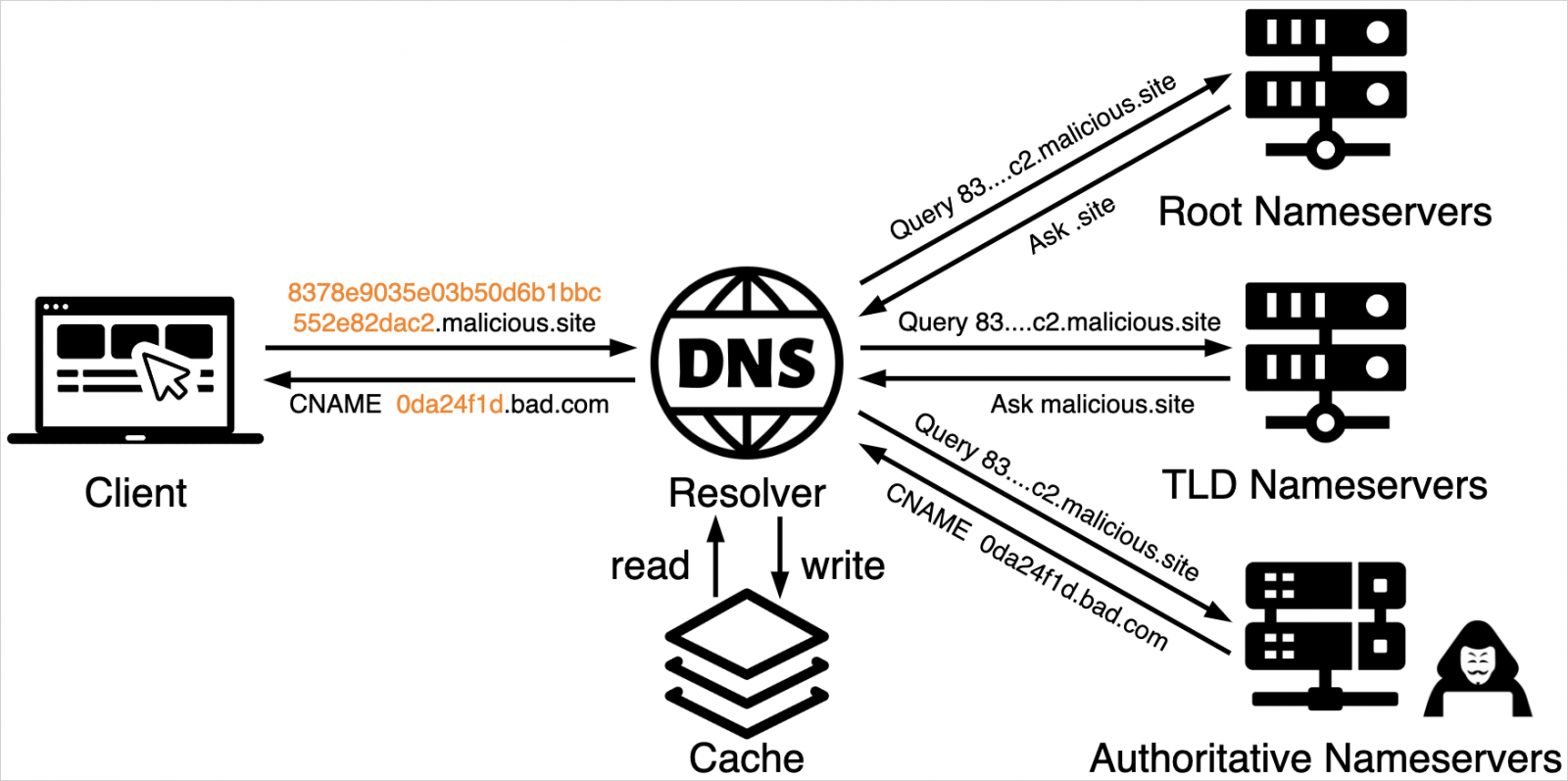
DNS tunneling is the encoding of data or commands that are sent and retrieved via DNS queries, essentially turning DNS, a fundamental network communication component, into a covert communications channel.
The threat actors encode the data in various ways, such as Base16 or Base64 or custom textual encoding algorithms, so they can be returned when querying DNS records, such as TXT, MX, CNAME, and Address records.
Hackers commonly use DNS tunneling to bypass network firewalls and filters, employing the technique for command and control (C2) and Virtual Private Network (VPN) operations. There are also legitimate DNS tunneling applications, such as for bypassing censorship.
Source: Unit 42
Palo Alto Networks’ Unit 42 security research team recently discovered additional use of DNS tunneling in malicious campaigns involving victim tracking and network scanning.
TrkCdn campaign
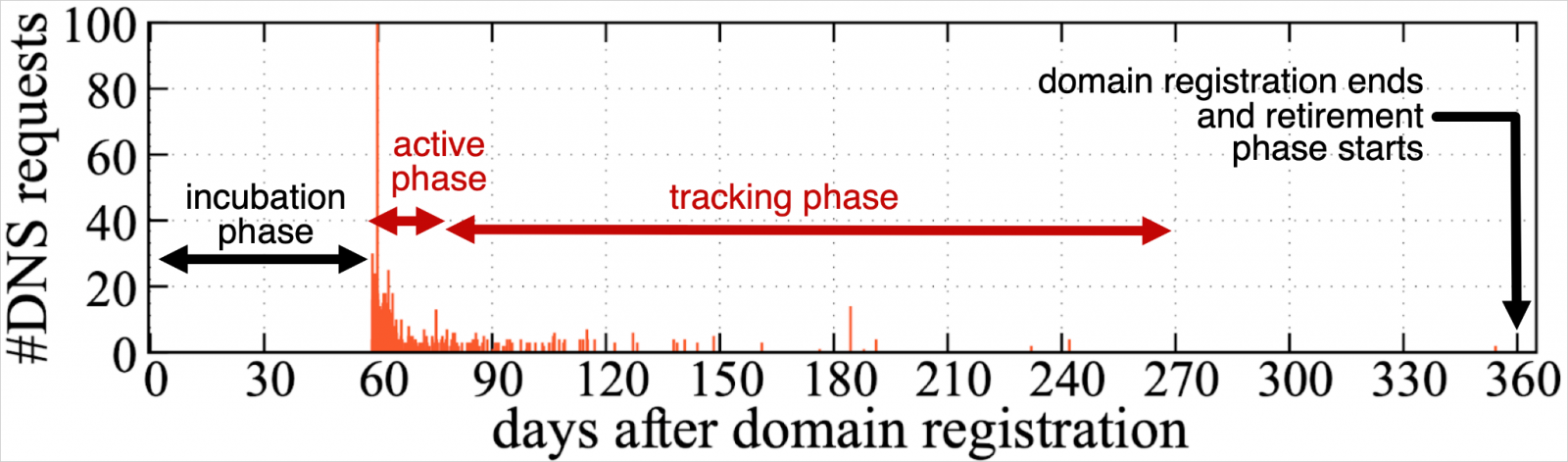
The first campaign, tracked as “TrkCdn,” focuses on tracking victim interactions with phishing email content.
The attackers embed content in an email that, when opened, performs a DNS query to attacker-controlled subdomains whose FQDN contains encoded content.
For example, 4e09ef9806fb9af448a5efcd60395815.trk.simitor[.]com. with 4e09ef9806fb9af448a5efcd60395815 being the md5 hash of unit42@not-a-real-domain[.]com, which resolves to a CNAME to a primary authoritative name server.
“Hence, even though the FQDNs vary across different targets, they are all forwarded to the same IP address used by cdn.simitor[.]com,” explains the researchers.
“This authoritative name server then returns a DNS result that leads to an attacker-controlled server that delivers attacker-controlled content. This content can include advertisements, spam, or phishing content.
This approach allows the attackers to evaluate their strategies, refine them, and confirm the delivery of malicious payloads to their victims.
Source: Unit 42
Unit 42’s report also highlights a similar campaign that uses DNS tunneling to track the delivery of spam messages, dubbed “SpamTracker.”
The SecShow campaign
The second campaign spotted by the analysts, codenamed “SecShow,” utilizes DNS tunneling to scan network infrastructures.
The attackers embed IP addresses and timestamps into DNS queries to map out network layouts and discover potential configuration flaws that can be exploited for infiltration, data theft, or denial of service.
The DNS queries used in this campaign were periodically repeated to enable real-time data gathering, detect status changes, and test the response of different network parts to unsolicited DNS requests.
Threat actors opt for DNS tunneling over more traditional methods like tracking pixels and regular network scanning tools for several reasons, including the ability to bypass security tools, avoid detection, and maintain operational versatility.
Unit 42 proposes that organizations implement DNS monitoring and analysis tools to monitor and analyze logs for unusual traffic patterns and anomalies, such as atypical or high-volume requests.
Additionally, it’s advisable to limit the DNS resolvers in the network to handle only the necessary queries, reducing the potential of DNS tunneling misuse.