Researchers identified a sophisticated cyberattack through a dormant Python Package Index (PyPI) package named Django-log-tracker, which was unexpectedly updated to deploy the NovaSentinel stealer malware.
This discovery highlights a significant threat to the software supply chain, emphasizing the need for heightened security measures among developers and organizations.
The django-log-tracker package, initially published in April 2022, remained inactive until a suspicious update on February 21, 2024, caught Phylum’s attention.
You can analyze such malware files, networks, modules, and registry activity with the ANY.RUN malware sandbox, and the Threat Intelligence Lookup which will let you interact with the OS directly from the browser.
The update’s divergence from the package’s GitHub repository activity suggested a potential compromise of the developer’s PyPI account. This incident marks a concerning trend of attackers targeting dormant packages to execute supply chain attacks.
The malicious update stripped the package to its bare essentials, leaving only an __init__.py and example.py file, both containing identical, malicious code.
Four sites on VirusTotal marked the exe as dangerous. We can easily get the binary’s data out because it turns out to be an NSIS launcher when we look at it in more detail. It has an Electron app inside.
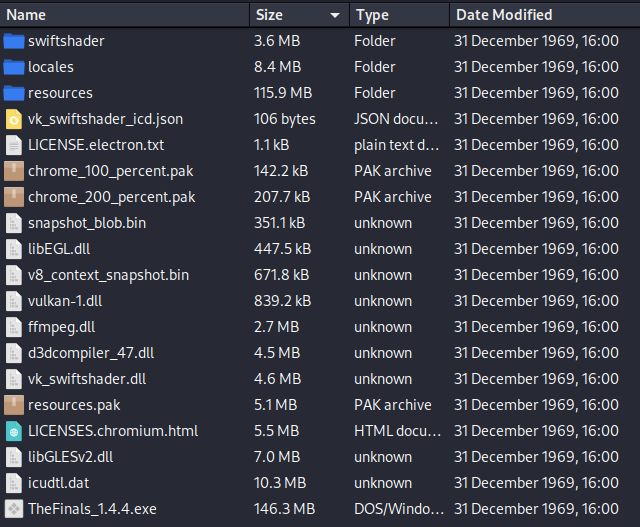
Upon execution, this code downloads and runs an executable named “Updater_1.4.4_x64.exe” from a remote server. The executable is embedded with the NovaSentinel stealer malware in Windows, known for its capabilities to exfiltrate sensitive information from infected systems.
NovaSentinel, first documented by Sekoia in November 2023, has been distributed through fake Electron apps on websites offering video game downloads. This recent PyPI package compromise represents an attempted supply chain attack, leveraging the trust within the developer community to spread malware.
The django-log-tracker package had been downloaded 3,866 times, with the rogue version 1.0.4 downloaded 107 times on the day of its publication. Phylum’s prompt detection and reporting led to the package’s removal from PyPI, preventing further downloads and potential infections.
Phylum’s discovery underscores the importance of vigilance and the implementation of robust security practices when dealing with third-party packages. Developers and organizations are encouraged to scrutinize package updates, especially those from dormant projects, and to employ automated security tools capable of detecting anomalous activities.
In this case, You can try Perimeter81 malware protection that blocks Trojans, ransomware, spyware, rootkits, worms, and zero-day vulnerabilities, which may wreck your network.





