A massive ad fraud campaign named “SubdoMailing” is using over 8,000 legitimate internet domains and 13,000 subdomains to send up to five million emails per day to generate revenue through scams and malvertising.
The campaign is called “SubdoMailing, as the threat actors hijack abandoned subdomains and domains belonging to well-known companies to send their malicious emails.
As these domains belong to trusted companies, they gain the benefit of being able to bypass spam filters and, in some cases, take advantage of configured SPF and DKIM email policies that tell secure email gateways that the emails are legitimate and not spam.
Some notable brands that fell victim to this domain hijacking campaign include MSN, VMware, McAfee, The Economist, Cornell University, CBS, NYC.gov, PWC, Pearson, Better Business Bureau, Unicef, ACLU, Symantec, Java.net, Marvel, and eBay.
These renowned brands involuntarily lend legitimacy to the fraudulent emails and help them pass through security filters.
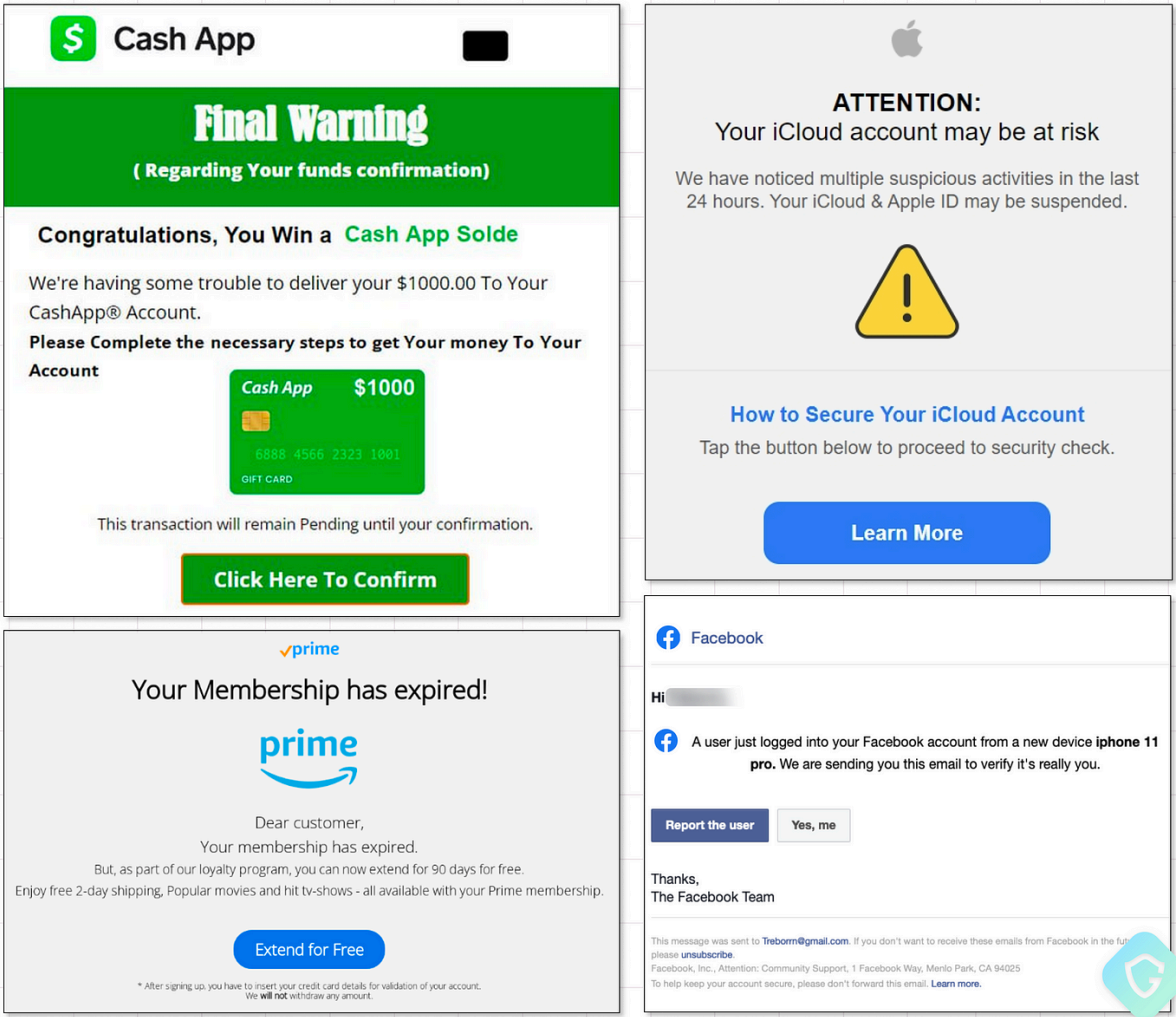
Clicking on the embedded buttons in the emails takes users through a series of redirections, generating revenue for the threat actors via fraudulent ad views. Ultimately, the user arrives at fake giveaways, security scans, surveys, or affiliate scams.
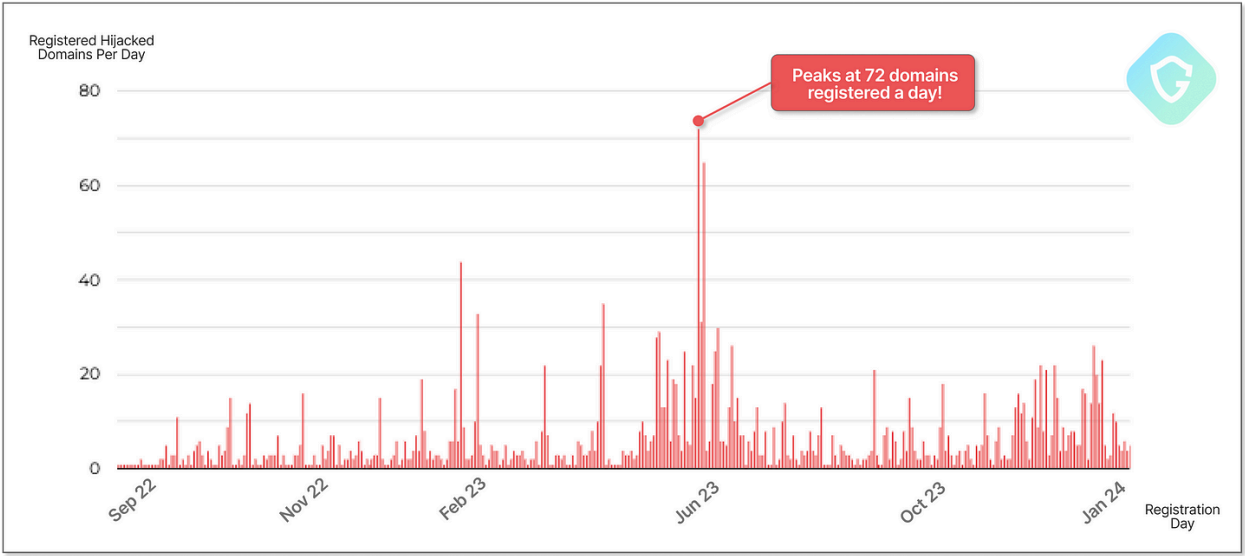
Guardio Labs researchers Nati Tal and Oleg Zaytsev discovered the ad fraud campaign and reported that the operation has been underway since 2022.
Source: Guardio Labs
Hijacking domains for spamming
Guardio Labs’ investigation began with detecting unusual patterns in email metadata, which led to the discovery of a vast subdomain hijacking operation.
A case study of an email falsely authorized by MSN showcases the variety of tactics used by the attackers to make their emails appear legitimate and evade blocks, including abusing SPF (Sender Policy Framework) checks, DKIM (DomainKeys Identified Mail), and DMARC (Domain-based Message Authentication, Reporting, and Conformance) protocols.
These email policies are used to prove to secure email gateways that the sender of an email is legitimate and should not be treated as spam.
Source: Guardio Labs
The SubdoMailing campaign targets domains and subdomains of reputable organizations, attempting to hijack them primarily through CNAME hijacking and SPF record exploitation.
In the CNAME attacks, the threat actors scan for subdomains of reputable brands with CNAME records pointing to external domains that are no longer registered. They then register these domains themselves through the NameCheap service.
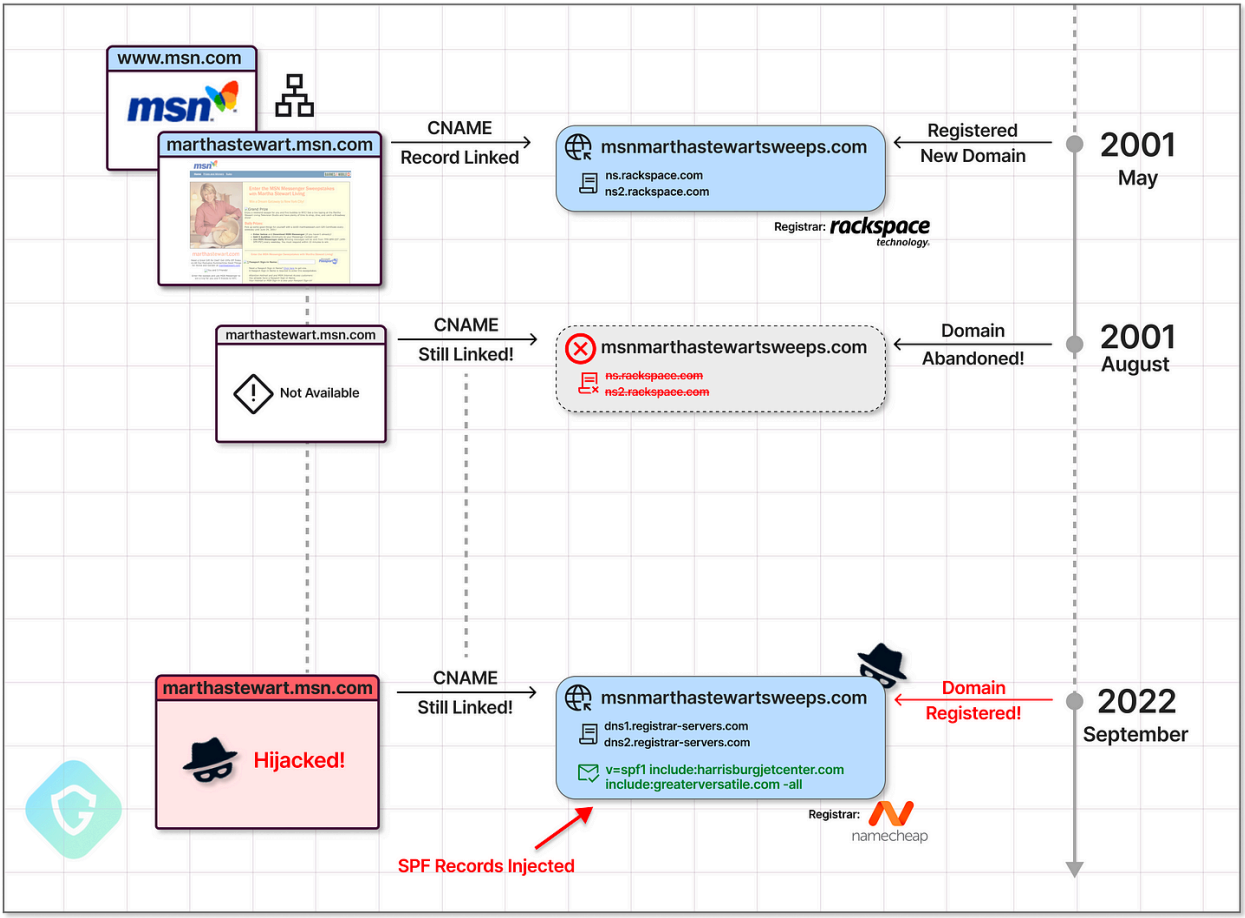
Source: Guardio Labs
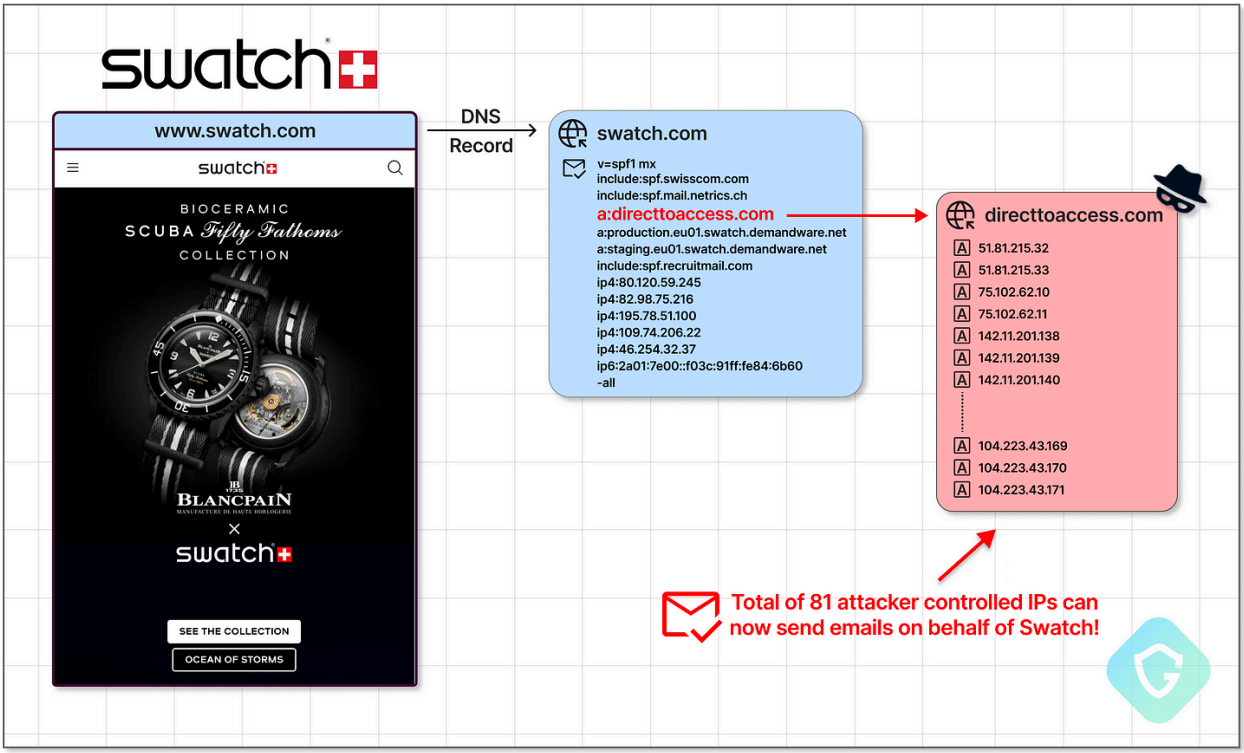
The second method involves looking at SPF records of target domains that use the “include:” configuration option pointing to external domains that are no longer registered.
The SPF include option is used to import allowed email senders from the external domain, which is now under the threat actor’s control.
The attackers register these domains and then change their SPF records to authorize their own malicious email servers. This makes the threat actor’s emails appear to legitimately come from a reputable domain, like MSN.
Source: Guardio Labs
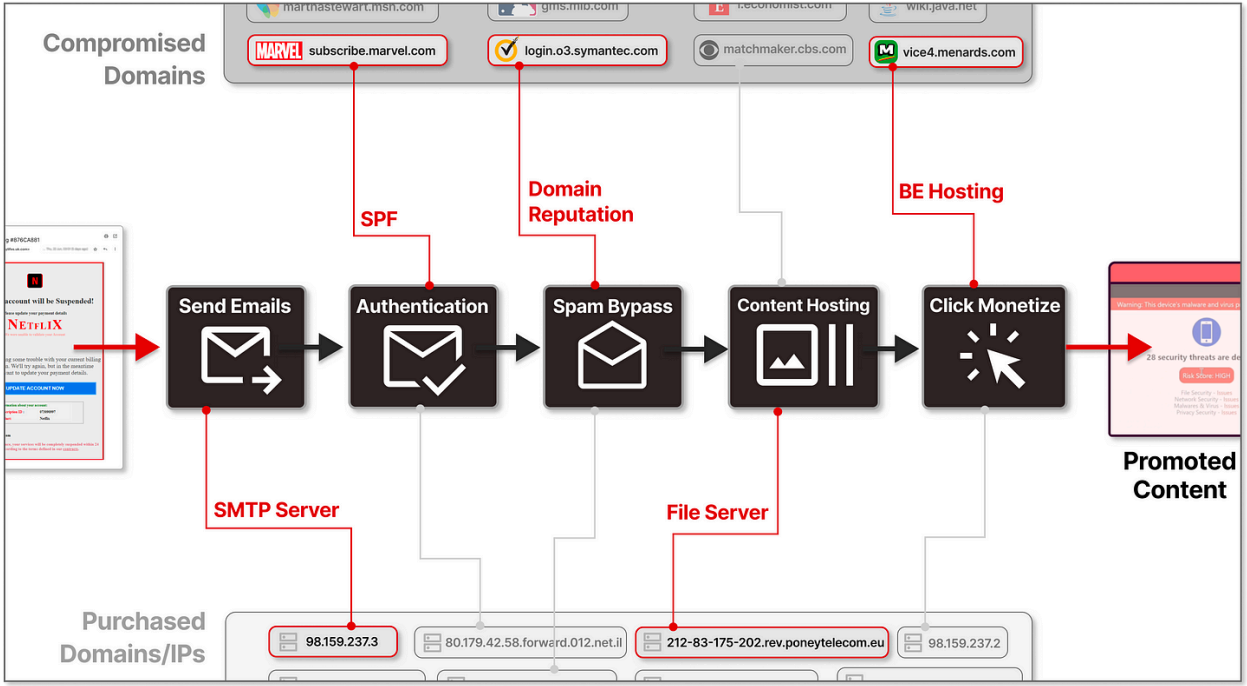
The operation generally leverages the hijacked domains for sending spam and phishing emails, hosting phishing pages, or hosting deceptive advertising content.
A massive campaign
Guardio Labs attributes the campaign to a threat actor they call “ResurrecAds,” who systematically scans the web for domains that can be hijacked, securing new hosts and IP addresses and making targeted domain purchases.
The threat actor constantly refreshes a vast network of hijacked and acquired domains, SMTP servers, and IP addresses to maintain the operation’s scale and complexity.
Source: Guardio Labs
Guardio Labs says SubdoMailing uses nearly 22,000 unique IPs, a thousand of which appear to be residential proxies.
Currently, the campaign operates through globally distributed SMTP servers configured to disseminate fraudulent emails through a massive network of 8,000 domains and 13,000 subdomains.
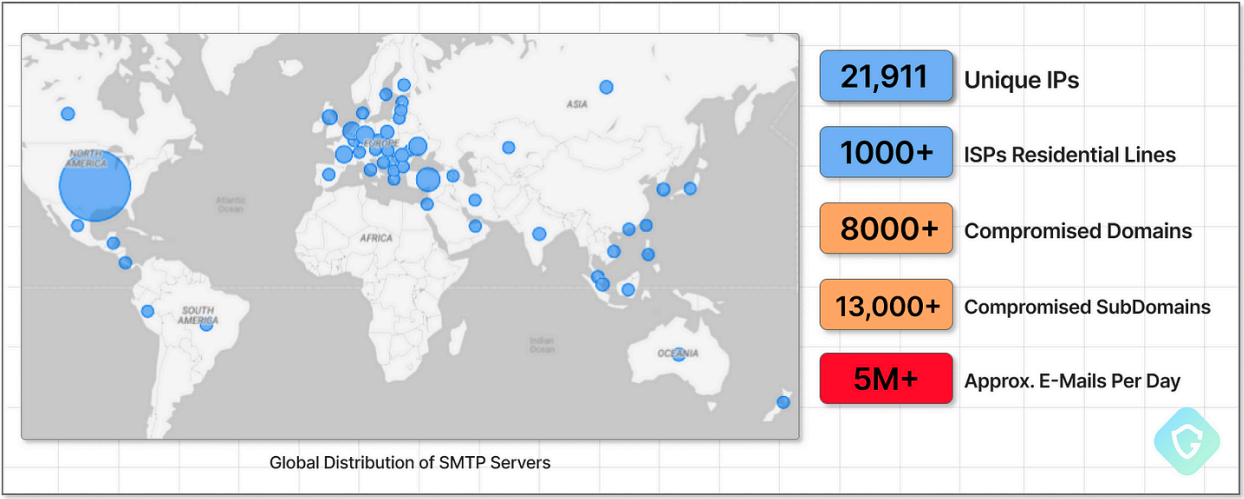
Source: Guardio Labs
The number of emails reaching targets surpasses 5,000,000 daily. While the attacker’s profit from this is impossible to appreciate, the scale of the operation and volume of the fraudulent emails are undeniably massive.
Guardio Labs has created a SubdoMailing checker site that can allow domain owners to detect if their brand is being abused and take action to stop or prevent it.






