Hydra Saiga is running a long-running espionage campaign that abuses Telegram as command-and-control (C2) to infiltrate critical utilities in Central Asia and exfiltrate sensitive data from government and infrastructure networks.
The first known Hydra Saiga activity dates to December 2024, when an executable named “Letter from the Permanent Representative of Turkmenistan to the UN addressed to the UN Secretary General regarding the launch.exe” was uploaded to VirusTotal.
This file acts as a loader, previously documented in Silent Lynx research, and launches a PowerShell backdoor that uses Telegram as a C2 channel.
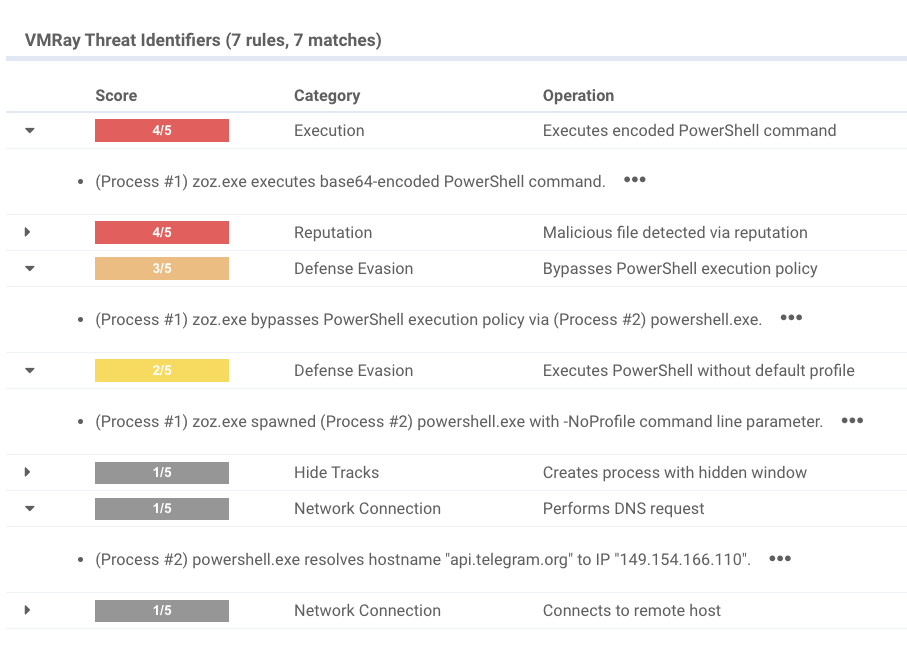
Analysis in VMRay shows the loader executing an embedded PowerShell script, bypassing PowerShell execution policy, and performing DNS lookups to the Telegram API domain.
Pivoting on these behaviours reveals related samples dating back to August 2024, often delivered in ISO or RAR archives attached to phishing emails, and frequently accompanied by local-language decoy documents referencing regional events and institutions.
The loader contains a base64-encoded PowerShell blob that decodes into a fully functional backdoor using the Telegram Bot API /getUpdates endpoint to poll for operator commands and to upload or download files via a Telegram chat.
Hydra Saiga Espionage
Pivoting on an attacker IP, 185.106.92[.]127, exposes a second initial access vector relying on phishing emails targeting the Royal Oman Police.
Analysis identified at least 34 compromised organizations across 8 countries, with reconnaissance activity extending to over 200 additional targets globally.
The email spoofed a researcher at the Nile Research Institute and carried a password-protected RAR containing a Word document titled “إنجازات الربع الثالث 2024 (003).doc” with malicious macros that execute on document open.
These macros spawn PowerShell, download a script from the same IP, and run it, as confirmed by dynamic analysis.
The downloaded script is a lightly obfuscated PowerShell backdoor that uses Invoke-Expression to run attacker commands and returns command output back to the same infrastructure.
Around the same time, the same IP also hosted a Meterpreter executable, suggesting operators were prepared to switch to more feature-rich tooling during post-exploitation.
Captured Telegram C2 command streams show a very manual, hands-on-keyboard style of operation, heavily using built-in Windows tools throughout the intrusion lifecycle.
Persistence is achieved mainly through scheduled tasks and registry modifications, typically pointing back to updated versions of the PowerShell Telegram C2 backdoor.
For credential access, operators exfiltrate plaintext “passwords.txt” files, deploy FakeLogonScreen to capture credentials at logon, export SAM and SECURITY hives for offline cracking, enable WDigest to store credentials in memory, and dump LSASS to extract them.
Lateral movement relies on nltest for domain controller discovery followed by WMI or PsExec to deliver and run reverse SOCKS5 proxy clients inside the network.
Collection and exfiltration are systematic: operators take screenshots, compress targeted documents with RAR, and exfiltrate archives via curl to C2 servers.

Defense evasion includes turning off Microsoft Defender features and firewall rules to keep C2 channels and reverse proxies unobstructed.
They also deploy a PyInstaller-based stealer that decrypts Chrome “Login Data,” later upgraded to a Golang infostealer that targets multiple browsers and exports credentials, cookies, and history in CSV format.
Hydra Saiga performs extensive external reconnaissance, using platforms like Censys and Shodan to scan exposed hosts and assess potential targets before intrusion.
They then run Acunetix for web vulnerability scanning, search for default passwords, use public password lists for brute forcing, and abuse compromised email accounts to harvest VPN configuration details and distribute further phishing lures.
Some operators have experimented with the Havoc C2 framework to extend their post-exploitation capabilities.
Their infrastructure choices favour anonymity: C2 servers are rented from providers such as BitLaunch and PSB Hosting, and domains are registered via QHoster with cryptocurrency payments.

Analysis of command timestamps from Telegram C2 reveals a consistent UTC+5 working pattern, with clear office-hour peaks and activity gaps aligning with Kazakhstan’s public holidays in March 2025.
Combined with targeting patterns and prior reporting, this supports assessment that Hydra Saiga acts in support of Kazakhstani state interests and overlaps with the Tomiris cluster, which is known to use Telegram-based implants like Telemiris and Rust backdoor JLORAT.
Between April 2023 and August 2025, Hydra Saiga compromised at least 34 organizations in eight countries, primarily in government, energy, critical infrastructure, healthcare, and legal sectors, with a concentration in Central Asia plus victims in Egypt and Georgia.
Notably, a focused “Water Campaign” from late 2024 to early 2025 targeted water utilities, hydroelectric operators, and associated ministries along the Syr Darya and Amu Darya river systems, directly intersecting regional water and energy security.
Parallel activity against exposed SCADA endpoints and a regional Russian gas distribution system further underscores the group’s interest in gas and industrial control environments that underpin critical utilities.
Defenders can blunt Hydra Saiga’s operations by first blocking access to api.telegram.org where feasible, disrupting the Telegram Bot API C2 channel used by their PowerShell implants.
Continuous monitoring for unusual outbound connections to known attacker autonomous systems and infrastructure providers, combined with close scrutiny of login anomalies and spikes in outbound email from government mail servers, helps surface both compromised hosts and abused email accounts.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.