Numerous iOS apps are using background processes triggered by push notifications to collect user data about devices, potentially allowing the creation of fingerprinting profiles used for tracking.
According to mobile researcher Mysk, who discovered this practice, these apps bypass Apple’s background app activity restrictions and constitute a privacy risk for iPhone users.
“Apps should not attempt to surreptitiously build a user profile based on collected data and may not attempt, facilitate, or encourage others to identify anonymous users or reconstruct user profiles based on data collected from Apple-provided APIs or any data that you say has been collected in an ‘anonymized,’ ‘aggregated,’ or otherwise non-identifiable way,” reads a section of Apple App Store review guidelines.
After analyzing what data is sent by iOS background processes when receiving or clearing notifications, Mysk found that the practice was far more prevalent than previously thought, involving many apps with a considerable user base.
Wake up and collect data
Apple designed iOS not to allow apps to run in the background to prevent resource consumption and for better security. When not using an app, they are suspended and eventually terminated, so they can’t monitor or interfere with foreground activities.
In iOS 10, though, Apple introduced a new system that allows apps to quietly launch in the background to process new push notifications before the device displays them.
The system allows apps that receive push notifications to decrypt the incoming payload and download additional content from their servers to enrich it before it’s served to the user. Once this process is done, the app is terminated again.
Through testing, Mysk found that many apps abuse this feature, treating it as a window of opportunity to transmit data about a device back to their servers. Depending on the app, this includes system uptime, locale, keyboard language, available memory, battery status, storage use, device model, and display brightness.
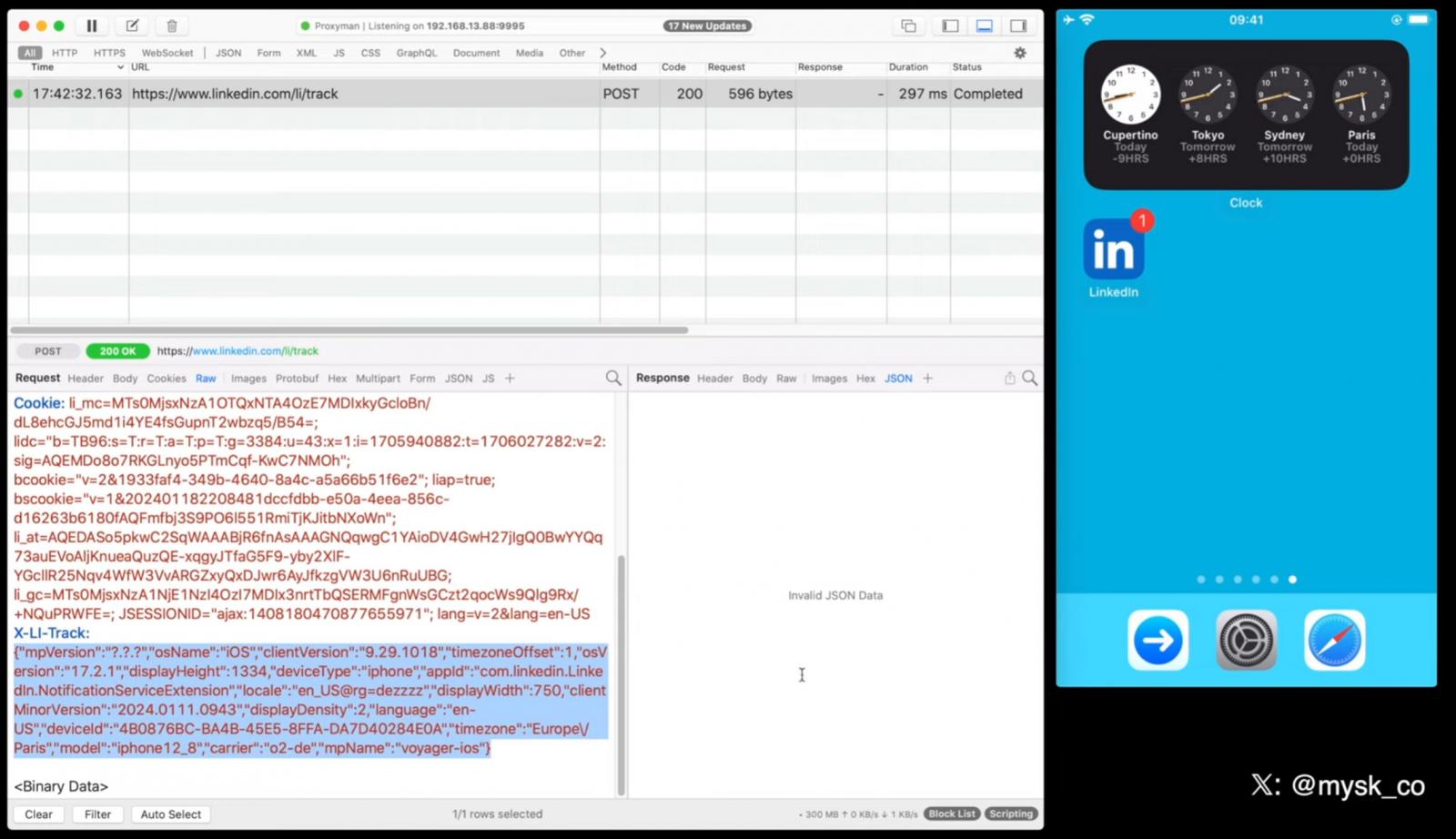
Source: Mysk
The researcher believes this data can be used for fingerprinting/user profiling, allowing for persistent tracking, which is strictly prohibited in iOS.
“Our tests show that this practice is more common than we expected. The frequency at which many apps send device information after being triggered by a notification is mind-blowing,” explains Mysk in a post on Twitter.
Mysk created the following video displaying the network traffic exchange during the reception of push notifications by TikTok, Facebook, X (Twitter), LinkedIn, and Bing.
The apps were found to send a wide range of device data to their servers using services like Google Analytics, Firebase, or their own proprietary systems.
Mitigating the issue
Apple will plug the gap and prevent further abuse of push notification wake-ups by tightening restrictions on using APIs for device signals.
Mysk told BleepingComputer that starting in Spring 2024, apps will be required to declare precisely why they need to use APIs that can be abused for fingerprinting.
These APIs are used to retrieve information about a device, such as its disk space, system boot time, file timestamps, active keyboards, and user defaults.
If apps do not properly declare their use of these APIs and what they are being used for, Apple says that they will be rejected from the App Store.
Until that happens, iPhone users who want to evade this fingerprinting should disable push notifications entirely. Unfortunately, making notifications silent will not prevent abuse.
To disable notifications, open ‘Settings,’ head to ‘Notifications,’ select the app you want to manage notifications for and tap the toggle to disable ‘Allow Notifications.’
In December, it was revealed that governments were requesting push notification records sent through Apple’s and Google’s servers as a way to spy on users.
Apple said that the US government prohibited them from sharing any information on these requests and has since updated their transparency reporting.