Today, Ivanti warned of two more vulnerabilities impacting Connect Secure, Policy Secure, and ZTA gateways, one of them a zero-day bug already under active exploitation.
The zero-day flaw (CVE-2024-21893) is a server-side request forgery vulnerability in the gateways’ SAML component that enables attackers to bypass authentication and access restricted resources on vulnerable devices.
A second flaw (CVE-2024-21888) in the gateways’ web component allows threat actors to escalate privileges to those of an administrator.
“As part of our ongoing investigation into the vulnerabilities reported on 10 January in Ivanti Connect Secure, Ivanti Policy Secure and ZTA gateways, we have discovered new vulnerabilities. These vulnerabilities impact all supported versions – Version 9.x and 22.x,” the company said today.
“We have no evidence of any customers being impacted by CVE-2024-21888 at this time. We are only aware of a small number of customers who have been impacted by CVE-2024-21893 at this time.”
“It is critical that you immediately take action to ensure you are fully protected,” Ivanti warned.
Ivanti has released security patches to address both flaws for some affected ZTA and Connect Secure versions, and it provides mitigation instructions for devices still waiting for a patch.
Patches for two more actively exploited zero-days
The company also released patches today for two other zero-days disclosed in early January— an authentication bypass (CVE-2023-46805) and a command injection (CVE-2024-21887)—chained in widespread attacks to deploy malware on vulnerable ICS, IPS, and ZTA gateways since January 11.
Ivanti also released mitigation measures to block attack attempts and recovery instructions designed to help restore compromised devices and bring them back online.
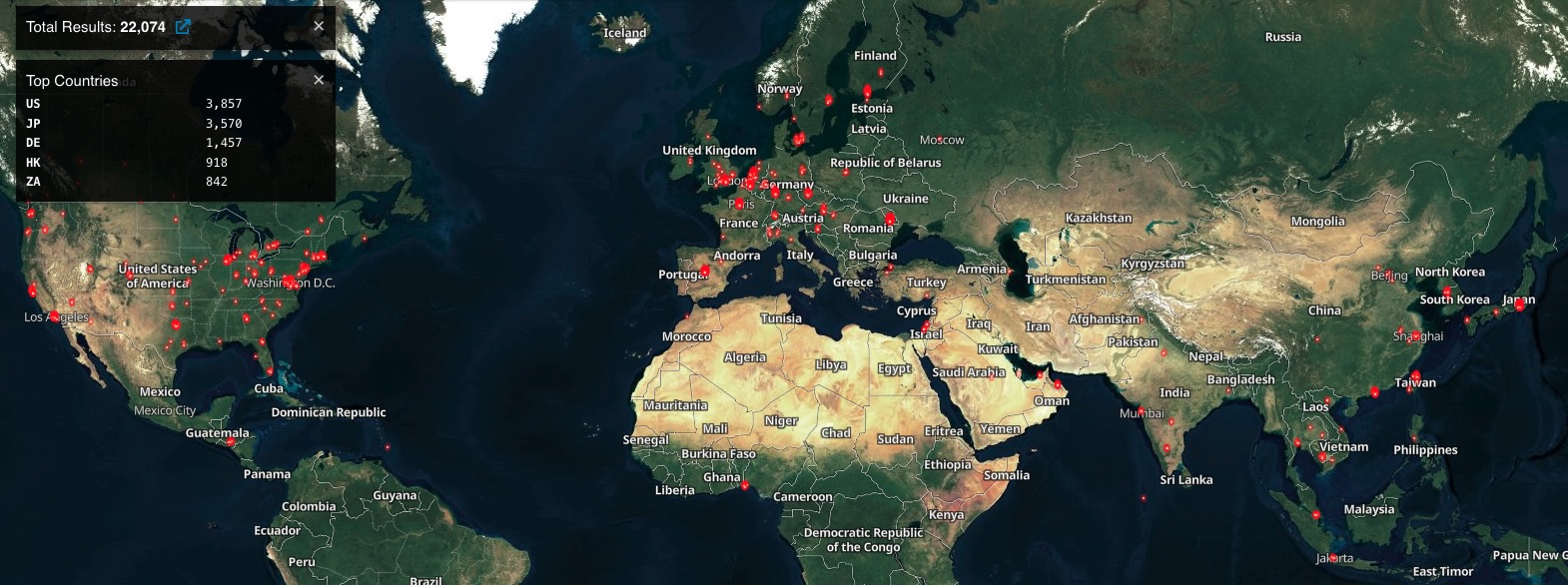
Threat monitoring platform Shadowserver currently tracks over 24,700 Internet-exposed ICS VPN gateways, over 7,200 in the United States (Shodan also sees over 22,000 Ivanti ICS VPNs exposed online).
Shadowserver also keeps track of compromised Ivanti VPN instances worldwide daily, with over 460 compromised devices discovered on January 30 alone.
CISA also issued 2024’s first emergency directive (ED 24-01), ordering federal agencies to immediately mitigate the CVE-2023-46805 and CVE-2024-21887 Ivanti zero-day flaws in response to mass exploitation by multiple threat actors.
When chained, the two zero-days let attackers move laterally within victims’ networks, steal data, and establish persistent access by deploying backdoors.
The list of victims discovered so far includes government and military organizations worldwide, national telecom companies, and defense contractors, as well as banking, finance, and accounting organizations and aerospace, aviation, and tech firms.
They all vary significantly in size, ranging from small businesses to some of the largest multinational conglomerates, including multiple Fortune 500 companies from various industry sectors.
Mandiant found five custom malware strains deployed in these extensive attacks that help threat actors steal credentials, deploy webshells, and drop additional malicious payloads.
Volexity and GreyNoise have also observed attackers deploying XMRig cryptocurrency miners and Rust-based malware payloads on some victims’ compromised systems.