Cybersecurity advisories from the Cybersecurity and Infrastructure Agency (CISA), the US Federal Bureau of Investigation (FBI), and the UK National Cyber Security Centre have shared reports on a rather interesting set of attackers leveraging the Jaguar Tooth malware.
According to a report by Cyble, a group of Russian state-sponsored attackers have access to the Jaguar Tooth malware and are actively exploiting the Simple Network Management Protocol (SNMP) vulnerabilities in unpatched Cisco Routers.
This report details the use of the Jaguar Tooth malware, its impact, and how hackers have gained access to exploit Cisco routers.
Jaguar Tooth malware and SNMP vulnerability exploitation
The advisory provides insight into the exploitation of SNMP vulnerabilities on Cisco Routers and the subsequent deployment of the notorious Jaguar Tooth malware.
The vulnerability, known as SNMP vulnerability or CVE-2017-6742, stems from a buffer overflow condition in the SNMP subsystem, which enables remote monitoring and configuration of network devices.
The severity of CVE-2017-6742 is categorized as High, as it allows authenticated remote attackers to execute code on affected systems or cause them to reload.

To exploit the vulnerability using SNMP Version 2c or earlier, attackers need the SNMP read-only community string associated with the targeted system.
In the case of SNMP Version 3, valid user credentials for the affected system are required. Devices that have SNMP enabled without explicitly excluding the affected MIBs or OIDs are considered vulnerable.
Jaguar Tooth malware: capabilities and modus operandi
Jaguar Tooth malware, a sophisticated malware variant, specifically targets Cisco IOS routers.
Once deployed, it automatically gathers device information, which is then transmitted via Trivial File Transfer Protocol (TFTP).
The malware exploits an authentication mechanism flaw, allowing unauthorized backdoor access to any local account without requiring authentication via Telnet or physical sessions.
By overriding the normal behavior of key functions, such as “askpassword” and “ask_md5secret,” Jaguar Tooth circumvents password verification, granting unauthorized access.

The malware also generates a new process known as “Service Policy Lock,” which involves automated data collection and exfiltration using TFTP.
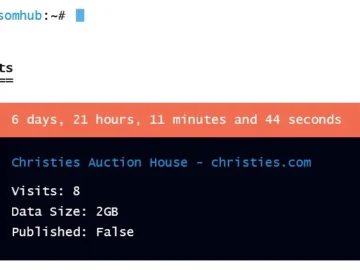
The stolen information includes crucial device details such as the running configuration, firmware version, flash memory directory listing, Address Resolution Protocol (ARP) entries, routing tables, interface information, and connections to other routers.
The report findings reveal that approximately 77,000 internet-exposed Cisco routers utilize SNMP, making them potential targets for exploitation. The geographic representation of exposed assets indicates a significant concentration in Russia, the United States, and India.
Impacted Cisco IOS versions and vulnerable MIBs
Cisco IOS versions 12.0 through 12.4 and 15.0 through 15.6 and IOS XE 2.2 through 3.17 are susceptible to CVE-2017-6742.
Furthermore, the Cisco cybersecurity advisory identifies several vulnerable MIBs (Management Information Bases) that put devices at risk:
- ADSL-LINE-MIB
- ALPS-MIB
- CISCO-ADSL-DMT-LINE-MIB
- CISCO-BSTUN-MIB
- CISCO-MAC-AUTH-BYPASS-MIB
- CISCO-SLB-EXT-MIB
- CISCO-VOICE-DNIS-MIB
- CISCO-VOICE-NUMBER-EXPANSION-MIB
- TN3270E-RT-MIB
Recent Cisco networking equipment vulnerabilities
Using Jaguar Tooth malware to tap unpatched vulnerabilities in Cisco Routers come as an interesting but inevitable development. Cybercriminals have been tapping bugs in Cisco products and services, owing to their global acceptability.
Cisco in April identified a critical vulnerability in its IOS Software and IOS XE Software, which could result in a denial of service (DoS) condition.
The vulnerability stems from improper resource management in the HTTP server code. Exploiting this flaw involves sending a large number of HTTP requests to a vulnerable device, potentially causing it to reload and resulting in a DoS situation.
Affected products include Cisco devices running vulnerable releases of IOS Software or IOS XE Software with the HTTP feature enabled. The vulnerability is present in all vulnerable releases of IOS XE Software within the 3SE and 3E release trains.
Days before the alert, Cisco disclosed another vulnerability in the Cloud Management for Catalyst migration feature of Cisco IOS XE Software that could allow a local attacker with authenticated access to gain root-level privileges on an affected device.
The vulnerability stemmed from insufficient memory protection in the Meraki migration feature of the device, enabling the attacker to manipulate the Meraki registration parameters and elevate privileges to root. Cisco has released software updates to address this vulnerability, and no workarounds are available.
This vulnerability affected Cisco Catalyst 9200 Series Switches and Catalyst 9300 Series Switches running vulnerable releases of Cisco IOS XE Software. Other Cisco products such as IOS Software, IOS XR Software, Meraki products, and NX-OS Software are confirmed not to be affected.