While the threat landscape continues to shift and evolve, attackers’ motivations do not, according to a Red Canary report. The classic tools and techniques adversaries deploy remain consistent–with some notable exceptions.
The report tracked MITRE ATT&CK techniques that adversaries abuse most frequently throughout the year, and two new and notable entries soared to the top 10 in 2023: email forwarding rule and cloud accounts.
Why do adversaries abuse cloud accounts?
Cloud account compromises are increasing in prevalence as organizations embrace software-as-a-service (SaaS) for critical productivity applications like email, file storage, and messaging, resulting in a substantial volume of data now being stored in the cloud. This shift is mirrored by adversaries too, who are finding just as much value in compromising cloud identities as they have historically in traditional endpoints.
Cloud accounts was the fourth most prevalent MITRE ATT&CK technique researchers detected in 2023, rising from 46th in 2022, increasing 16x in detection volume and affecting three times as many customers in 2023 than in 2022.
Detections for malicious email forwarding rules rose by nearly 600%, as adversaries compromised email accounts, redirected sensitive communications to archive folders and other places users are unlikely to look, and attempted to modify payroll or wire transfer destinations, rerouting money into the criminal’s account.
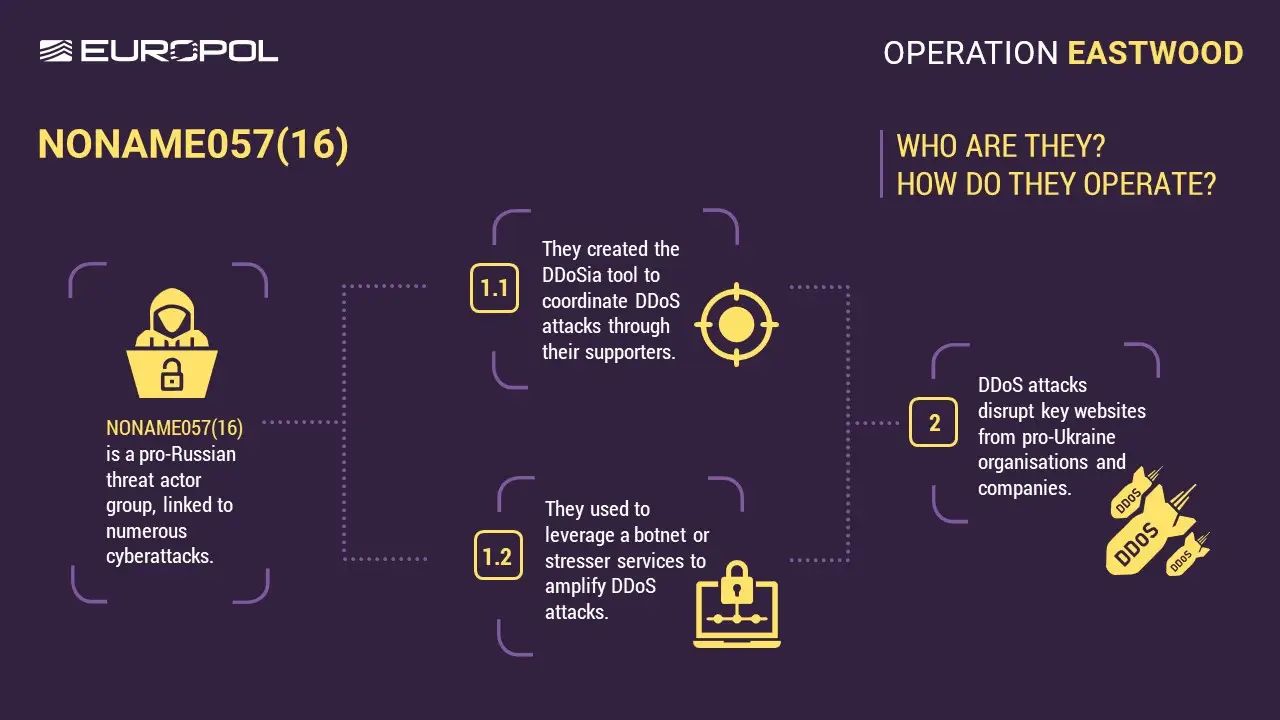
In 2023 we saw continued use of perennial favorite techniques. Phishing remains an evergreen issue, and this year adversaries continued to leverage a variety of file types in their phishing emails to deliver malicious payloads. SEO poisoning and malvertising continued to be popular, with new threats taking inspiration from established malware families. We saw a steady stream of new vulnerabilities exploited by adversaries from ransomware operators to state-sponsored threats, emphasizing the need to maintain patch levels both internally and within the supply chain.
Identity attacks
Half of the top threats are ransomware precursors that could lead to a ransomware infection if left unchecked, with ransomware continuing to have a major impact on businesses.
Despite a wave of new software vulnerabilities, humans remained the primary vulnerability that adversaries took advantage of in 2023, comprising identities to access cloud service APIs, execute payroll fraud with email forwarding rules, launch ransomware attacks, and more.
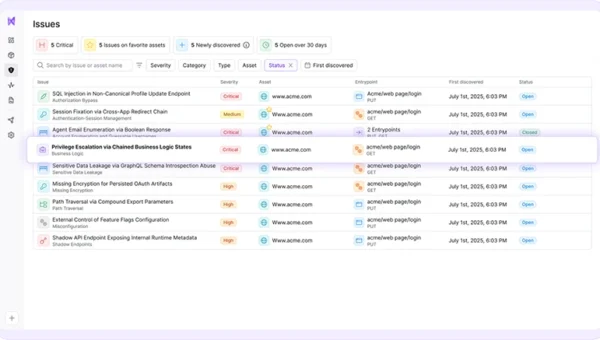
As organizations migrate to the cloud and rely on a growing array of SaaS applications to manage and access sensitive information, identities are the ties that bind all these systems together. Adversaries have quickly learned that these systems house the information they want and that valid and authorized identities are the most expedient and reliable way into those systems.
Researchers noted several broader trends impacting the threat landscape, such as the emergence of generative AI, the continued prominence of remote monitoring and management (RMM) tool abuse, the prevalence of web-based payload delivery like SEO poisoning and malvertising, the increasing necessity of MFA evasion techniques, and the dominance of brazen but highly effective social engineering schemes such as help desk phishing.
“The top 10 threats and techniques change minimally year over year, so the drift that we’re seeing in the 2024 report is significant. The rise of cloud account compromises from 46 to number 4 is unprecedented in our dataset–and it’s a similar story with email forwarding rules,” said Keith McCammon, Chief Security Officer, Red Canary.
“The golden thread connecting these modes of attack is identity. To access cloud accounts and SaaS applications, adversaries must compromise some form of identity or credential, and one that is highly privileged can grant an adversary untold access to valuable accounts, underscoring the critical importance of securing corporate identities and identity providers,” McCammon continued.
Emerging techniques for macOS, Microsoft, and Linux users to watch out for
In 2023 researchers detected more stealer activity in macOS environments than ever before, along with instances of reflective code loading and AppleScript abuse.
While many techniques like PowerShell and Windows Command Shell persist, there were some interesting variations, including:
- Adversaries compiled malicious installers with Microsoft’s new MSIX packaging tool–typically used to update existing desktop applications or install new ones–to trick victims into running malicious scripts under the guise of downloading legitimate software.
- Container escapes–where adversaries exploit vulnerabilities or misconfigurations in container kernels and runtime environments to “escape” the container and infect the host system.
- Reflective code loading is allowing adversaries to evade macOS security controls and run malicious code on otherwise hardened Apple endpoints.
Adversaries don’t target verticals; they target systems
The data shows that adversaries reliably leverage the same small set of 10-20 ATT&CK techniques against organizations, regardless of the victim’s sector or industry. However, adversaries do favor certain tools and techniques that may target systems and workflows that are common in specific sectors:
- Healthcare: Visual Basic and Unix Shell were more prevalent likely due to the different machinery and systems used within that industry.
- Education: Email forwarding and hiding rules were more common, likely due to a heavy reliance on email.
- Manufacturing: Replication through removable media, such as USBs, was more common—likely due to a reliance on air-gapped or pseudo air-gapped physical infrastructure and legacy systems.
- Financial services and insurance: Less “obvious” techniques, such as HTML smuggling and Distributed Component Object Model were more common, likely due to greater investments in controls and testing.