The Knight ransomware is being distributed in an ongoing spam campaign that pretends to be TripAdvisor complaints.
Knight ransomware is a recent rebrand of the Cyclop Ransomware-as-a-Service, which switched its name at the end of July 2023.
Who is Cyclops and Knight ransomware?
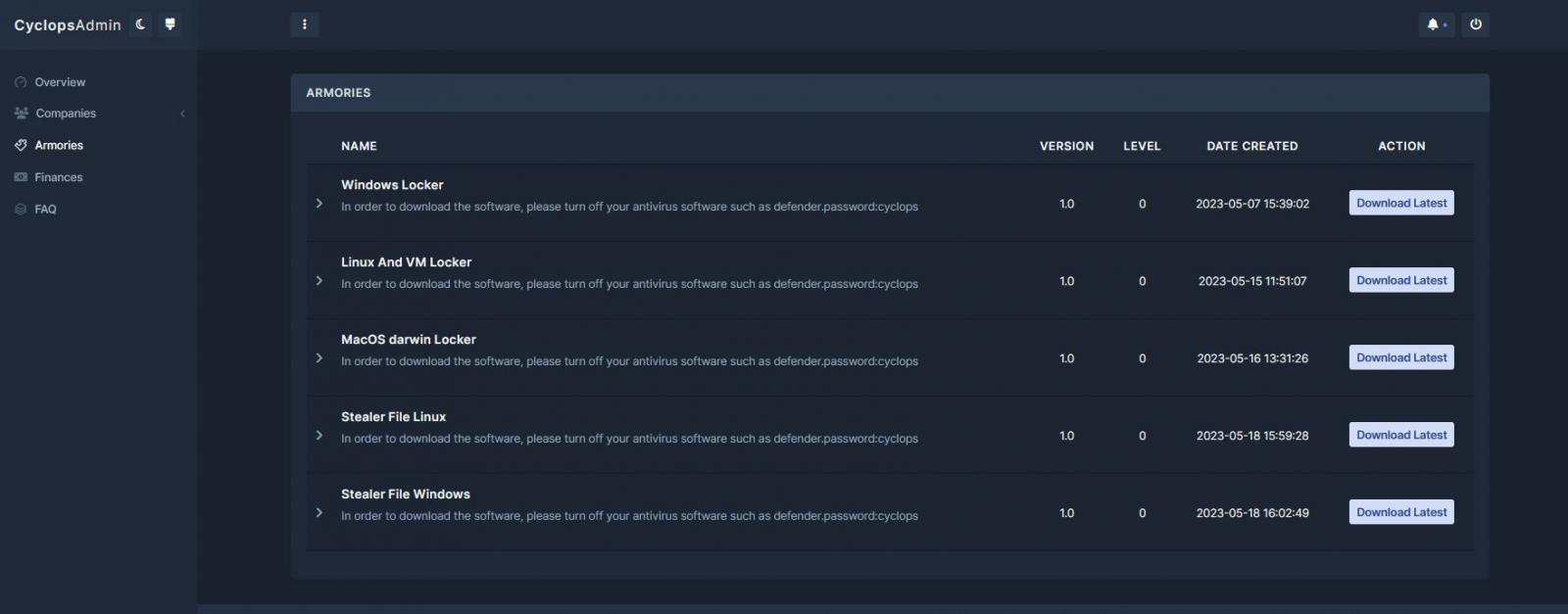
The Cyclops ransomware operation launched in May 2023 when the operators began recruiting affiliates for the new ransomware-as-a-service (RaaS) on the RAMP hacking forum.
A report by Uptycs explains that the operation launched with encryptors for Windows, macOS, and Linux/ESXi. The operation also offers affiliates information-stealing malware for Windows and Linux, which is not normally seen in RaaS operations.
Source: BleepingComputer
In addition to their normal encryptors, the operation offers a ‘lite’ version for use in spam and pray-and-spray mass distribution campaigns targeting large numbers of targeted users. This version appears to utilize a fixed ransom amount rather than negotiating with victims.
At the end of July, Cyclops rebranded as Knight, also stating they updated the lite encryptor to support ‘batch distribution’ and launched a new data leak site.
“We’ve updated our new panel and officially changed our name to Knight.We are looking for partners (of any kind) that!!!,” reads an announcement on the old Cyclops and new Knight data leak sites.
“We have also updated the lite version to support batch distribution.”
There are currently no victims or stolen files leaked on the Knight data leak site.
The Knight spam campaign
This week, Sophos researcher Felix spotted a new spam campaign pretending to be TripAdvisor complaints but distribute the Knight ransomware instead.
While the actual emails were not shared, Felix said that the emails include ZIP file attachments named ‘TripAdvisorComplaint.zip’ that contain an executable named ‘TripAdvisor Complaint – Possible Suspension.exe’ [VirusTotal].
A newer version of this campaign spotted and analyzed by BleepingComputer now includes an HTML attachment named ‘TripAdvisor-Complaint-[random].PDF.htm’ [VirusTotal].
When the HTML file is opened, it will use Mr.D0x’s Browser-in-the-Browser phishing technique to open what appears to be a browser window to TripAdvisor.
This fake browser window pretends to be a complaint submitted to a restaurant, asking the user to review it. However, clicking the ‘Read Complaint’ button will download an Excel XLL file named ‘TripAdvisor_Complaint-Possible-Suspension.xll’ [VirusTotal], as shown below.
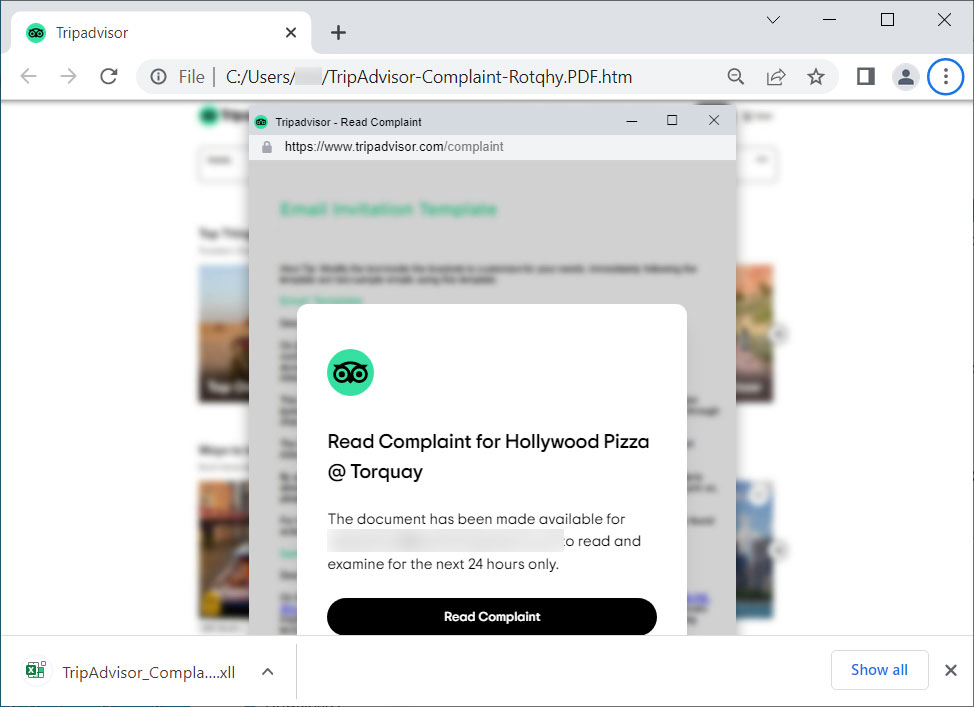
Source: BleepingComputer
This XLL file is created using Excel-DNA, which integrates .NET into Microsoft Excel to execute the malware when it is opened.
When you open the XLL, Microsoft Excel will detect the Mark of the Web (MoTW), added to files downloaded from the Internet, including email. If it detects the MoTW, it will not enable the .NET add-in built into the Excel document, nullifying the attack unless a user unblocks the file.
However, if there is no MoTW flag on the file, Excel will prompt the user as to whether they want to enable the add-in, as shown below.
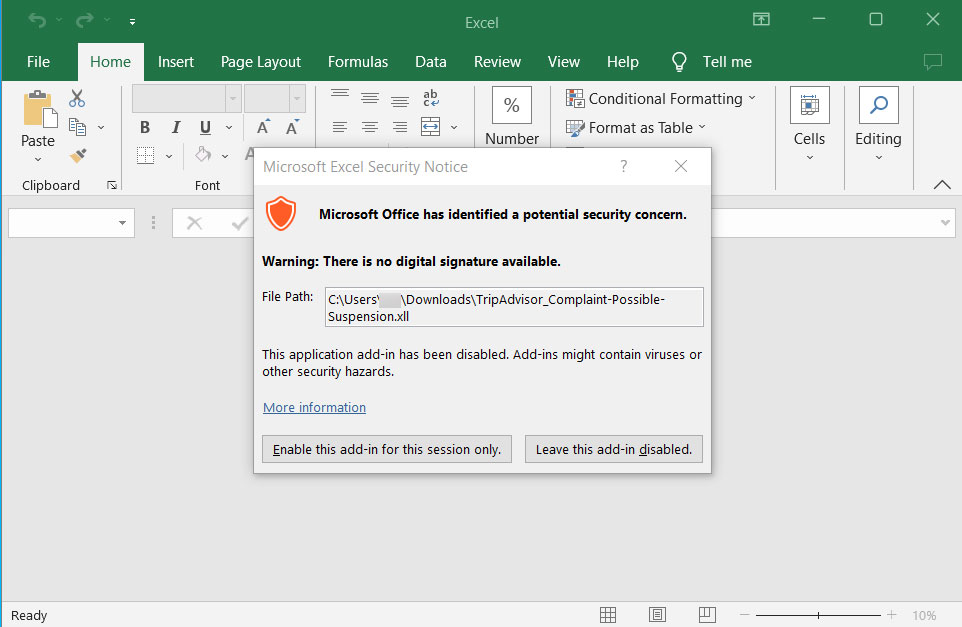
Source: BleepingComputer
Enabling the add-in will cause the Knight Lite ransomware encryptor to be injected into a new explorer.exe process and begin to encrypt the files on your computer.
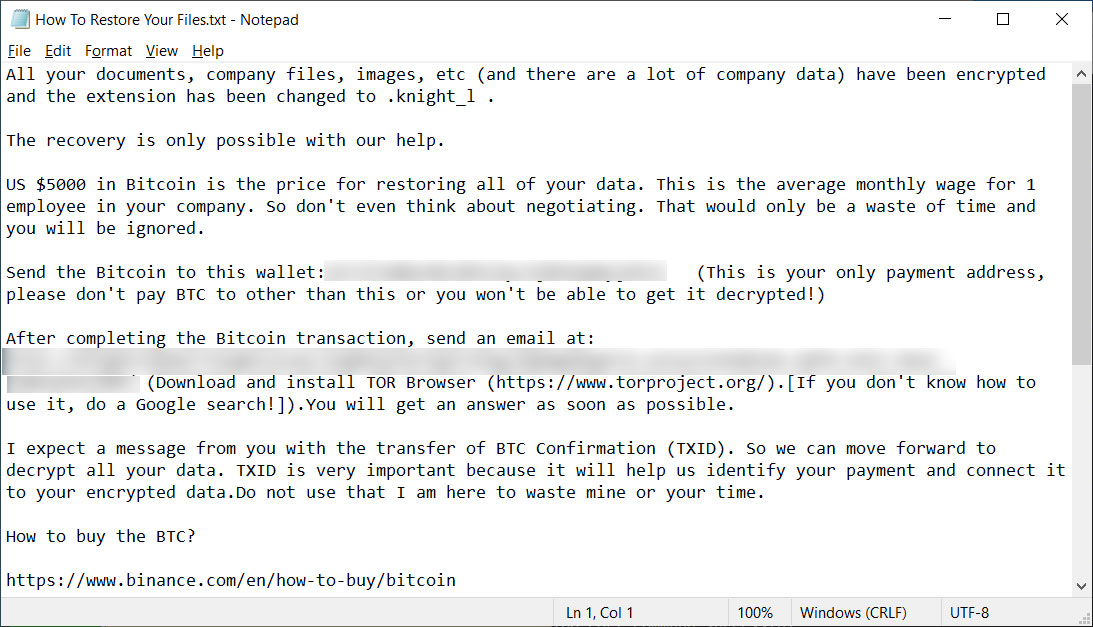
When encrypting files, it will append the .knight_l extension to encrypted files’ names, where the ‘l’ portion likely stands for ‘lite.’
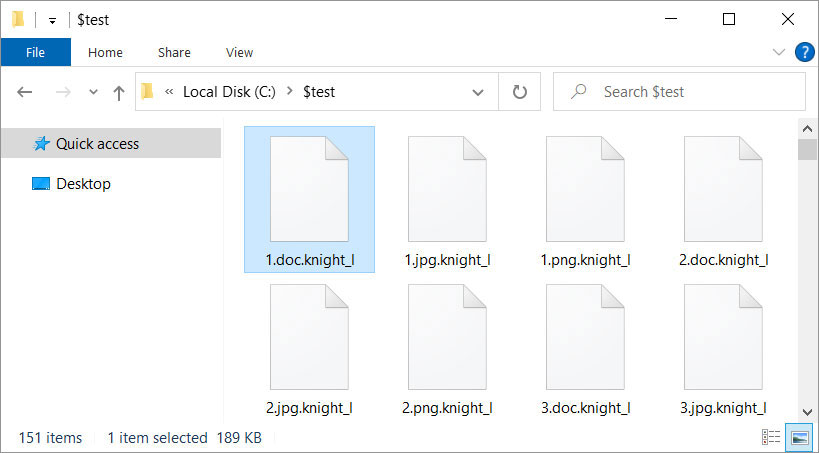
Source: BleepingComputer
The ransomware will also create a ransom note named How To Restore Your Files.txt in each folder on the computer. The ransom note in this campaign demands $5,000 be sent to a listed Bitcoin address and also contains a link to the Knight Tor site.
However, every ransom note in this campaign seen by BleepingComputer utilizes the same Bitcoin address of ’14JJfrWQbud8c8KECHyc9jM6dammyjUb3Z,’ which would make it impossible for the threat actor to determine which victim paid a ransom.
Source: BleepingComputer
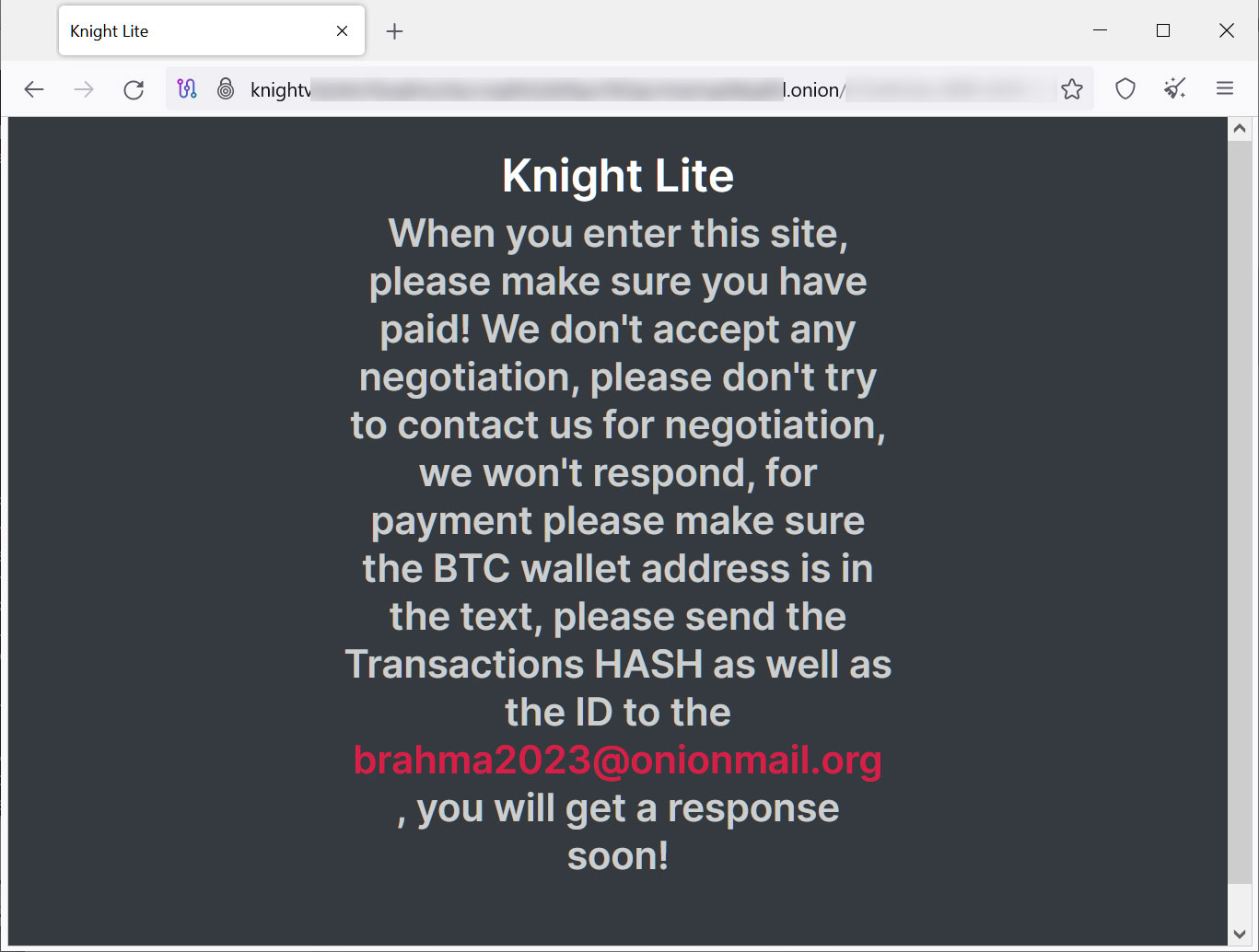
As this is a Knight Lite campaign, visiting the site does not display a negotiation panel. Instead, it shows a message stating that victims should have paid the ransom demand already and to contact the affiliate at brahma2023@onionmail.org then.
Source: BleepingComputer
At this time, it is not known if paying a ransom will result in receiving a decryptor from the Knight affiliate.
Furthermore, all the ransom notes seen by BleepingComputer utilize the same Bitcoin address, making it possible for someone else to claim a payment as theirs, essentially stealing your payment.
Therefore, it is strongly advised to refrain from paying a ransom in this campaign, as there is a good chance you will not receive a decryptor.







