Hackers use a novel method involving RBAC (Role-Based Access Control) to create persistent backdoor accounts on Kubernetes clusters and hijack their resources for Monero crypto-mining.
RBAC is a Kubernetes API access control system allowing admins to define which users or service accounts can access API resources and operations.
By abusing RBAC to enforce malicious access control policies, threat actors can persist on compromised clusters even if the misconfiguration that provided initial access is fixed in the future.
This new type of attack was discovered by Aqua Security’s research team, “Nautilus,” who named the campaign ‘RBAC Buster.’
The analysts report that the attack campaign was observed to be actively used to compromise 60 misconfigured Kubernetes clusters.
RBAC Buster
Aqua Security could record and analyze the attack after the threat actors breached one of its Kubernetes honeypots that were purposely misconfigured to expose APIs and access keys.
The initial access to the target Kubernetes cluster is achieved through unauthenticated requests from anonymous users with privileges, so the API server needs to be misconfigured.
Next, the attacker sends HTTP requests to list secrets and makes API requests to gather information about the cluster by listing entities in the ‘kube-system’ namespace.
At this stage, the attacker checks if the server was compromised already by their campaign, deployed as ‘kube-controller,’ or if other cybercrime competitors have already compromised the cluster. If it finds other attackers’ deployments, it will delete them to take control of the device’s resources for its own malicious use.
The next step is when the attacker gains persistence on the cluster by creating a new ‘ClusterRole’ with near admin-level privileges and a ServiceAccount ‘kube-controller’ in the ‘kube-system’ namespace.
Finally, the attacker creates a ClusterRoleBinding named ‘system:controller:kube-controller,’ binding the ClusterRole with the ServiceAccount to persist in the cluster even in the case that ‘anonymous user access’ is disabled.
A ClusterRoleBinding named ‘kube-controller’ was used to evade detection and blend into logs, as this name is similar to a legitimate daemon used by Kubernetes.
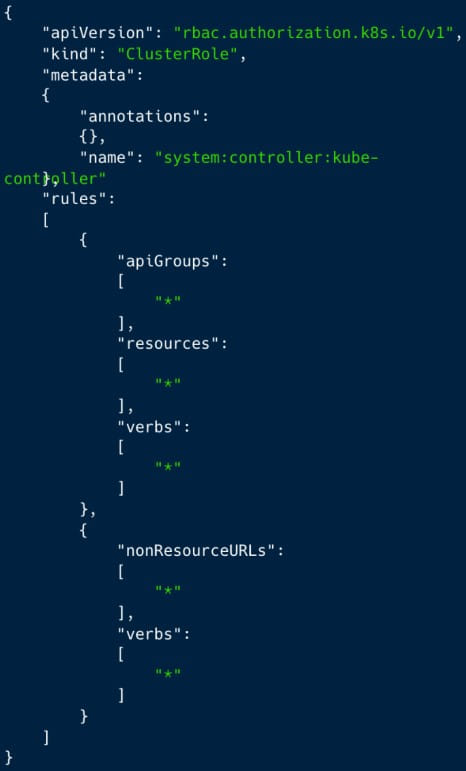
(AquaSec)
AquaSec’s honeypot purposely exposed AWS access keys, and the security firm noticed that the attackers leveraged them to try and gather additional information from the cloud instance they could access.
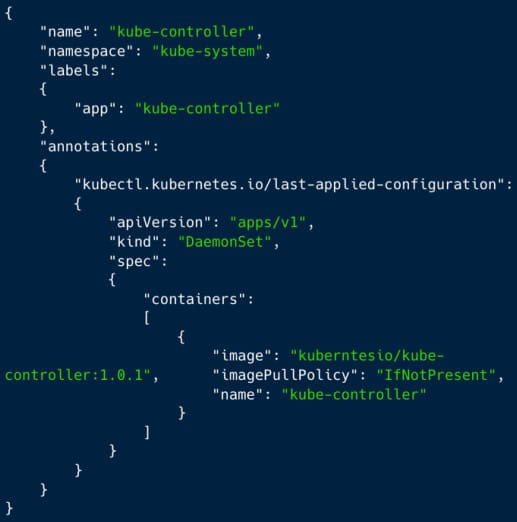
The final step of the attack is to create a DaemonSet to deploy a Docker Hub-hosted container image (‘kuberntesio/kube-controller’) on all nodes with a single API request and start mining the hard-to-trace cryptocurrency Monero on the compromised server.
Deployed through typosquatting
Aqua Security found that the malicious ‘kube-controller’ container was deployed from and located on the public Docker registry as ‘kuberntesio/kube-controller:1.0.1.’ This name impersonates the legitimate ‘kubernetesio’ account and the popular ‘kube-controller-manager’ image.
The latter is a continuously-running critical component of the Kubernetes control plane responsible for detecting and responding to node failures, so it is easy for administrators to overlook.
AquaSec reports that the particular container image has been pulled over 14,000 times from Docker Hub during the five months since it was first uploaded to the repository, indicating that the campaign is widespread.
Retrieving the wallet address from the configuration file revealed that the attacker had already mined 5 XMR and has the potential to make the equivalent of $200 per worker per year.
The repercussions of the RBAC Buster attacks on Kubernetes clusters can be significant and include unauthorized access to data, exposure of secrets, resource hijacking, and potentially even reputation damage.
To mitigate the threat, secure the API server by disallowing unauthenticated requests from anonymous users and create and enforce strict API access policies by using RBAC effectively.
Admins are also urged to monitor audit logs and encrypt any secrets and account credentials hosted in the cluster.







