Microsoft says a North Korean hacking group has breached Taiwanese multimedia software company CyberLink and trojanized one of its installers to push malware in a supply chain attack targeting potential victims worldwide.
According to Microsoft Threat Intelligence, activity suspected to be linked with the altered CyberLink installer file surfaced as early as October 20, 2023.
This trojanized installer has been detected on more than 100 devices across various nations worldwide, including Japan, Taiwan, Canada, and the United States.
Microsoft security experts have attributed this supply chain attack with high confidence to a North Korean cyberespionage group tracked by Redmond as Diamond Sleet (aka ZINC, Labyrinth Chollima, and Lazarus).
The second-stage payload observed while investigating this attack interacts with infrastructure that the same group of threat actors previously compromised.
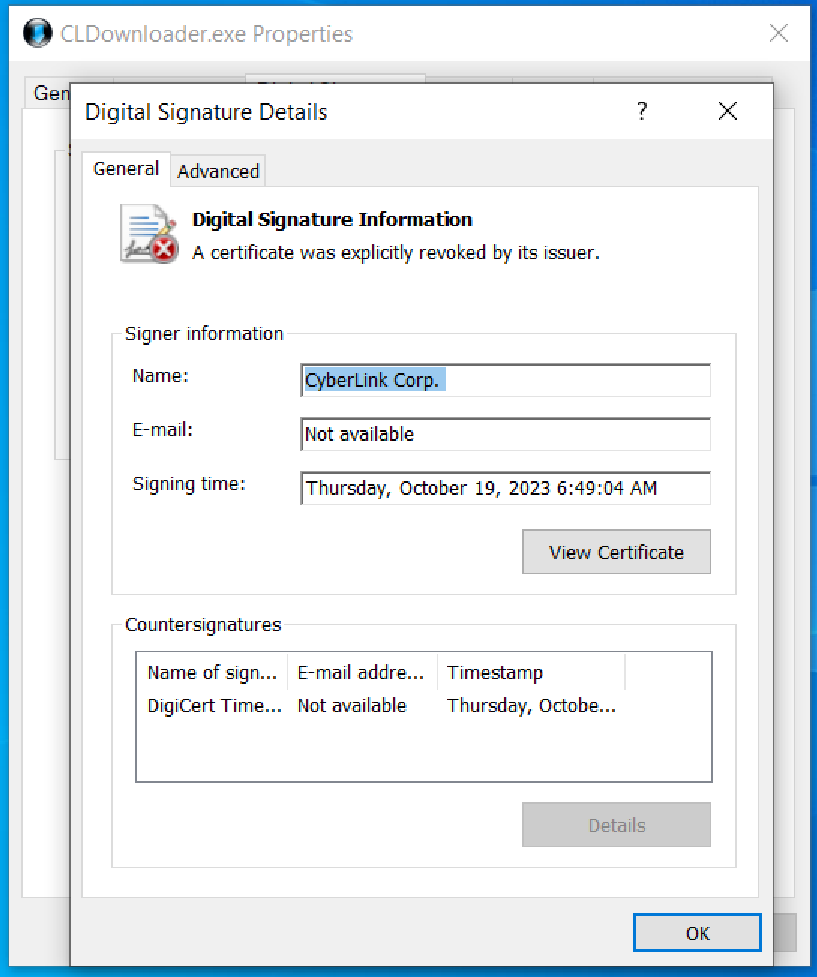
“Diamond Sleet utilized a legitimate code signing certificate issued to CyberLink Corp. to sign the malicious executable,” the company said.
“This certificate has been added to Microsoft’s disallowed certificate list to protect customers from future malicious use of the certificate.”
Microsoft tracks the trojanized software and related payloads as LambLoad, a malware downloader and loader.
LambLoad targets systems not protected by FireEye, CrowdStrike, or Tanium security software. If these conditions are unmet, the malicious executable continues running without executing the bundled malicious code.
However, if the criteria are met, the malware connects with one of three command-and-control (C2) servers to retrieve a second-stage payload concealed within a file posing as a PNG file using the static User-Agent ‘Microsoft Internet Explorer.’
“The PNG file contains an embedded payload inside a fake outer PNG header that is, carved, decrypted, and launched in memory,” Microsoft says.
This is a common attack method used by the Lazarus North Korean threat actors, who are known for trojanizing legitimate cryptocurrency software to steal crypto assets.
Even though Microsoft has yet to detect hands-on-keyboard activity following LambLoad malware breaches, the Lazarus hackers are known for:
- Stealing sensitive data from compromised systems
- Infiltrating software build environments
- Progressing downstream to exploit further victims
- Establishing persistent access to victims’ environments
After detecting a supply chain attack, Microsoft informed CyberLink and is also notifying Microsoft Defender for Endpoint customers who were affected by the attack.
Microsoft also reported the attack to GitHub, which removed the second-stage payload as per its Acceptable Use Policies.
A CyberLink spokesperson did not immediately respond to BleepingComputer’s request for comment.
Who is Lazarus?
The Lazarus Group is a North Korean-sponsored hacking group that has been operating for more than ten years, since at least 2009.
Known for targeting organizations worldwide, their operations have so far included attacks on financial institutions, media outlets, and government agencies.
Lazarus has been linked to a wide range of malicious activities encompassing espionage, data breaches, and financial exploitation. Their campaigns also involved targeting security researchers, embedding malicious code in open-source cryptocurrency platforms, executing massive cryptocurrency heists, and using sham job interviews to disseminate malware.
The group is thought to be behind many high-profile cyber attacks, including the 2014 Sony Pictures hack, the WannaCry ransomware attack of 2017, and the largest crypto hack ever in 2022.







