Malware-as-a-Service on the rise, ransomware rotates away from Bitcoin: a look at crimeware and financial threats in 2023As the financial threat landscape has been evolving dramatically over the past few years, Kaspersky experts believe it is no longer sufficient to look at the threats to traditional financial institutions, but that it is better to assess financial threats as a whole.
The cybercrime market has been developing extensively, with the overwhelming majority of attackers pursuing one goal – financial profit. This year, our researchers have decided to adjust their predictions accordingly, expanding them to encompass both crimeware developments and financial cyberthreats.
By analyzing the significant events and trends that formed both crimeware and the financial threats landscape in 2022, our security experts and researchers have forecasted several important tendencies expected in 2023. Here are their key prediction.
2023 EXPRESS FORECAST
Led by gamers and entertainment sectors, web3 continues to gain traction
With the increasing popularity of cryptocurrencies, the number of crypto scams has also grown. However, users are now much more aware of crypto and will not fall for primitive scams such as the dubious cryptocurrency scheme that went viral featuring a video with a deepfake “Elon Musk”.
Cybercriminals will continue to try stealing from people using fake ICOs and NFTs, and other cryptocurrency-based financial theft. Along with the exploitation of vulnerable smart contracts, criminals will use and create more advanced methods to proliferate their crimes. •
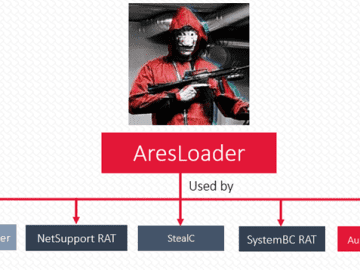
Malware loaders are to become the hottest goods on the underground market
Many actors have their own malware, but that alone is not enough. Entire samples used to consist of ransomware alone. But when there are different types of modules in ransomware, it is easier for the threat to evade detection. As a result, attackers are now paying much more attention to downloaders and droppers, which can avoid detection.
This has become a major commodity in the Malware-as-a-Service industry, and there are already favorites among cybercriminals on the darknet, for example the Matanbunchus downloader. All in all, stealth execution and bypassing EDR’s is what malicious loaders developers are going to focus on in 2023.
More new penetration testing frameworks will be deployed by cybercriminals
While various vendors create and improve penetration testing frameworks to protect companies, such as Brute Ratel C4 and Cobalt Strike, crimeware actors are expected to use them much more actively for illegal activities. Along with the development of new penetration tools, cybercriminals will increasingly use the frameworks for their own malicious purposes.
Ransomware negotiations and payments will rely less on Bitcoin as a transfer of value
As sanctions on ransomware payments continue to be issued, the markets become more regulated, and technologies improve at tracking the flow and sources of Bitcoin (and sometimes clawing back conspicuous transactions), cybercrooks will rotate away from this cryptocurrency and toward other forms of value transfer.
Ransomware groups following less financial interest, but more destructive activity
As the geopolitical agenda increasingly occupies the attention not only of the public but also of cybercriminals, ransomware groups are expected to make demands for some form of political action instead of asking for ransom money. An example of this is Freeud, brand-new ransomware with wiper capabilities.