Admins, hosting providers, and the French Computer Emergency Response Team (CERT-FR) warn that attackers actively target VMware ESXi servers unpatched against a two-year-old remote code execution vulnerability to deploy ransomware.
Tracked as CVE-2021-21974, the security flaw is caused by a heap overflow issue in the OpenSLP service that can be exploited by unauthenticated threat actors in low-complexity attacks.
“As current investigations, these attack campaigns appear to be exploiting the vulnerability CVE-2021-21974, for which a patch has been available since 23 February 2021,” CERT-FR said.
“The systems currently targeted would be ESXi hypervisors in version 6.x and prior to 6.7.”
To block incoming attacks, admins have to disable the vulnerable Service Location Protocol (SLP) service on ESXi hypervisors that haven’t yet been updated.
CERT-FR strongly recommends applying the patch as soon as possible but adds that systems left unpatched should also be scanned to look for signs of compromise.
CVE-2021-21974 affects the following systems:
- ESXi versions 7.x prior to ESXi70U1c-17325551
- ESXi versions 6.7.x prior to ESXi670-202102401-SG
- ESXi versions 6.5.x prior to ESXi650-202102101-SG
French cloud provider OVHcloud has also published a report today linking this massive wave of attacks targeting VMware ESXi servers with the Nevada ransomware operation.
“According to experts from the ecosystem as well as autorities, they might be related to Nevada ransomware and are using CVE-2021-21974 as compromission vector. Investigation are still ongoing to confirm those assumptions,” OVHcloud CISO Julien Levrard said.
“The attack is primarily targetting ESXi servers in version before 7.0 U3i, apparently through the OpenSLP port (427).”
New ESXiArgs ransomware
However, from the ransom notes seen in this attack, they do not appear to be related to the Nevada Ransomware, and appears to be a new ransomware family.
Starting roughly four hours ago, victims impacted by this campaign have also begun reporting the attacks on BleepingComputer’s forum, asking for help and more information on how to recover their data.
The ransomware encrypts files with the .vmxf, .vmx, .vmsd, and .nvram extensions on compromised ESXi servers and creates a .args file for each encrypted document with metadata (likely needed for decryption).
Victims have found ransom notes named “ransom.html” and “How to Restore Your Files.html” on locked systems. Others said that their notes are plaintext files.
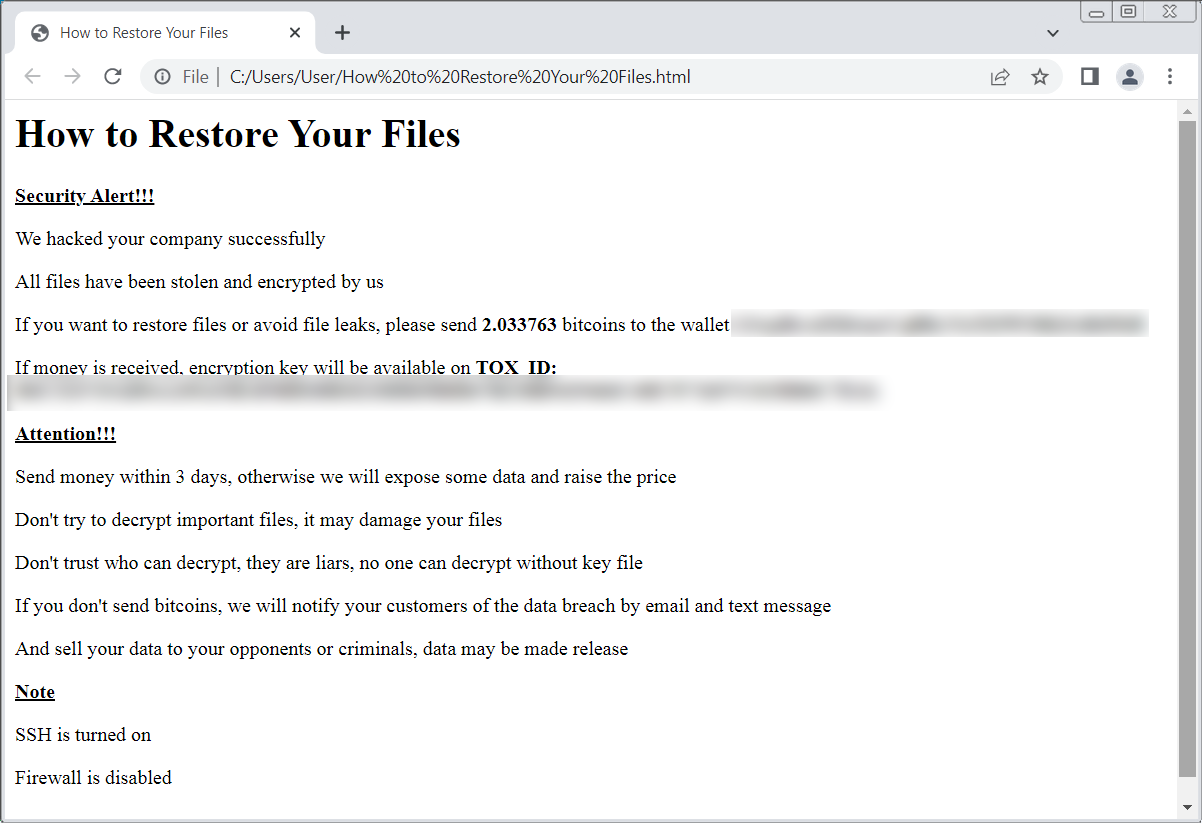
ID Ransomware’s Michael Gillespie is currently tracking the ransomware under the name ‘ESXiArgs,’ but told BleepingComputer that until we can find a sample, there is no way to determine if it has any weaknesses in the encryption.
BleepingComputer has a dedicated support topic where people are reporting their experiences with this attack.
If you have new information or a copy of the malware, please let us know so researchers can analyze it for weaknesses.
This is a developing story and will be updated with new info as it becomes available …







