A ransomware operation known as Medusa has begun to pick up steam in 2023, targeting corporate victims worldwide with million-dollar ransom demands.
The Medusa operation started in June 2021 but had relatively low activity, with few victims. However, in 2023 the ransomware gang increased in activity and launched a ‘Medusa Blog’ used to leak data for victims who refused to pay a ransom.
Medusa gained media attention this week after they claimed responsibility for an attack on the Minneapolis Public Schools (MPS) district and shared a video of the stolen data.
Will the real Medusa please stand up?
Many malware families call themselves Medusa, including a Mirai-based botnet with ransomware capabilities, a Medusa Android malware, and the widely known MedusaLocker ransomware operation.
Due to the commonly used name, there has been some confusing reporting about this ransomware family, with many thinking it’s the same as MedusaLocker.
However, the Medusa and MedusaLocker ransomware operations are entirely different.
The MedusaLocker operation launched in 2019 as a Ransomware-as-a-Service, with numerous affiliates, a ransom note commonly named How_to_back_files.html, and a wide variety of file extensions for encrypted files.
The MedusaLocker operation uses a Tor website at qd7pcafncosqfqu3ha6fcx4h6sr7tzwagzpcdcnytiw3b6varaeqv5yd.onion for negotiation.
However, the Medusa ransomware operation launched around June 2021 and has been using a ransom note named !!!READ_ME_MEDUSA!!!.txt and a static encrypted file extension of .MEDUSA.
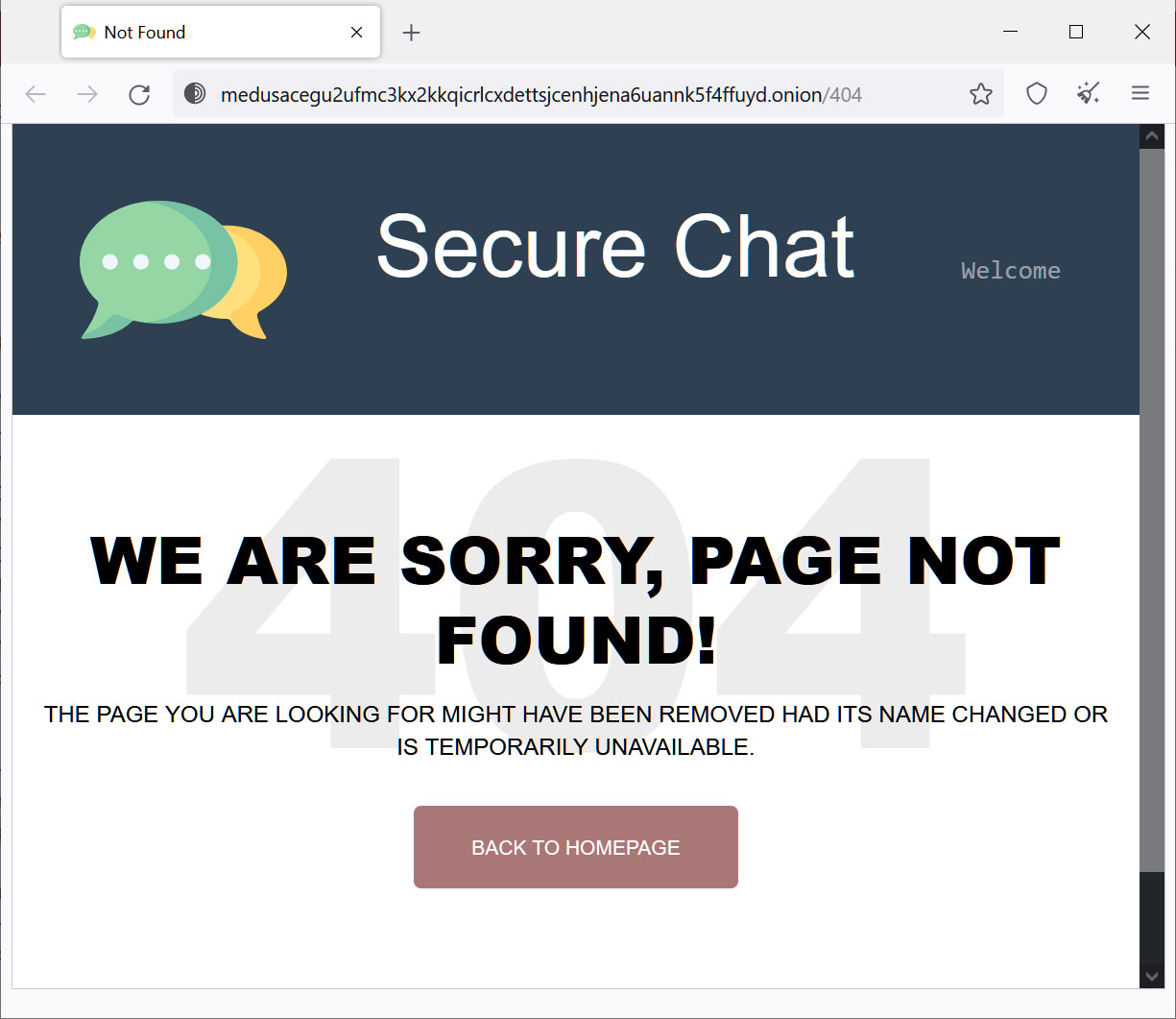
The Medusa operation also uses a Tor website for ransom negotiations, yet their’s is located at medusacegu2ufmc3kx2kkqicrlcxdettsjcenhjena6uannk5f4ffuyd.onion.
How Medusa encrypts Windows devices
BleepingComputer has only been able to analyze the Medusa encryptor for Windows, and it is not known if they have one for Linux at this time.
The Windows encryptor will accept command-line options that allow the threat actor to configure how files will be encrypted on the device, as shown below.
# Command Line
Option | Description
---------------------
-V | Get version
-d | Do not delete self
-f | Exclude system folder
-i | In path
-k | Key file path
-n | Use network
-p | Do not preprocess (preprocess = kill services and shadow copies)
-s | Exclude system drive
-t | Note file path
-v | Show console window
-w | Initial run powershell path (powershell -executionpolicy bypass -File %s)
For example, the -v command line argument will cause the ransomware to display a console, showing status messages as it encrypts a device.
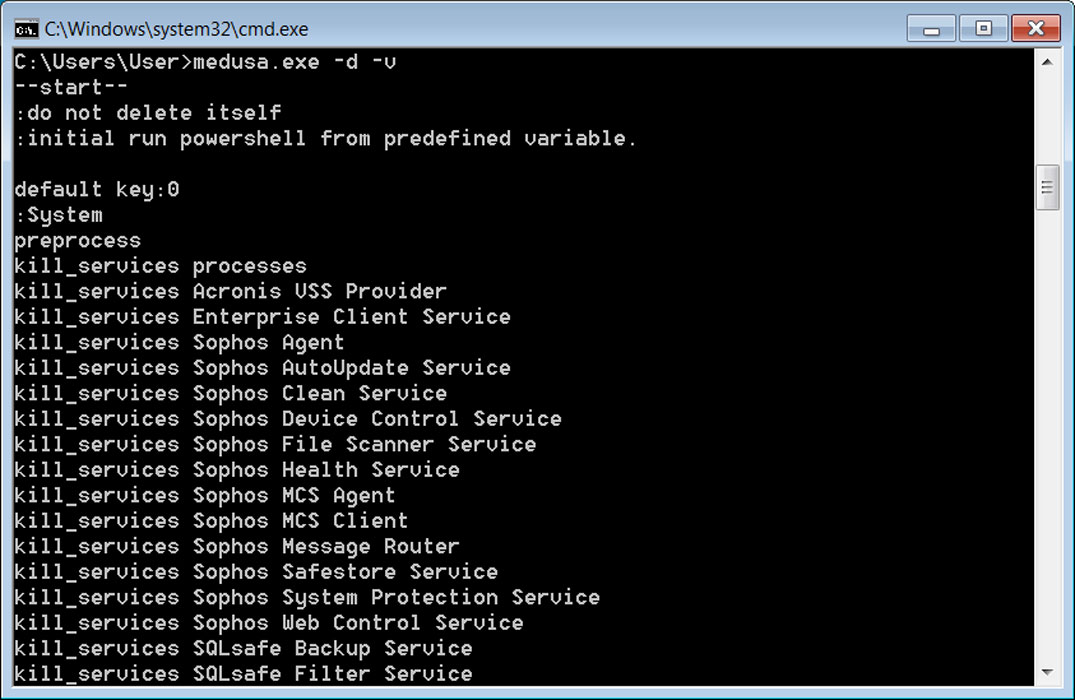
Source: BleepingComputer
In a regular run, without command line arguments, the Medusa ransomware will terminate over 280 Windows services and processes for programs that may prevent files from being encrypted. These include Windows services for mail servers, database servers, backup servers, and security software.
The ransomware will then delete Windows Shadow Volume Copies to prevent them from being used to recover files.
deletes shadow volume copies
vssadmin Delete Shadows /all /quiet
vssadmin resize shadowstorage /for=%s /on=%s /maxsize=unbounded
Ransomware expert Michael Gillespie also analyzed the encryptor and told BleepingComputer it encrypts files using AES-256 + RSA-2048 encryption using the BCrypt library.
Gillespie further confirmed that the encryption method used in Medusa is different than the one used in MedusaLocker.
When encrypting files, the ransomware will append the .MEDUSA extension to encrypted file names, as shown below. For example, 1.doc would be encrypted and renamed to 1.doc.MEDUSA.
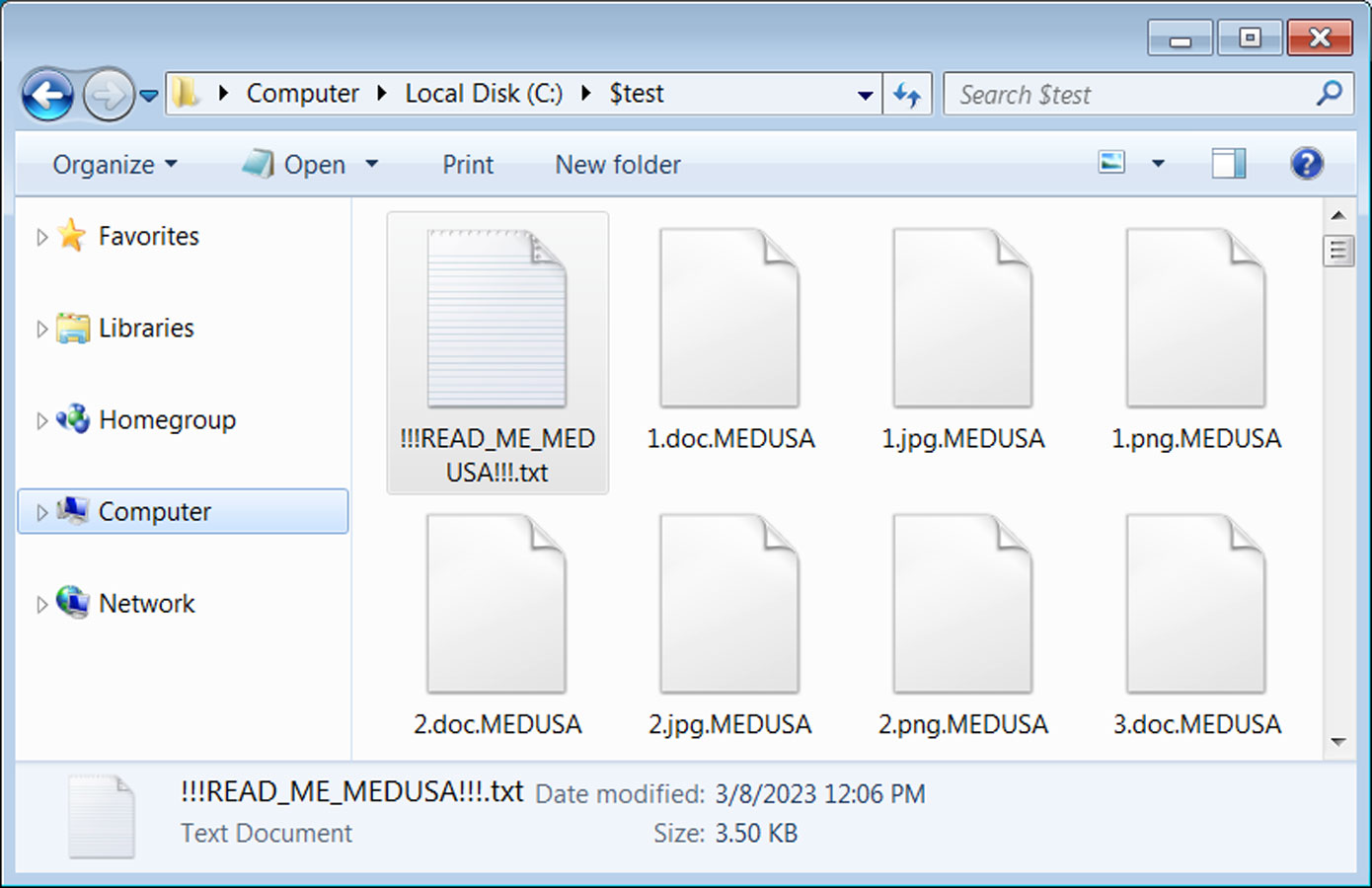
Source: BleepingComputer
In each folder, the ransomware will create a ransom note named !!!READ_ME_MEDUSA!!!.txt that contains information about what happened to the victim’s files.
The ransom note will also include extension contact information, including a Tor data leak site, a Tor negotiation site, a Telegram channel, a Tox ID, and the key.medusa.serviceteam@protonmail.com email address.
The Tor negotiation site is at http://medusacegu2ufmc3kx2kkqicrlcxdettsjcenhjena6uannk5f4ffuyd.onion.
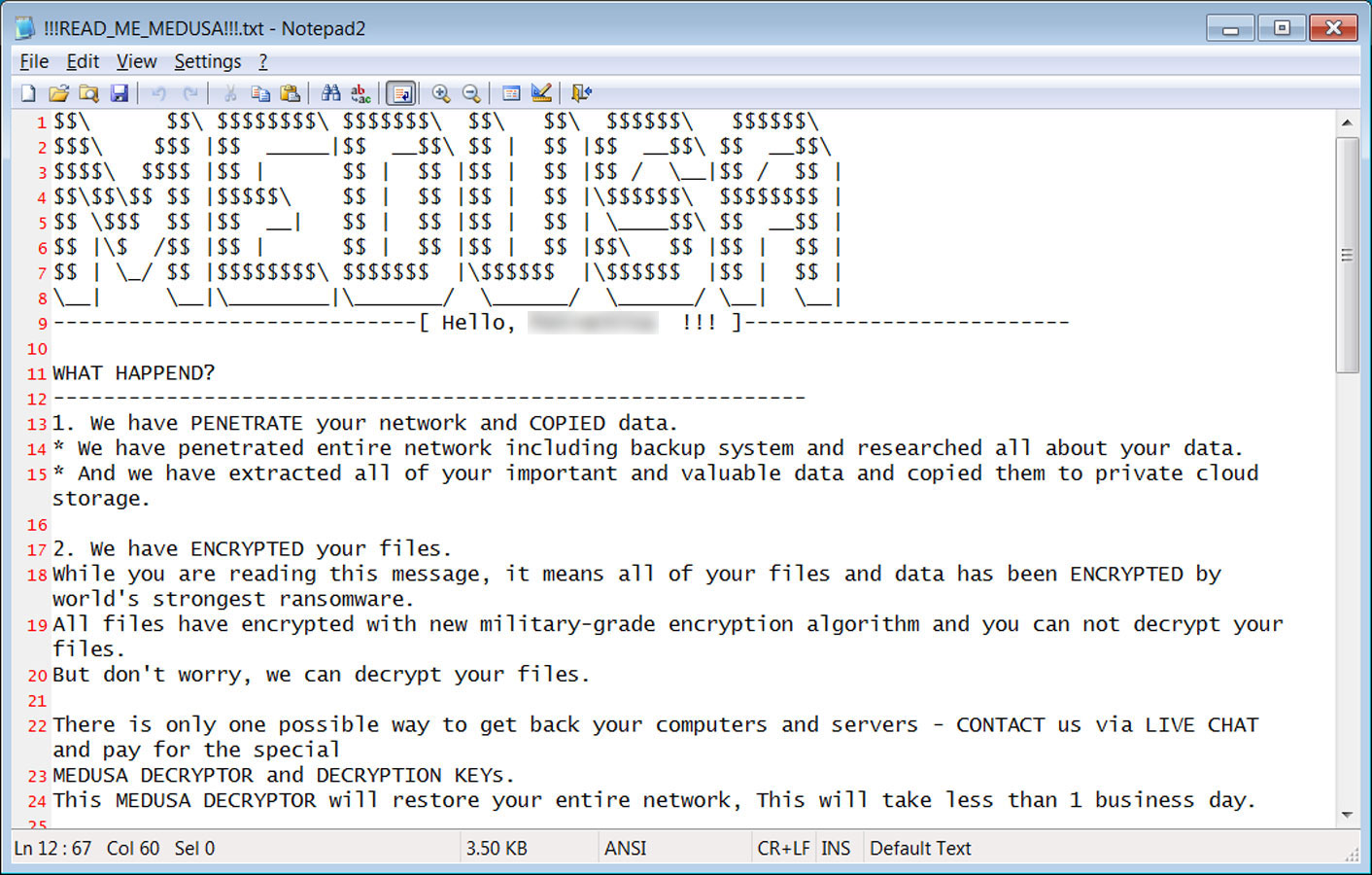
Source: BleepingComputer
As an extra step to prevent the restoration of files from backups, the Medusa ransomware will run the following command to delete locally stored files associated with backup programs, like Windows Backup. This command will also delete virtual disk hard drives (VHD) used by virtual machines.
del /s /f /q %s*.VHD %s*.bac %s*.bak %s*.wbcat %s*.bkf %sBackup*.* %sbackup*.* %s*.set %s*.win %s*.dsk
The Tor negotiation site calls itself “Secure Chat,” where each victim has a unique ID that can be used to communicate with the ransomware gang.
Source: BleepingComputer
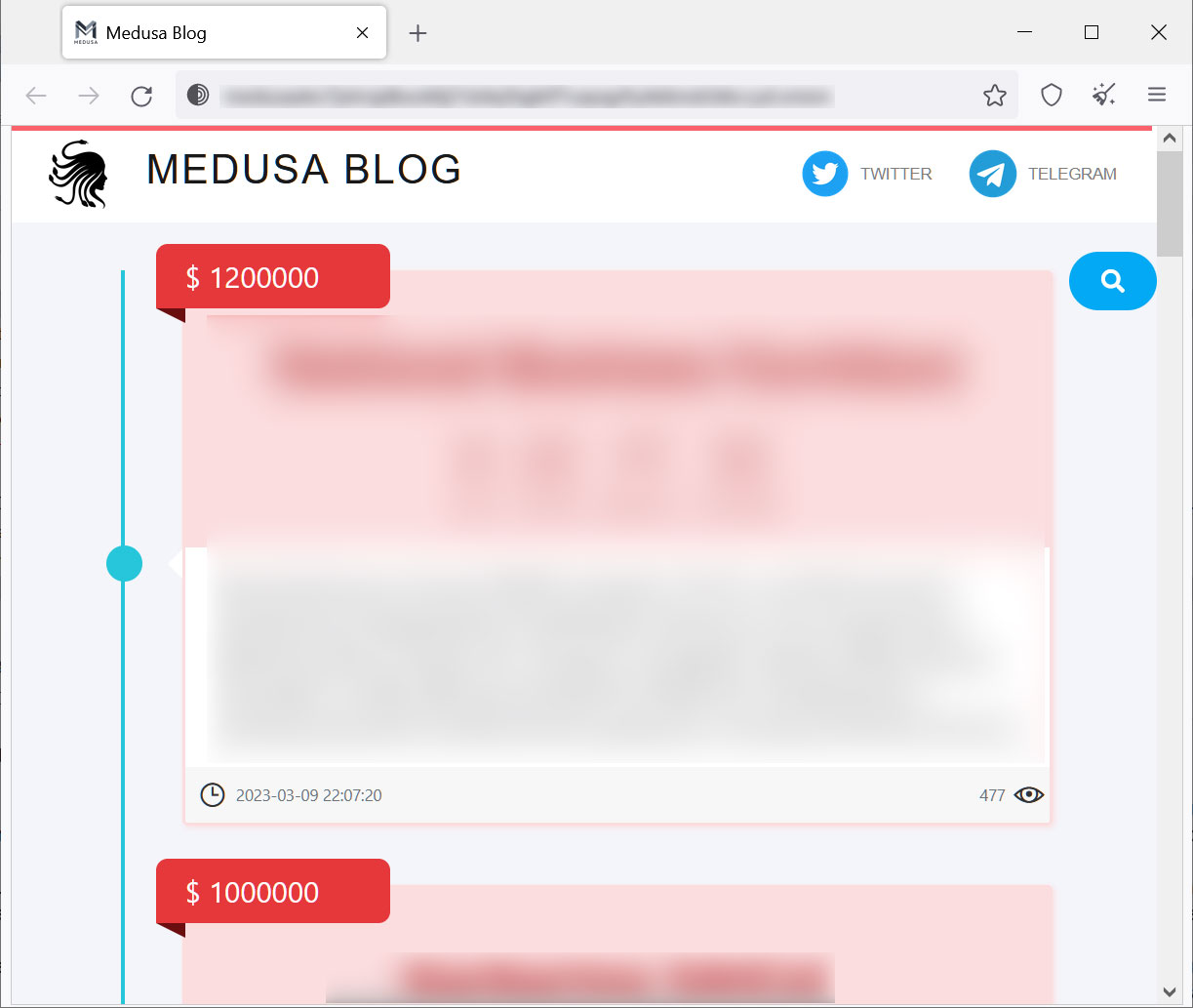
Like most enterprise-targeting ransomware operations, Medusa has a data leak site named ‘Medusa Blog.’ This site is used as part of the gang’s double-extortion strategy, where they leak data for victims who refuse to pay a ransom.
Source: BleepingComputer
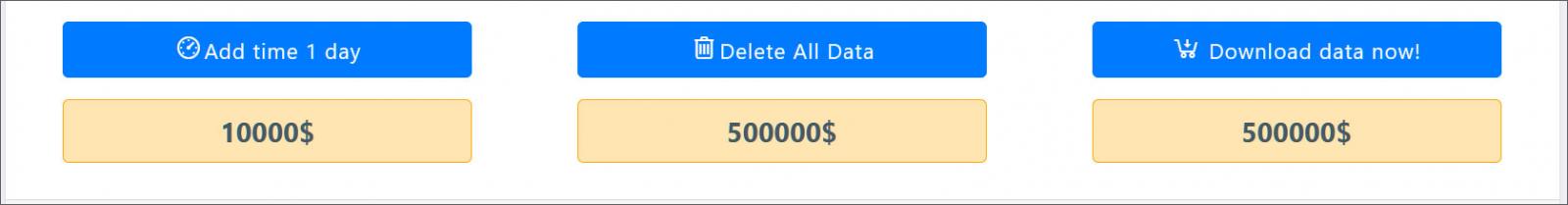
When a victim is added to the data leak, their data is not immediately published. Instead, the threat actors give the victims paid options to extend the countdown before data is released, to delete the data, or to download all of the data. Each of these options has different prices, as shown below.
Source: BleepingComputer
These three options are done to apply extra pressure on the victim to scare them into paying a ransom.
Unfortunately, no known weaknesses in the Medusa Ransomware encryption allow victims to recover their files for free.
Researchers will continue to analyze the encryptor, and if a weakness is found, we will report it at BleepingComputer.