The new Brain Cipher ransomware operation has begun targeting organizations worldwide, gaining media attention for a recent attack on Indonesia’s temporary National Data Center.
Indonesia is building out National Data Centers to securely store servers used by the government for online services and data hosting.
On June 20th, one of the temporary National Data Centers suffered a cyberattack that encrypted the government’s servers and disrupted immigration services, passport control, issuing of event permits, and other online services.
The government confirmed that a new ransomware operation, Brain Cipher, was behind the attack, disrupting over 200 government agencies.
Brain Cipher demanded $8 million in the Monero cryptocurrency to receive a decryptor and not leak allegedly stolen data.
BleepingComputer has learned that the threat actors have stated in the negotiation chat that they are issuing a “press release” about the “quality of personal data protection” in the attack, likely indicating that data was stolen.
Who is Brain Cipher
Brain Cipher is a new ransomware operation launched earlier this month, conducting attacks on organizations worldwide.
While the ransomware gang initially launched without a data leak site, their latest ransom notes now link to one, indicating that data is still in attack and will be used in double-extortion schemes.
BleepingComputer is aware of numerous samples of the Brain Cipher ransomware uploaded to various malware-sharing sites over the past two weeks.
These samples [1, 2, 3] were created using the leaked LockBit 3.0 builder, which other threat actors heavily abused to launch their own ransomware operations.
However, Brain Cipher has made some minor changes to the encryptor.
One of those changes is that it not only appends an extension to the encrypted file but also encrypts the file name, as shown below.
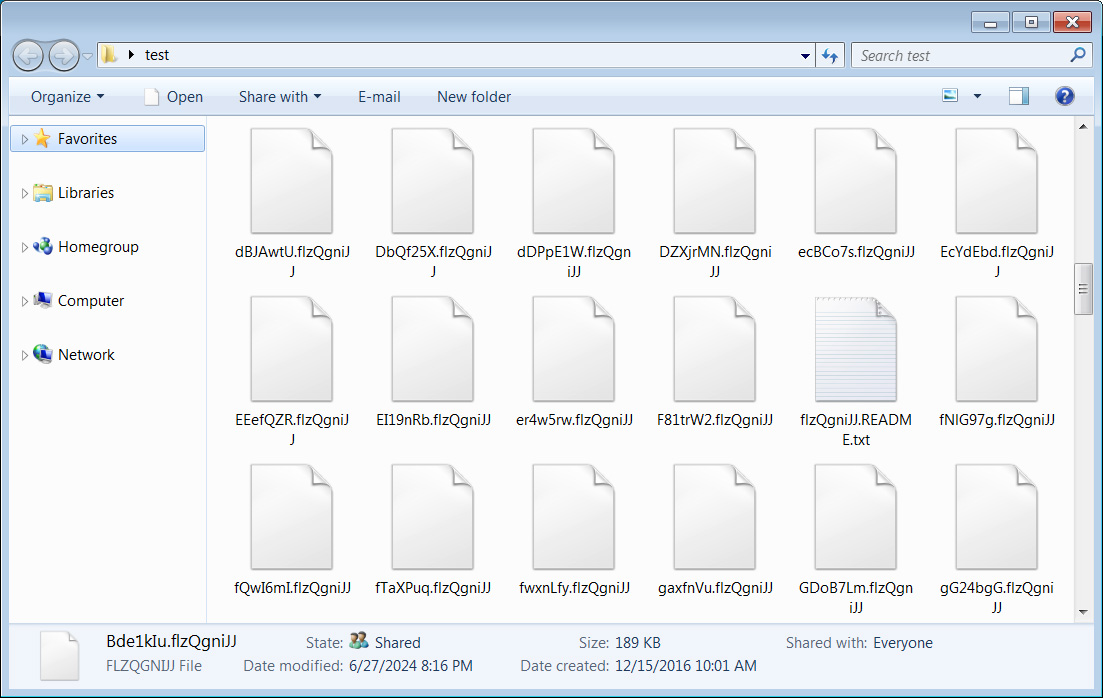
Source: BleepingComputer
The encryptor will also create ransom notes named in the format of [extension].README.txt, as shown below. These ransom notes briefly describe what happened, make threats, and link to the Tor negotiation and data leak sites.
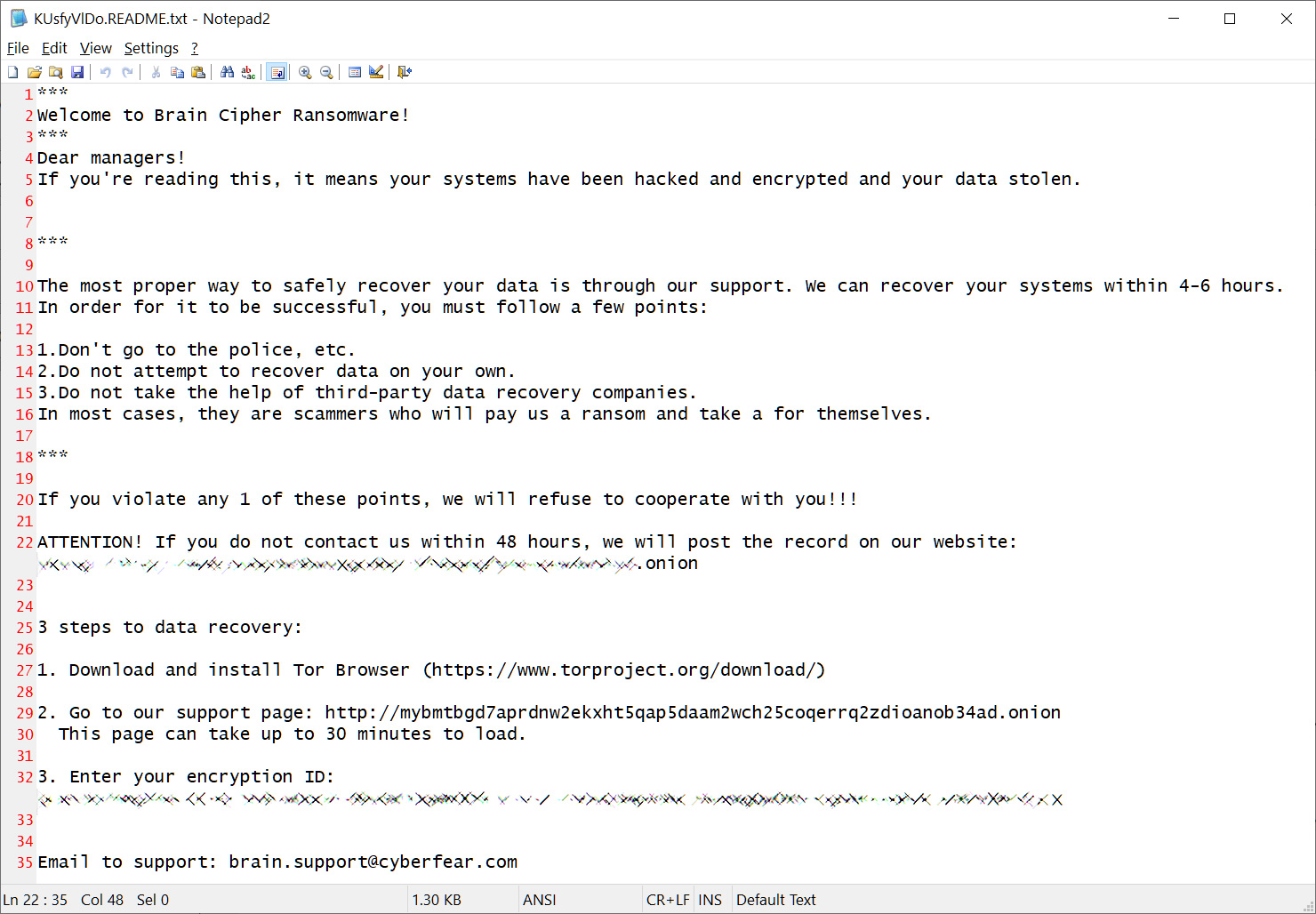
Source: BleepingComputer
In one note seen by BleepingComputer, the threat actor deviated a bit in the template and used the file name ‘How To Restore Your Files.txt.’
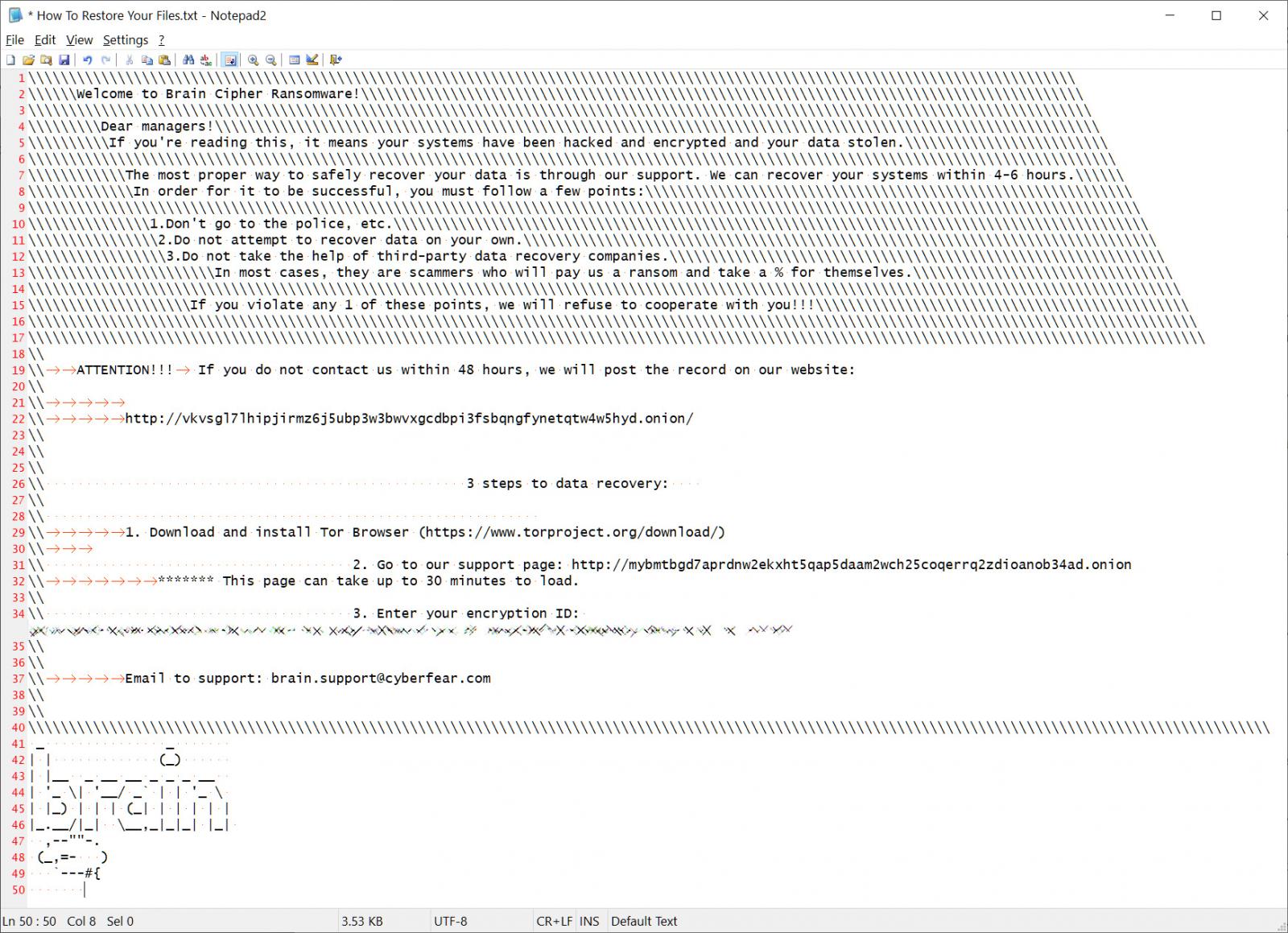
Source: BleepingComputer
Each victim has a unique encryption ID that is entered into the threat actor’s Tor negotiation site. Like many other recent ransomware operations, the negotiation site is pretty simple, just including a chat system that the victim can use to communicate with the ransomware gang.
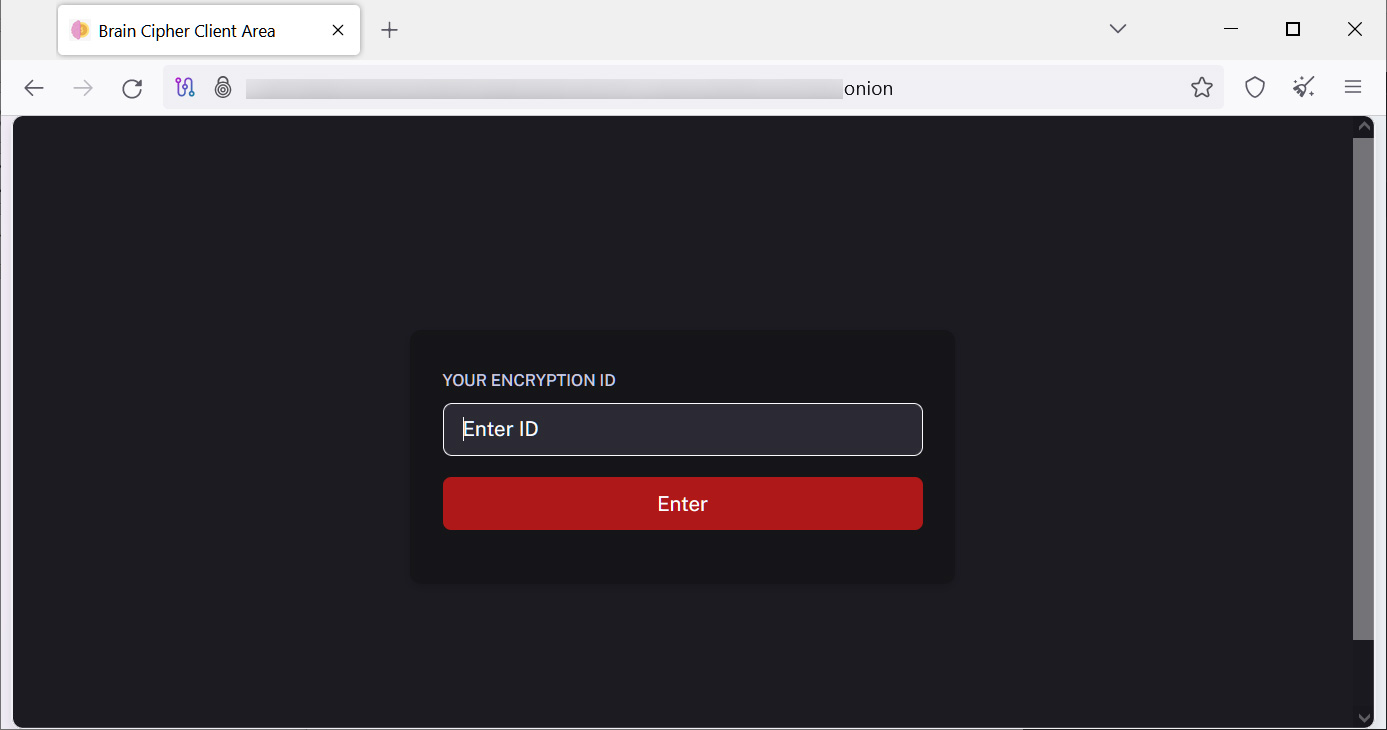
Source: BleepingComputer
New data leak site launched
Like other ransomware operations, Brain Cipher will breach a corporate network and spread laterally to other devices. Once the threat actors gain Windows domain admin credentials, they deploy the ransomware throughout the network.
However, before encrypting files, the threat actors will steal corporate data for leverage in their extortion attempts, warning victims that it will be publicly released if a ransom is not paid.
Brain Cipher is no different and has recently launched a new data leak site that does not currently list any victims.
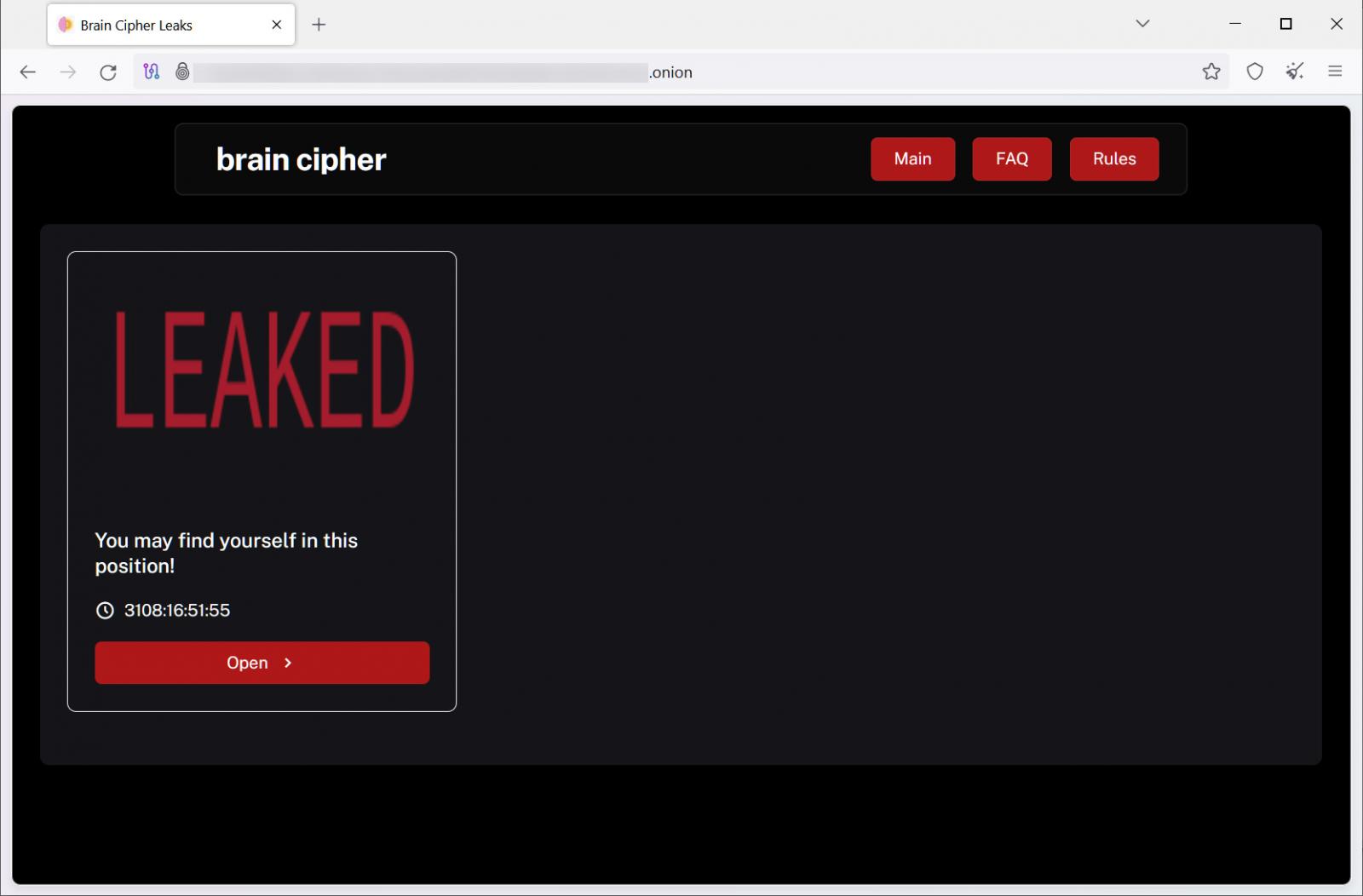
Source: BleepingComputer
From negotiations seen by BleepingComputer, the ransomware gang has demanded ransoms ranging between $20,000 and $8 million.
As the encryptor is based on the leaked LockBit 3 encryptor, it has been thoroughly analyzed in the past, and unless Brain Cipher tweaked the encryption algorithm, there are no known ways to recover files for free.






