Ransomware is seen as the biggest cybersecurity threat across every industry, with 75% of organizations affected by ransomware more than once in the past 12 months – a jump from 61% in 2023, according to SpyCloud.
Session hijacking surges as major ransomware threat
Traditional tools and solutions like antivirus and MFA are not infallible. For organizations affected by ransomware in the past year, MFA bypass via session hijacking is seen as the greatest emerging threat for ransomware, and at least 54% of devices infected with infostealer malware had an antivirus or endpoint detection and response (EDR) solution installed at the time of infection.
Despite this, respondents still named MFA as the second-most common countermeasure for malware remediation – demonstrating a need for new strategies.
Based on recaptured malware data tied to the industries SpyCloud surveyed, as well as previous self-reported ransomware attacks, SpyCloud predicts that the insurance and healthcare industries are at most risk for a ransomware attack in 2024:
- Insurance: 6.3x more likely to experience a ransomware attack
- Healthcare: 2.1x more likely to experience a ransomware attack
CIOs, CISOs, and other IT security executives (91%) are almost twice as confident than their security practitioner counterparts (54%) in their organization’s ability to prevent a full-blown ransomware attack – outlining an alarming disconnect between key decision makers and front-line teams on their preparedness for this costly threat.
“With ransomware operators increasingly exploiting infostealer-exfiltrated data like session cookies, it’s become clear that traditional defenses are no longer enough,” said Damon Fleury, CPO at SpyCloud. “Organizations need to shift to an identity-centric approach for malware remediation and ransomware prevention. This means extending protection beyond just devices and directly addressing exposed digital identities. To disrupt the evolving tactics of ransomware attacks before they escalate, step one is knowing the data criminals have already stolen. Step two is quickly remediating compromised credentials and terminating stolen web sessions – including SSO, VPN, and SaaS application access.”
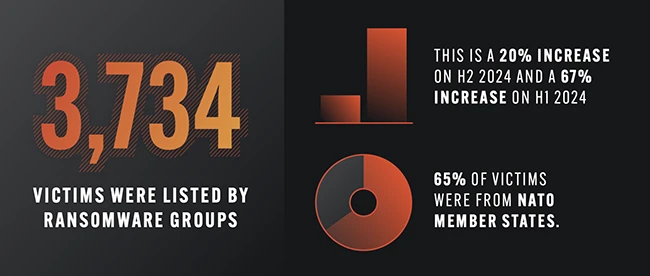
Organizations paying more ransoms
Given ransomware operators’ success, it comes as no surprise to see an increase in the number of surveyed organizations that have been affected by ransomware in the past 12 months. In fact, over 90% of organizations reported being affected by ransomware over the last year, up from 81% in 2023. ‘Affected’ in this context means teams allocated resources to address ransomware attempts and/or full-blown attacks.
Additionally, the data shows that year-over-year, significantly more organizations paid a ransom: 62% this year vs. 48% last year. But only about a third of those organizations fully recovered their data, which is a stark reminder that giving in to cybercriminals’ demands is a gamble, and the odds are not always in your favor.
In addition to the paid ransom, the overall cost of a ransomware attack continues to rise with more than 44% of businesses now incurring over $1 million in total costs, up from 39% last year. These expenses can include general disruptions, lost business, reduced productivity, and reputational damage—any of which can wreak havoc on an organization’s bottom line.
Rise of infostealer malware and digital identity exposure
Cybercriminals have pivoted to next-generation tactics, using information-stealing malware (or “infostealers”) to siphon digital identity data, authentication details, and session cookies from infected users and selling this information to ransomware operators – leaving virtually every respondent (99.8%) concerned about this trend.
61% of all data breaches in the past year were malware-related, with infostealers responsible for the theft of 343.78 million credentials. One in five individuals have been victims of an infostealer infection. Each infection, on average, exposes 10-25 third-party business application credentials, creating fertile ground for further access and exploitation by ransomware operators. This, combined with a similarly explosive growth in digital identity exposure over the past few years, fuels a perfect storm for targeted cyberattacks like ransomware.
Participants rank third-party access as the second most common entry point for ransomware, and 82% are either extremely or significantly concerned about risks posed by third-party devices. Security professionals within the technology and manufacturing sectors express the highest concern.
Security teams often have little-to-no visibility into the risk stemming from these endpoints, making it difficult for an organization to properly defend itself. Compounding the issue, survey participants ranked detecting third-party or unmanaged devices infected by malware as the capability organizations lack the most today.
Security teams ramp up responses to malware infections
While there is universal agreement that more needs to be done to address the infostealer problem, the research demonstrates that organizations are making progress. The top routine actions that security teams now take in response to a malware infection on an infected device are: investigating the incident (79%), resetting passwords for potentially exposed applications (77%), and attempting to remove the malware (67%).
There was a big year-over-year jump in password resets (from 64% in 2023), which may be a positive sign of maturity. However, a “brute force” reset and wipe doesn’t solve the larger issue of stolen data, and thus access, in the wrong hands. Reviewing logs to analyze exposure and determine the necessary remediation path should be a high priority. Yet even fewer security teams do this than before: only 55% this year vs. 73% last year.
“To fully combat ransomware and other critical threats, organizations must adopt a multi-layered strategy that includes post-infection remediation steps like resetting application credentials and invalidating session cookies siphoned by infostealer malware,” Fleury added.