Microsoft has provided a workaround to temporarily fix a known issue that is blocking Linux from booting on dual-boot systems with Secure Boot enabled.
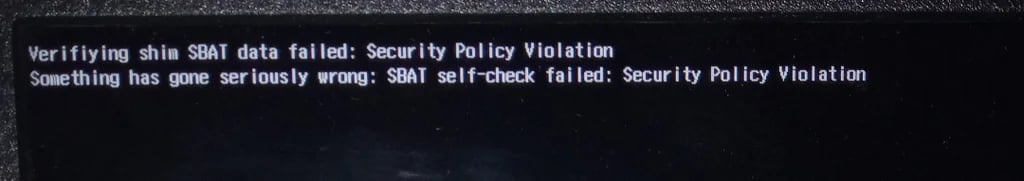
The company says this temporary fix can help Linux users revive unbootable systems displaying “Something has gone seriously wrong: SBAT self-check failed: Security Policy Violation” errors after installing the August 2024 Windows security updates.
Many Linux users confirmed they were affected by this known issue following this month’s Patch Tuesday, as BleepingComputer reported on Tuesday.
Those affected said that their systems (running a wide range of distros, including but not limited to Ubuntu, Linux Mint, Zorin OS, and Puppy Linux) stopped booting into Linux after installing this month’s Windows cumulative updates.
The issue is triggered by a Secure Boot Advanced Targeting (SBAT) update designed to block UEFI shim bootloaders vulnerable to exploits targeting the CVE-2022-2601 GRUB2 Secure Boot bypass. When it released the update, Microsoft said the update would not be delivered to devices where dual booting is detected.
However, after acknowledging the issue this week, it also confirmed that “the dual-boot detection did not detect some customized methods of dual-booting and applied the SBAT value when it should not have been applied.”
For those who have already installed the August 2024 Windows updates and can no longer boot Linux on their dual-boot devices, Microsoft recommends deleting the SBAT update and ensuring that future SBAT updates will no longer be installed.
To do that, you will have to go through the following procedure:
- Disable Secure Boot after booting into your device’s firmware settings (this requires different steps for every manufacturer).
- Delete the SBAT update by booting Linux and running the
sudo mokutil --set-sbat-policy deletecommand and rebooting. - Verify SBAT revocations by running the
mokutil --list-sbat-revocationscommand and ensuring it’s empty. - Re-enable Secure Boot from your device’s firmware settings.
- Check the Secure Boot status by booting into Linux, running the
mokutil --sb-statecommand, and ensuring the output is “SecureBoot enabled.” If not, retry the 4th step. - Prevent Future SBAT Updates in Windows by running the following command from a Command Prompt window as Administrator:
reg add HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlSecureBootSBAT /v OptOut /d 1 /t REG_DWORD
“At this point, you should now be able to boot into Linux or Windows as before. It’s a good time to install any pending Linux updates to ensure your system is secure,” Microsoft said.
The company is still investigating the issue with the help of Linux partners and will provide more updates when new information is available.