The QSC Loader service DLL named “loader.dll” leverages two distinct methods to obtain the path to the Core module code.
It either extracts the path from the system directory “driversmsnet” or reads and deletes a 256-byte path string from the file “n_600s.sys” within its own directory.
Subsequently, the Loader reads and decompresses the code from the specified path. Through reflective loading, it injects this decompressed code into memory and executes the exported function “plugin_working” within the injected Core module.
The Core module dynamically loads and injects the Network module, responsible for C2 communication using MbedTLS and leverages configuration data, including potentially sensitive internal/proxy IP addresses, to establish connections.
Specifically, it communicates with the File Manager module, which is responsible for providing functionalities such as browsing the file system, reading, writing, deleting, and moving files.
Both modules operate within the context of the Core module, which manages their loading, initialization, and execution, including handling C2 commands for data exfiltration and module updates.
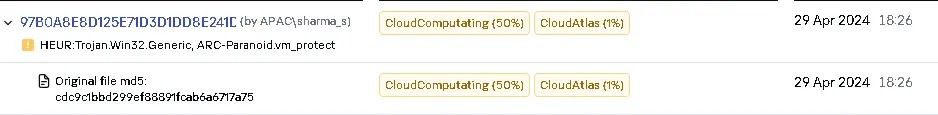
The QSC framework, discovered in 2021, was recently observed deployed by the CloudComputating threat actor targeting an ISP in West Asia that leveraged pre-existing access established through the Turian backdoor since 2022.
Investigate Real-World Malicious Links, Malware & Phishing Attacks With ANY.RUN – Try for Free
It employs a Command Shell module (qscShell.dll) that interacts with a spawned cmd.exe process via pipes and processes commands, including file manipulation (.put, .get) and timestamp changes (.ctm), and executes them within the shell environment.
The attackers also deployed a new Golang-based backdoor, GoClient, alongside the QSC framework, starting on October 17, 2023.
They used the Quarian backdoor to deploy the QSC framework and the GoClient backdoor, where the QSC framework was used to create services to launch the QSC framework loader DLLs.
While the GoClient backdoor was used to execute commands including collecting system information, disabling UAC remote restrictions, and compressing harvested data.
The attacker also used the QSC framework to discover domain controllers and other machines on the network.
After gaining access to the domain controller, the attacker used a tool called we.exe to perform pass-the-hash attacks to remotely execute commands and enumerate users.
Then they used WMIC to execute commands on the domain controller to obtain network configuration, create a shadow copy of the C: drive, steal the NTDS database, and store the collected information on the domain controller.
According to the Secure List, a lateral movement within the victim network was accomplished by the CloudComputing group through the utilization of the QSC framework.
Attackers utilized WMIC with stolen domain admin credentials to execute QSC framework components on multiple machines and communicated with a C2 server through internal pivot machines.
The group employed a custom tool, “pf.exe,” to forward traffic between internal and external C2 servers.
The presence of the Quarian backdoor, known to be used by CloudComputating, along with specific tools like TailorScan and StowProxy, further strengthens the attribution to this group.
Find this News Interesting! Follow us on Google News, LinkedIn, and X to Get Instant Updates!