A new phishing-as-a-service (PhaaS) named ‘Darcula’ uses 20,000 domains to spoof brands and steal credentials from Android and iPhone users in more than 100 countries.
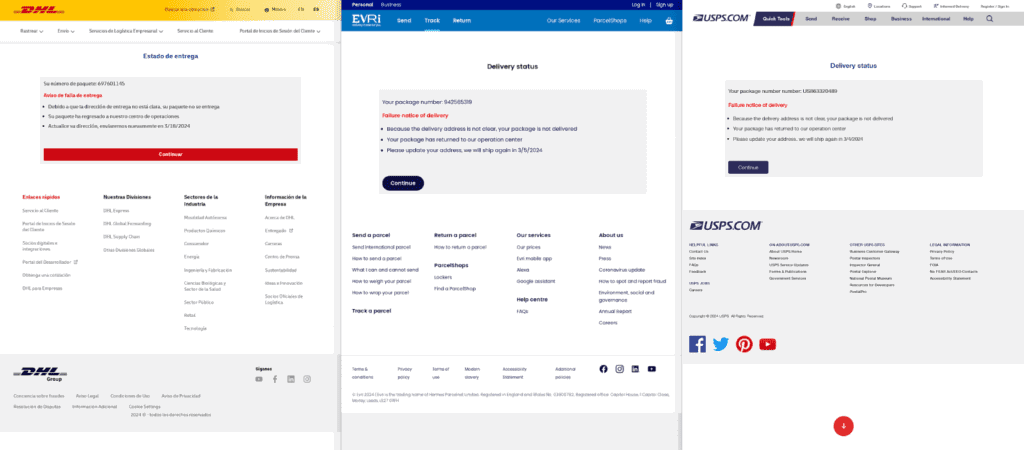
Darcula has been used against various services and organizations, from postal, financial, government, taxation departments, to telcos, airlines, utility, offering fraudsters over 200 templates to choose from.
One thing that makes the service stand out is that it approaches the targets using the Rich Communication Services (RCS) protocol for Google Messages and iMessage instead of SMS for sending phishing messages.
Darcula phishing service
Darcula was first documented last summer by security researcher Oshri Kalfon but Netcraft analysts report that the platform has been becoming more popular on the cybercrime space, and was recently used in several high-profile cases.
Unlike traditional phishing methods, Darcula employs modern technologies like JavaScript, React, Docker, and Harbor, enabling continuous updates and new feature additions without clients needing to reinstall the phishing kits.
The phishing kit offers 200 phishing templates that impersonate brands and organizations in more than 100 countries. The landing pages are high-quality and use the correct local language, logos, and content.
The fraudsters select a brand to impersonate and run a setup script that installs the corresponding phishing site and its management dashboard directly into a Docker environment.
The system uses the open-source container registry Harbor to host the Docker image, while the phishing sites are developed using React.
The researchers say that Darcula service typically uses “.top” and “.com” top-level domains to host purpose-registered domains for the phishing attacks, while roughly one-third of those are backed by Cloudflare.
Netcraft has mapped 20,000 Darcula domains across 11,000 IP addresses, with 120 new domains being added daily.
Abandoning SMS
Darcula diverges from traditional SMS-based tactics and instead utilizes RCS (Android) and iMessage (iOS) to send victims messages with links to the phishing URL.
The advantage from this is that the recipients are more likely to perceive the communication as legitimate, trusting the additional safeguards that aren’t available in SMS.
Moreover, since RCS and iMessage support end-to-end encryption, it is impossible to intercept and block phishing messages based on their content.
Netcraft comments that recent global legislation efforts aimed at curbing SMS-based cybercrime by blocking suspicious messages are likely pushing PhaaS platforms towards alternative protocols such as RCS and iMessage.
However, these protocols come with their own sets of restrictions that cybercriminals have to overcome.
For example, Apple bans accounts sending high volumes of messages to multiple recipients, and Google recently implemented a restriction preventing rooted Android devices from sending or receiving RCS messages.
.png)
The cybercriminals attempt to override these limitations by creating multiple Apple IDs and using device farms to send a small number of messages from each device.
A more challenging obstacle is a safeguard in iMessage that only allows recipients to click on a URL link if they have replied to the message.
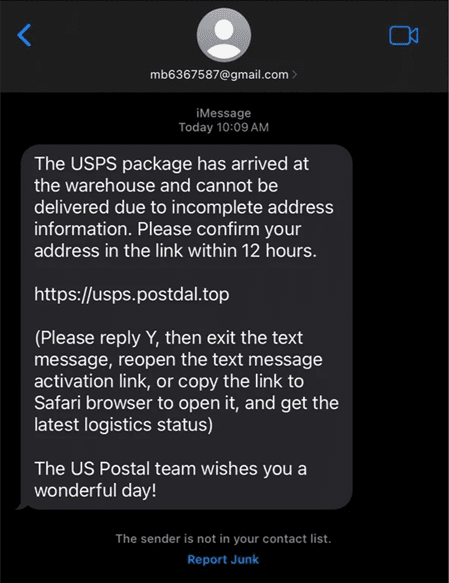
To go around this measure, the phishing message instructs the recipient to reply with a ‘Y’ or ‘1’ and then reopen the message to follow the link. This process may create friction that could reduce the effectiveness of the phishing attack.
Users should treat all incoming messages urging them to click on URLs with suspicion, especially if the sender is not recognized. Regardless of the platform or app, phishing threat actors will keep experimenting with new delivery methods.
Netcraft researchers also recommend paying attention at inaccurate grammar, spelling errors, overly attractive offers, or calls to urgent actions.







