New Golang-based Zergeca Botnet appeared in the threat landscape

Researchers uncovered a new Golang-based botnet called Zergeca that can carry out distributed denial-of-service (DDoS) attacks.
Researchers at the QiAnXin XLab team uncovered a new Golang-based botnet called Zergeca that can carry out distributed denial-of-service (DDoS) attacks.
On May, 2024, the researchers detected a suspicious ELF file at /usr/bin/geomi that was uploaded from Russia to VirusTotal. The file was packed with a modified UPX and had a unique magic number, 0x30219101, however, it wasn’t flagged as malicious. A similar file was uploaded from Germany the same day. The experts discovered multiple uploads from different countries. The analysis revealed the file to be a Golang-based botnet. The botnet was named “Zergeca” due to its C2 string “ootheca,” reminiscent of the Zerg swarming in StarCraft.
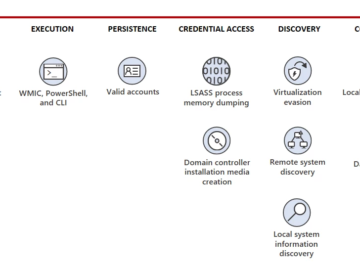
The DDoS botnet Zergeca supports six attack methods and implements additional functionalities such as proxying, scanning, self-upgrading, persistence, file transfer, reverse shell, and collecting sensitive device information. Unique features include multiple DNS resolution methods, prioritizing DNS over HTTPS (DoH) for command and control (C2) resolution, and using the uncommon Smux library for C2 communication, encrypted via XOR
The analysis revealed that Zergeca’s C2 IP address, 84[.]54.51.82, has been associated with at least two Mirai botnets since September 2023. The researchers speculate that the author of Zergeca likely gained experience from operating Mirai botnets.
From early to mid-June 2024, the botnet was used to launch DDoS attacks on organizations in Canada, the United States, and Germany. The main type of attack was ackFlood (atk_4), the experts noticed that the victims were distributed across multiple countries and different ASNs.

The botnet’s functionality is implemented through four distinct modules, respectively named as persistence, proxy, silivaccine, and zombie.
The silivaccine module allows to bot to remove competing malware, while the module ‘zombie’ implements the full botnet functionality. The zombie module reports sensitive information from the compromised device to the C2 and awaits commands, it supports six types of DDoS attacks, scanning, reverse shell, and other functions.
“Functionally, it can be broken down into four distinct modules. The persistence and proxy modules are self-explanatory, with the former ensuring persistence and the latter handling proxying.” reads the report published by the QiAnXin XLab team. “The silivaccine module is used to remove competing malware, ensuring exclusive control over the device. The most crucial module is zombie, which implements the full botnet functionality. It reports sensitive information from the compromised device to the C2 and awaits commands from the C2, supporting six types of DDoS attacks, scanning, reverse shell, and other functions.”
Zergeca maintains persistence on compromised devices by adding a system service geomi.service. The service allows the bot to automatically generates a new geomi process if the device restarts or the process is terminated.
“Through reverse analysis, we gained initial insights into Zergeca’s author. The built-in competitor list shows familiarity with common Linux threats. Techniques like modified UPX packing, XOR encryption for sensitive strings, and using DoH to hide C2 resolution demonstrate a strong understanding of evasion tactics.” concludes. “Implementing the network protocol with Smux showcases their development skills. Given this combination of operational knowledge, evasion tactics, and development expertise, encountering more of their work in the future would not be surprising.“
Pierluigi Paganini
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, botnet)