A previously unknown campaign involving the Hotabot botnet malware has targeted Spanish-speaking users in Latin America since at least November 2020, infecting them with a banking trojan and spam tool.
The malware enables the operators to take control of the victim’s Gmail, Outlook, Hotmail, or Yahoo email accounts, steal email data and 2FA codes arriving in the inbox, and send phishing emails from the compromised accounts.
The new Horabot operation was discovered by analysts at Cisco Talos, who report that the threat actor behind it is likely based in Brazil.
Starts with phishing
The multi-stage infection chain begins with a tax-themed phishing email sent to the target, with an HTML attachment that is supposedly a payment receipt.
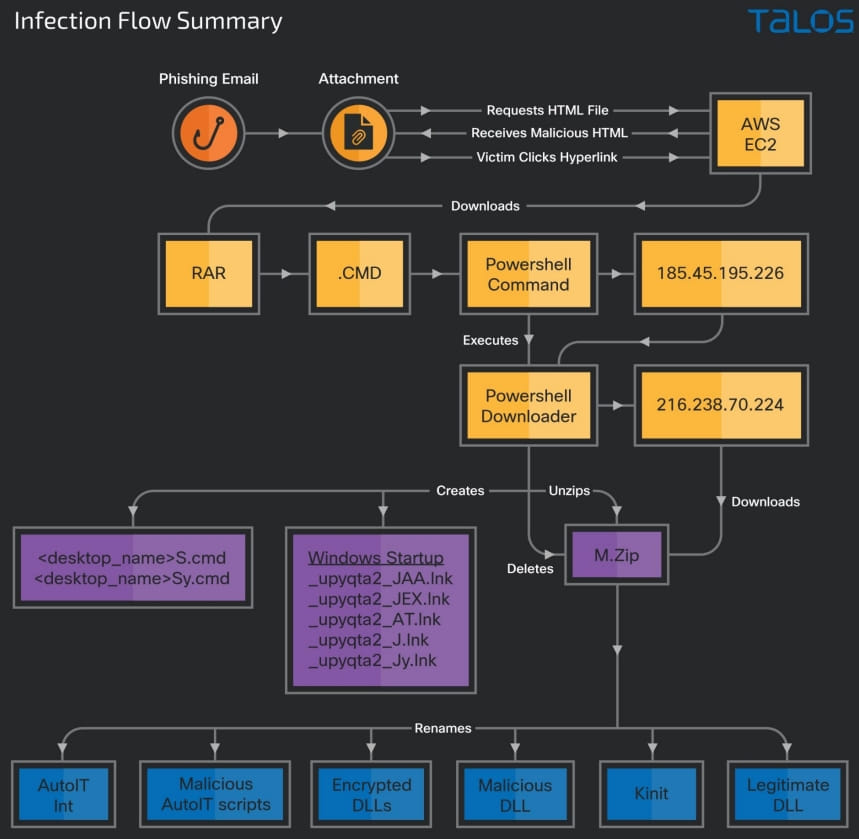
Opening the HTML launches a URL redirection chain that lands the victim on an HTML page hosted on an attacker-controlled AWS instance.
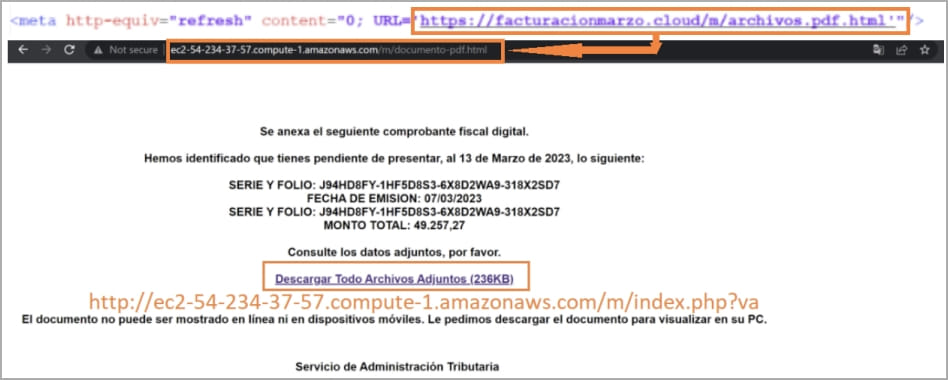
The victim clicks on the hyperlink on the page and downloads a RAR archive that contains a batch file with a CMD extension, which downloads a PowerShell script that fetches trojan DLLs and a set of legitimate executables from the C2 server.
These trojans execute to fetch the final two payloads from a different C2 server. One is a PowerShell downloader script, and the other is the Horabot binary.
Banking trojan
One of the DLL files in the downloaded ZIP, “jli.dll,” which is sideloaded by the “kinit.exe” executable, is a banking trojan written in Delphi.
It targets system info (language, disk size, antivirus software, hostname, OS version, IP address), user credentials, and activity data.
Moreover, the trojan also offers its operators remote access capabilities like performing file actions and can also conduct keylogging, screenshot snapping, and mouse event tracking.
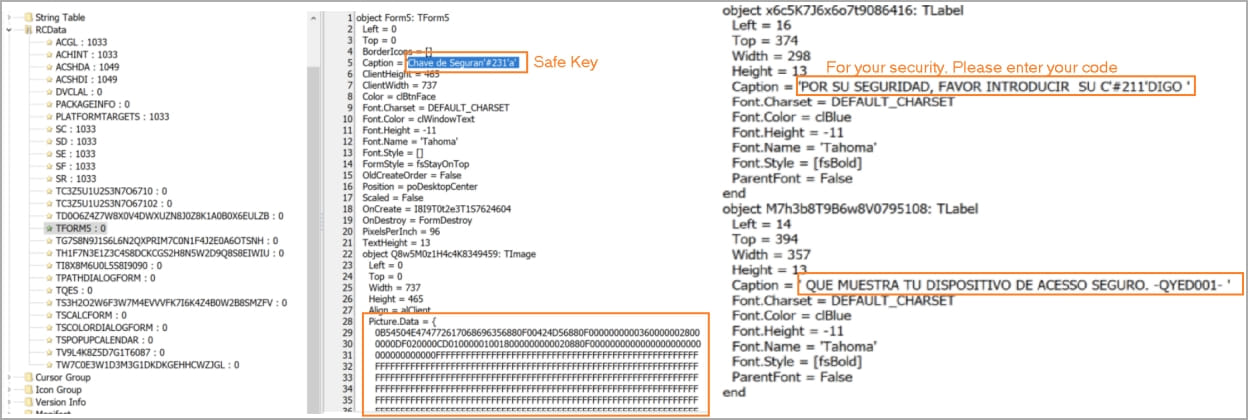
When the victim opens an application, the trojan overlays a fake window on top of it to trick victims into entering sensitive data like online banking account credentials or one-time codes.
All information collected from the victim’s computer is sent to the attacker’s command and control server via HTTP POST requests.
Cisco explains that the trojan has several built-in anti-analysis mechanisms to prevent it from running in sandboxes or alongside debuggers.
The ZIP archive also contains an encrypted spam tool DLL named “_upyqta2_J.mdat,” designed to steal credentials for popular webmail services like Gmail, Hotmail, and Yahoo.
Once the credentials are compromised, the tool takes over the victim’s email account, generates spam emails, and sends them to the contacts found in the victim’s mailbox, furthering the infection somewhat randomly.
This tool also features keylogging, screenshot snapping, and mouse event interception or tracking capabilities, functionally overlapping with the banking trojan, possibly for redundancy.
Horabot
The primary payload dropped onto the victim’s system is Horabot, a documented PowerShell-based botnet that targets the victim’s Outlook mailboxes to steal contacts and disseminate phishing emails containing malicious HTML attachments.
The malware launches the victim’s desktop Outlook application to scrutinize the address book and contacts from the mailbox contents.
“After initialization, the [Horabot] script looks for the Outlook data files from the victim profile’s Outlook application data folder,” explains Cisco in the report.
“It enumerates all folders and emails in the victim’s Outlook data file and extracts email addresses from the emails’ sender, recipients, CC, and BCC fields.”
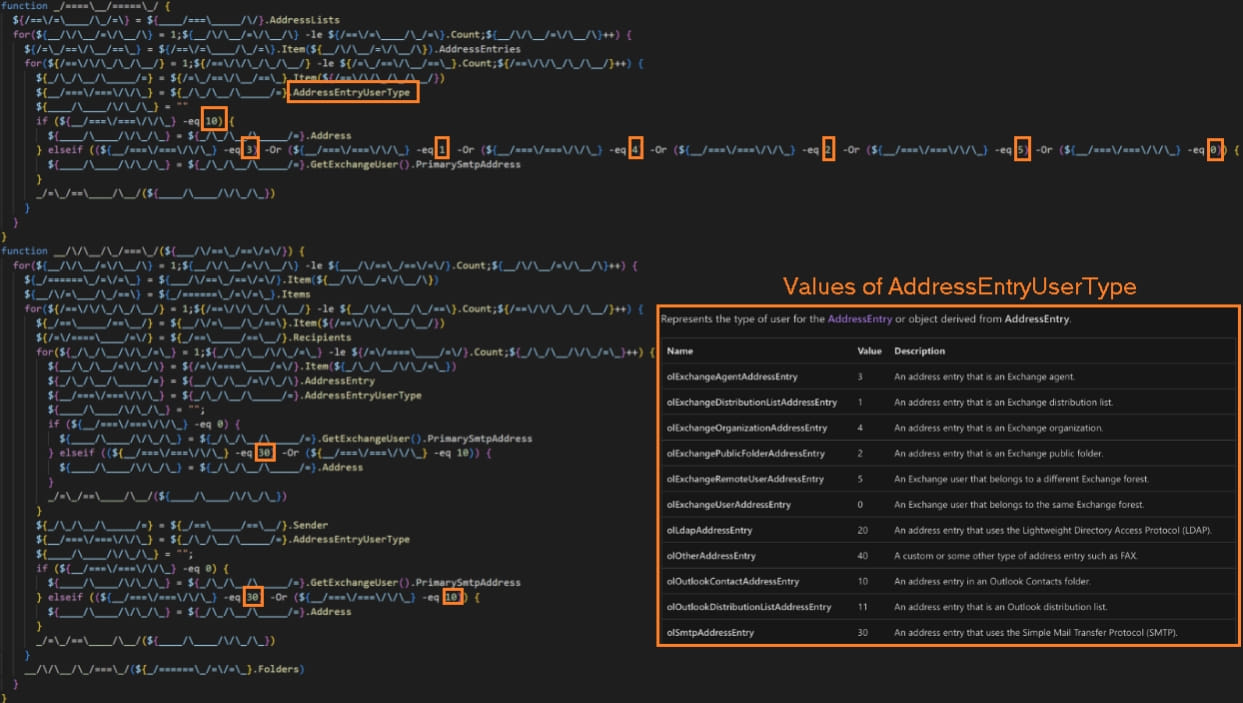
All extracted email addresses are written into an “.Outlook” file and then encoded and exfiltrated to the C2 server.
Finally, the malware creates an HTML file locally, fills it with content copied from an external resource, and sends phishing emails to all extracted email addresses individually.
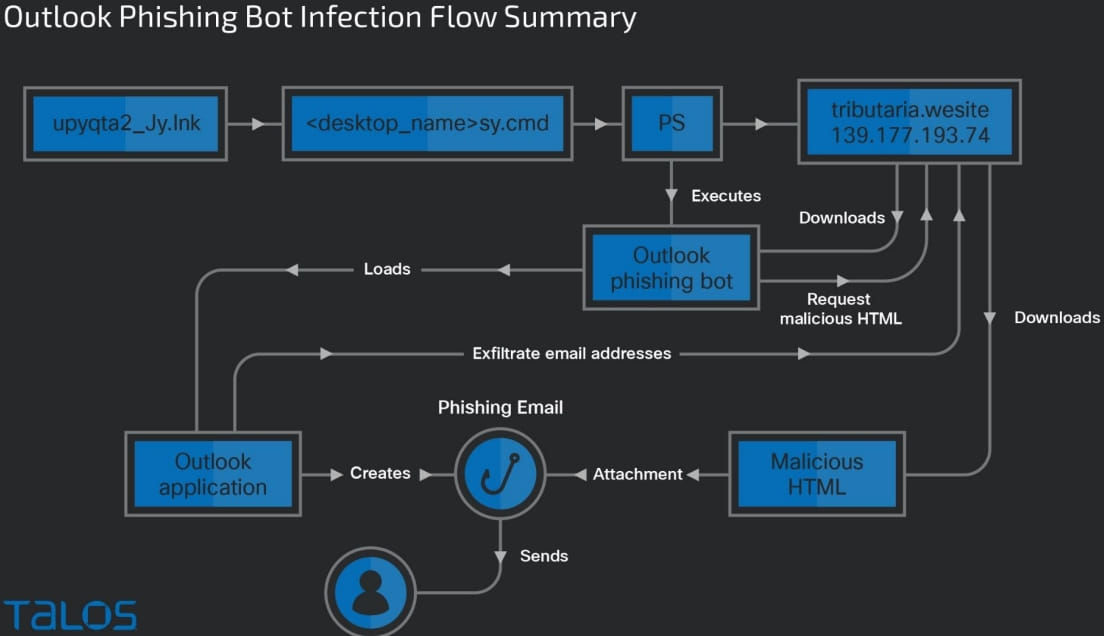
When the phishing email distribution process is finished, the locally created files and folders are deleted to wipe any traces.
Although this Horabot campaign mainly targets users in Mexico, Uruguay, Brazil, Venezuela, Argentina, Guatemala, and Panama, the same or collaborating threat actors could expand its reach to other markets anytime, using phishing themes written in English.




