A hacking group tracked as ‘UAC-0184’ was observed utilizing steganographic image files to deliver the Remcos remote access trojan (RAT) onto the systems of a Ukrainian entity operating in Finland.
UAC-0184 are threat actors Trend Micro saw carrying out attacks in late 2023 against the Armed Forces of Ukraine, also using the same malware.
The threat group’s latest activity, which started in early January 2024 and was spotted by Morphisec analysts, illustrates that they have expanded to target organizations outside of Ukraine that are affiliated with their strategic target.
Morphisec opted not to provide technical information or specific details about the victim due to confidentiality but still shared some data on the employed attack methods.
Using images for loading malware
Steganography is a well-documented but rarely seen tactic that involves encoding malicious code into the pixel data of images to evade detection by solutions using signature-based rules.
Typically, the small payload chunks in the image pixels do not result in an altered image appearance, but in the case seen by Morphisec, the image looks visibly distorted.
This distortion, however, would only be damaging for the attackers in the case of manual inspection, and assuming there’s none, it still works in evading detection from automated security products.
The attack chain observed by Morphisec starts with a carefully crafted phishing email supposedly from Ukraine’s 3rd Separate Assault Brigade or the Israel Defense Forces.
Tricked recipients opening the shortcut file attachment trigger an infection chain that launches an executable (DockerSystem_Gzv3.exe), which in turn activates a modular malware loader named ‘IDAT.’
“Distinguished by its modular architecture, IDAT employs unique features like code injection and execution modules, setting it apart from conventional loaders,” describes Morphisec.
“It employs sophisticated techniques such as dynamic loading of Windows API functions, HTTP connectivity tests, process blocklists, and syscalls to evade detection.”
To remain stealthy, API calls aren’t written in the code in plaintext form but are instead resolved at runtime using a decryption key that is part of the attack chain.
IDAT extracts the encoded payload that is embedded in the malicious PNG image file and then decrypts and executes it in memory, a process that involves multiple stages and additional modules that are injected into legitimate processes (Explorer.exe) and DLL files (PLA.dll).
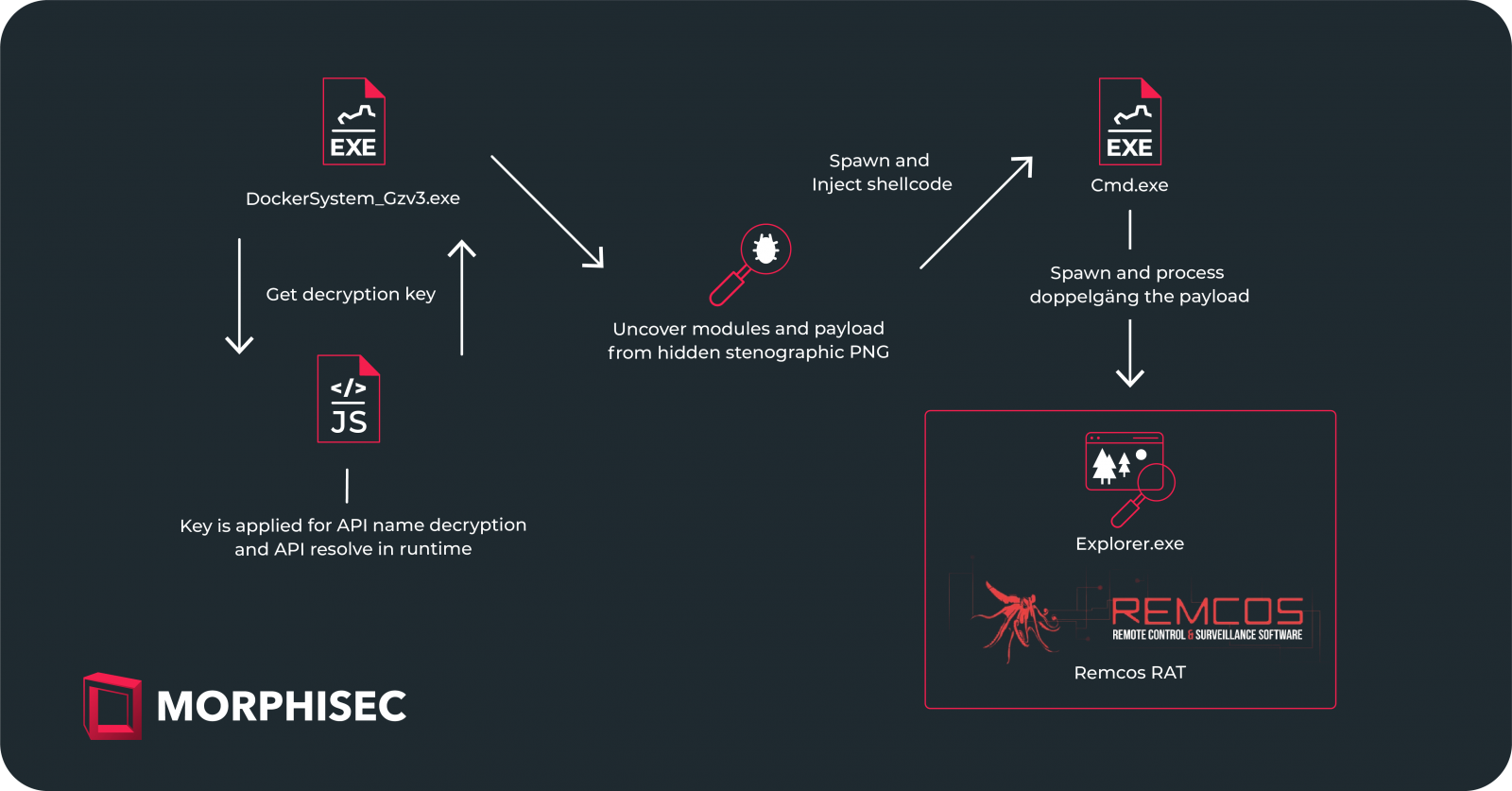
The final stage involves the decryption and execution of the Remcos RAT, a commodity malware that hackers employ as a backdoor on compromised systems, allowing stealthy data theft and victim activity monitoring.
Morphisec says IDAT also delivers malware like Danabot, SystemBC, and RedLine Stealer, but it is unclear if these families were seen in the Finland-based computers or in different attacks.
The complete list of the indicators of compromise (IoC) for this campaign can be found in this report by CERT-UA.