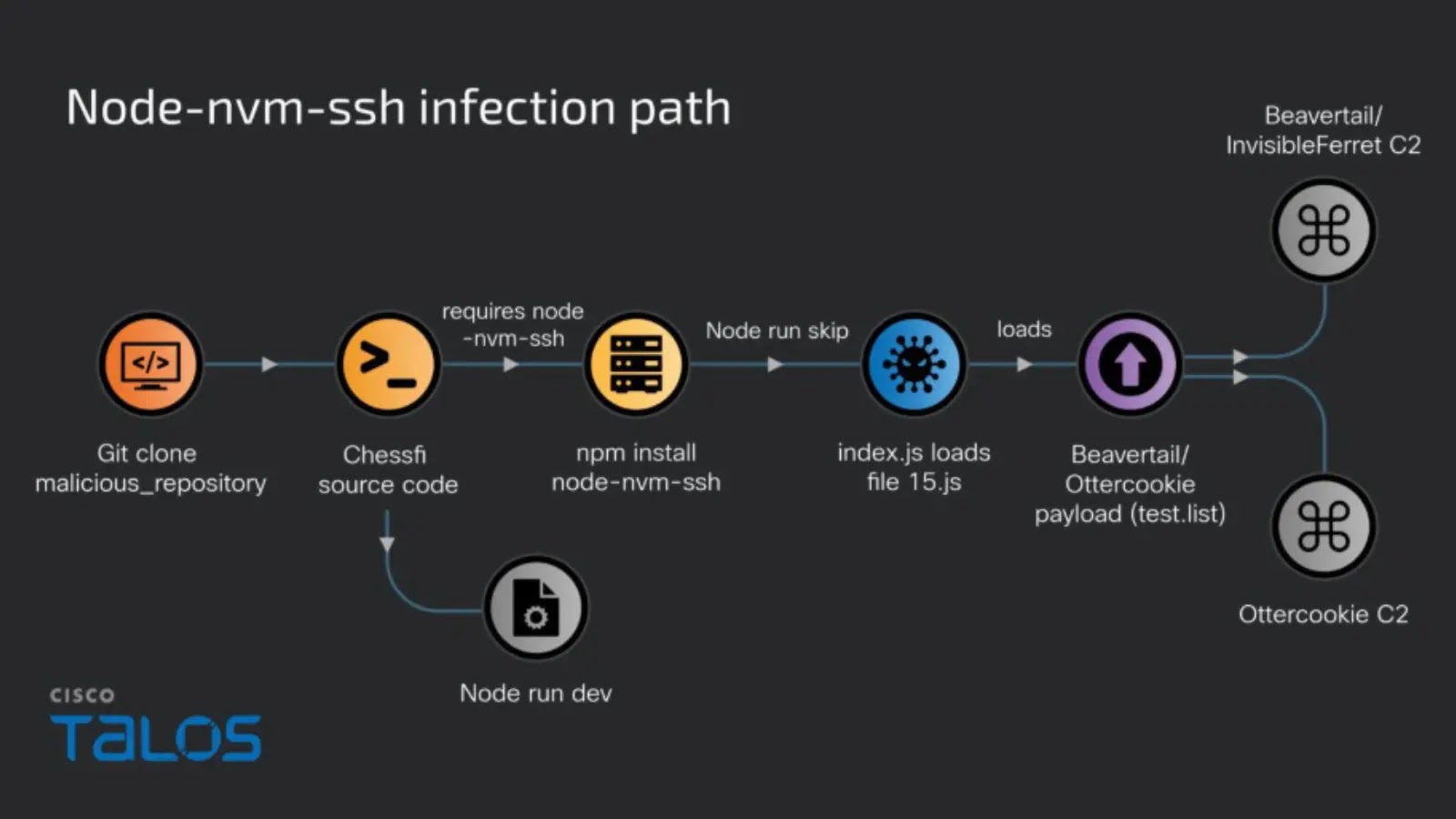
The investigation began with the detection of two scanning IP addresses, 91.238.181[.]225 and 5.188.86[.]169 sharing a common Secure Shell (SSH) fingerprint (b5:4c:ce:68:9e:91:39:e8:24:b6:e5:1a:84:a7:a1:03).
Cybersecurity researchers have uncovered a sophisticated multi-stage malware campaign that leverages malicious Windows LNK shortcut files to deploy the REMCOS backdoor, a potent remote access trojan capable of full system compromise.
This fingerprint led to the identification of an expanded network of 138 servers through reconnaissance tools like Shodan and Fofa, highlighting a broader infrastructure potentially tied to the campaign’s command-and-control (C2) operations.
Discovery Through Network Probes
The attack chain, often initiated via phishing emails or malicious downloads, disguises the LNK file as innocuous documents such as invoices or Word files, exploiting Windows’ default behavior of hiding file extensions to deceive users.
Upon execution, the shortcut triggers a hidden PowerShell command that downloads and decodes a Base64-encoded payload, ultimately installing the REMCOS backdoor for persistent access, keystroke logging, and data exfiltration.
In this campaign, the malicious LNK file, named “ORDINE-DI-ACQUIST-7263535” with SHA-256 hash 506ecb76cf8e39743ec06129d81873f0e4c1ebfe7a352fc5874d0fc60cc1d7c6, invokes powershell.exe with a concealed command-line argument.
This argument uses System.Net.WebClient to fetch a Base64-encoded file from the domain shipping-hr.ro/m/r/r.txt, saving it as HEW.GIF in the hidden C:ProgramData directory.
The script then decodes this content into a binary executable disguised as CHROME.PIF, a PIF file mimicking a Chrome-related program but functioning as an MS-DOS executable.
Upon launch, CHROME.PIF (SHA-256: 5ec8268a5995a1fac3530acafe4a10eab73c08b03cabb5d76154a7d693085cc2) drops additional artifacts, including Xufewgoz.url for persistence via shortcuts and a batch file [.].cmd, while creating a mutex to ensure single-instance execution.
Payload Behavior
Static analysis reveals the payload as a PE image-based MS-DOS program that hooks into user32.dll via SetWindowsHookExA to implement a keylogger, capturing inputs and storing them in %ProgramData%remcoslogs.dat alongside screenshots and system logs.
Network communications establish C2 connections to IPs like 92.82.184[.]33 (Romania, associated with shipping-hr.ro via TLSv1.2) and 198.23.251.10 (United States, linked to mal289re1.es), enabling REMCOS’s core capabilities: arbitrary command execution, file transfers, webcam/microphone captures, and remote control over TCP with a custom binary protocol.
According to the report, this fileless approach evades traditional detection by running payloads in memory, abusing trusted tools like PowerShell and mshta.exe, and hiding malicious commands in LNK properties such as icon paths or alternate data streams.

The campaign’s stealth stems from its social engineering tactics, bypassing macro warnings common in Office-based attacks, and exploiting user trust in familiar file types.
For removal, experts recommend booting into Safe Mode with Networking and scanning with tools like UltraAV, which detects it as a Trojan.WinLNK.Powershell_S03, followed by manual checks of Task Scheduler, registry run keys, and startup folders to delete suspicious files like CHROME.PIF.
Prevention emphasizes real-time antivirus protection, avoiding untrusted attachments, and monitoring system performance via Task Manager.
As malicious LNK files evolve, this attack underscores the need for vigilance against seemingly harmless shortcuts from emails or network shares, with potential for widespread compromise if not addressed promptly.
Indicators of Compromise (IOCs)
| Type | Indicator | Description |
|---|---|---|
| File Name | ORDINE-DI-ACQUIST-7263535 | Malicious LNK file |
| SHA-256 | 506ecb76cf8e39743ec06129d81873f0e4c1ebfe7a352fc5874d0fc60cc1d7c6 | LNK file hash |
| File Name | CHROME.PIF | Payload file |
| SHA-256 | 5ec8268a5995a1fac3530acafe4a10eab73c08b03cabb5d76154a7d693085cc2 | Payload hash |
| File Name | HEW.GIF | Downloaded encoded file |
| SHA-256 | 8bc668fd08aecd53747de6ea83ccc439bdf21b6d9edf2acafd7df1a45837a4e1 | Encoded file hash |
| URL | https://shipping-hr.ro/m/r/r.txt | Download source |
| IP Address | 92.82.184[.]33 | C2 server (Romania) |
| IP Address | 198.23.251[.]10 | C2 server (USA) |
| Domain | shipping-hr.ro | Resolved to 92.82.184.33 |
| Domain | mal289re1.es | Resolved to 198.23.251.10 |
| File Path | %ProgramData%remcoslogs.dat | Keylogger log file |
| IP Address | 91.238.181[.]225 | Scanning probe IP |
| IP Address | 5.188.86[.]169 | Scanning probe IP |
| SSH Fingerprint | b5:4c:ce:68:9e:91:39:e8:24:b6:e5:1a:84:a7:a1:03 | Common probe fingerprint |
Find this News Interesting! Follow us on Google News, LinkedIn, and X to Get Instant Updates!