A relatively new ransomware operation known as Nevada seems to grow its capabilities quickly as security researchers noticed improved functionality for the locker targeting Windows and VMware ESXi systems.
Nevada ransomware started to be promoted on the RAMP darknet forums on December 10, 2022, inviting Russian and Chinese-speaking cybercriminals to join it for an 85% cut from paid ransoms.
For those affiliates who bring in a lot of victims, Nevada say they will increase their revenue share to 90%.
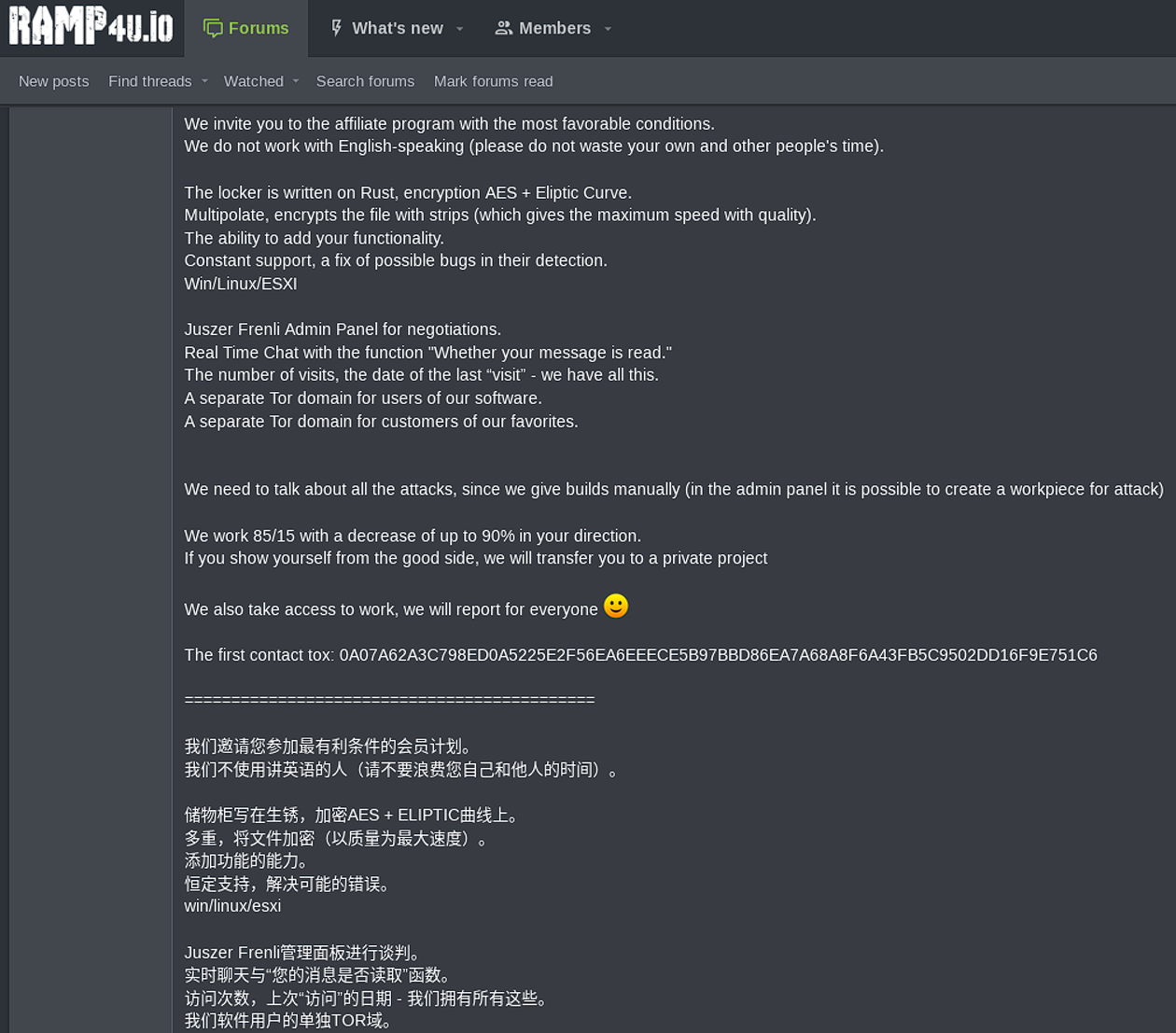
RAMP has been previously reported as a space where Russian and Chinese hackers promote their cybercrime operations or to communicate with peers.
Nevada ransomware features a Rust-based locker, real-time negotiation chat portal, separate domains in the Tor network for affiliates and victims.
.png)
Resecurity researchers analyzed the new malware and published a report on their findings. They say that while Nevada ransomware is explicit about excluding English-speaking affiliates, the operators are open to doing business with vetted access brokers from anywhere.
Targeting Windows hosts
The Nevada ransomware variant that focuses on Windows machines is executed via console and supports a set of flags that give its operators some control over the encryption:
- -file > encrypt selected file
- -dir > encrypt selected directory
- -sd > self delete after everything done
- -sc > delete shadow copies
- -lhd > load hidden drives
- -nd > find and encrypt network shares
- -sm > safe mode encryption
One interesting characteristic of Nevada ransomware is the set of system locales it spares from the encryption process. Typically, ransomware gangs exclude victims in Russia and CIS (Commonwealth of Independent States) countries. With this malware, the list extends to Albania, Hungary, Vietnam, Malaysia, Thailand, Turkey, and Iran.
The payload uses MPR.dll to collect information about network resources, adding shared directories in the encryption queue. Each drive, including hidden ones, is assigned a letter, and all files in them are added to the queue too.
After this stage, the encryptor is installed as a service, and then the breached system reboots into Windows safe mode with an active network connection.
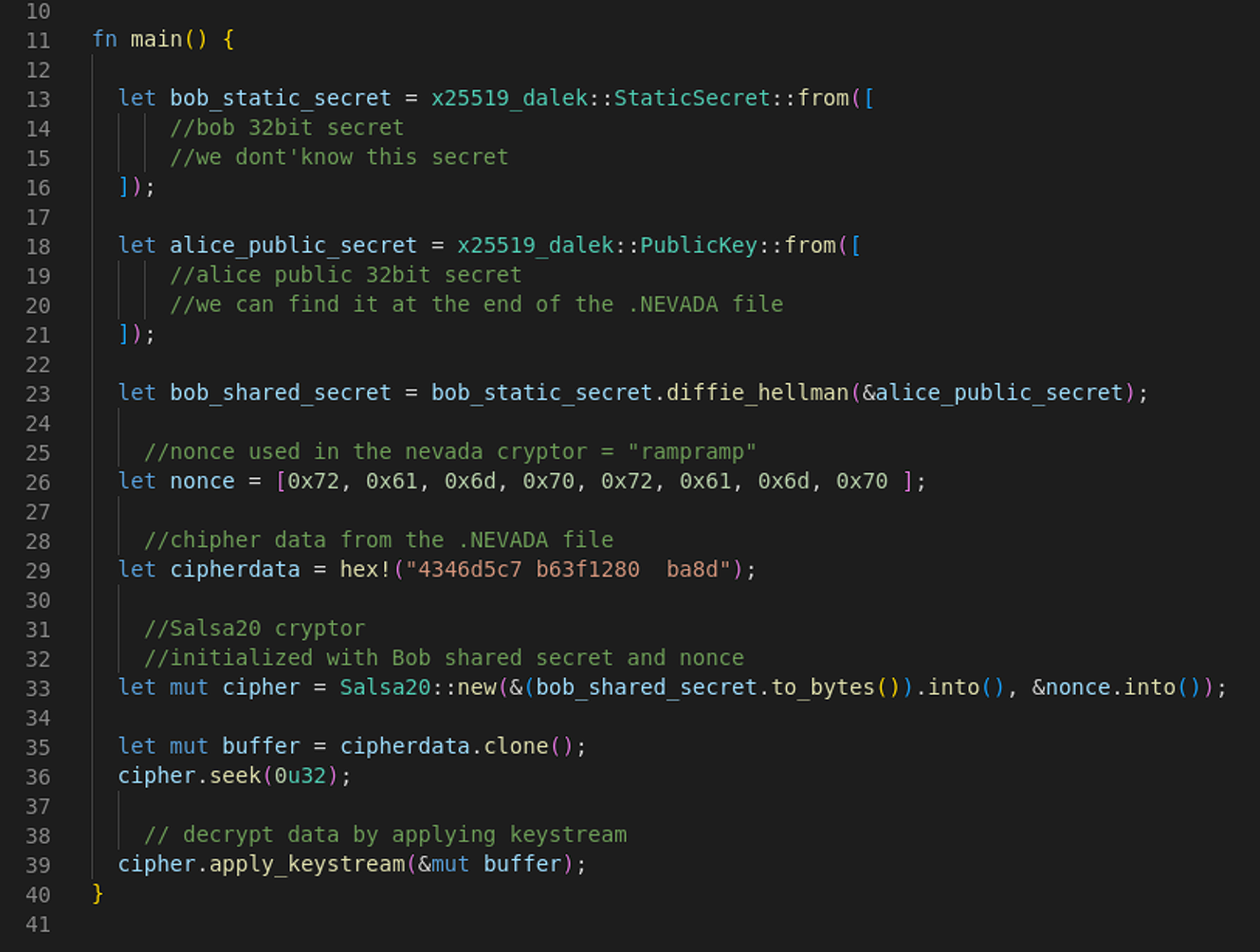
The locker uses the Salsa20 algorithm to perform intermittent encryption on files larger than 512KB for quicker encryption.
Executables, DLLs, LNKs, SCRs, URLs, and INI files in Windows system folders and the user’s Program Files are excluded from encryption to avoid rendering the victim host unbootable.
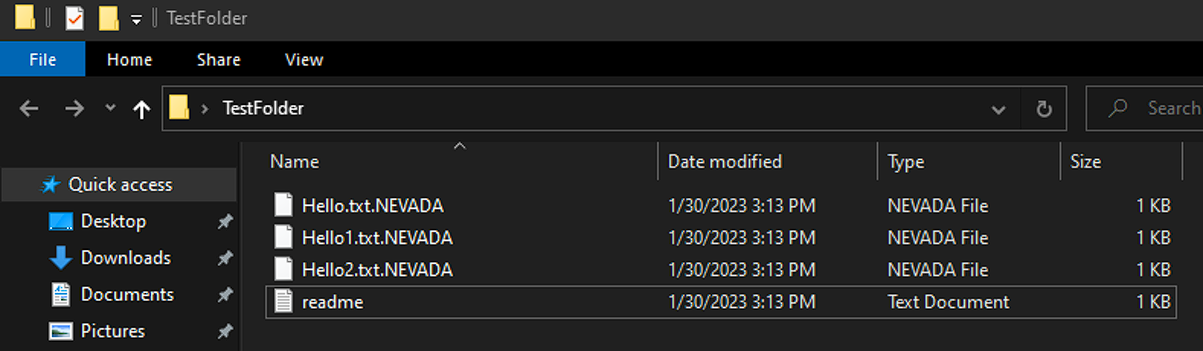
Encrypted files are appended the “.NEVADA” file extension and each folder hosts a ransom note that gives victims five days to meet the threat actor’s demands, else their stolen data would be published on Nevada’s data leak website.
.png)
Targeting VMware ESXi systems
The Linux/VMware ESXi version of Nevada ransomware uses the same encryption algorithm (Salsa20) as the Windows variant. It relies on a constant variable, an approach previously seen in Petya ransomware.
The Linux encryptor follows the same intermittent encryption system. fully encrypting only files smaller than 512KB.
Likely due to a bug in the Linux version, Nevada ransomware will skip all files sized between 512KB and 1.25MB, the researcher discovered.
The Linux locker supports the following arguments:
- -help > help
- -daemon > creation and launch of a ‘nevada’ service
- -file > encrypt particular file
- -dir > encrypt particular folder
- -esxi > disable all virtual machines
On Linux systems, the public key is stored at the end of the encrypted file in the form of an additional 38 bytes.
Resecurity says that similarities shared with Petya ransomware extend to encryption implementation bugs that might make it possible to retrieve the private key too, which would allow recovering the data without paying the ransom.
Nevada ransomware is still building its network of affiliates and initial access brokers, looking for skillful hackers.
Resecurity observed Nevada ransomware operators buying access to compromised endpoints and engaging a dedicated post-exploitation team to perform the intrusion.
The researchers note that this threat seems to continue its growth and should be closely monitored.







